Certificate-based smart cards have been one of the most trusted and proven implementations of multi-factor authentication for over 20 years. There’s only one problem… the typical credit card-shaped smart card didn’t work well, if at all, on mobile devices without additional hardware and software.
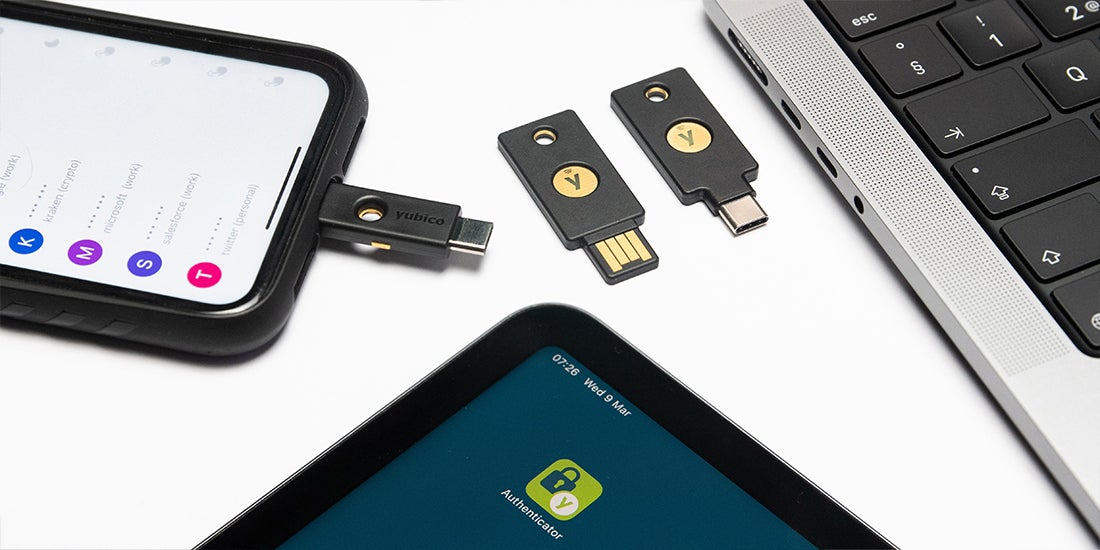
Today, smart cards come in many form factors, from a credit card size that fits in your wallet to a hardware security key that fits on your keychain. With the portability and multi-protocol support offered by Yubico’s security keys, it’s now possible to use any personal identity verification (PIV)-enabled YubiKey on any supported iOS device as a certificate-based smart card.
As of iOS 14.2, Apple provides native support for smart cards, enabling any PIV-compatible smart card to interact with an iPhone without any additional hardware readers or software. The YubiKey 5 Series key is ideal as a smart card on iOS because it provides hardware-backed security and portable credentials, supports the PIV standard, and can communicate with any Apple device physically over the Lightning connector or wirelessly over NFC.
Recently, the Office of Management and Budget (OMB) also released a memo requiring federal agencies to meet security requirements to adopt phishing-resistant MFA. Smart cards meet this requirement, including the YubiKey 5 FIPS Series which enables government agencies and regulated industries to meet the highest authenticator assurance level 3 (AAL3) requirements. In this post, we’ll review what a smart card is, the capabilities and advantages of using a YubiKey as a smart card, and how the YubiKey interacts with the Yubico Authenticator app on iOS to support use cases like certificate-based authentication for clients, signing email, or decrypting messages and documents on any iOS device.
What Is a Smart Card?
A generic smart card is just a physical device that comes in various sizes and shapes (from a key to a card) and has a computer chip with an embedded secure element. The secure element allows for storing, retrieving, and sending information securely. The most common types of these smart cards are bank ATM cards, e-passports, and global ID cards.
PIV Smart Card
For the purposes of this post, we focus on Personal Identity Verification (PIV) smart cards compliant with the PIV standards at NIST. With a PIV-compatible smart card, there is increased assurance that all electronic communications, data storage, and data retrieval will be more secure and better protected.
The most common usage of a PIV smart card is the Common Access Card (CAC) issued to all members of the United States Armed Forces (since 2018) for identification, physical access, and credentialed access to secure computer networks and systems.
YubiKey as a smart card
The YubiKey is well known as a strong two-factor, multi-factor, and passwordless authenticator. Unbeknownst to many, it’s also a PIV-compatible Smart Card. All YubiKey 5 Series keys provide smart card functionality based on the PIV interface. This means the YubiKey can deliver the same cryptographic functionality (as a PIV-compatible CAC) for identity verification, physical access, and credentialed access to secure computer networks and systems.
Derived PIV Credential
The United States government has been issuing smart cards for over 20 years, so what’s changed and why now? Along with the recent Apple changes to the way iOS devices interact with a smart card, the NIST guidelines have also greatly improved the usability of electronic authentication via mobile devices through the approved use of derived PIV credentials.
Authorization of derived PIV credentials means that these credentials and the associated private key can now be provisioned onto the PIV-compatible secure element of a FIPS Series YubiKey. The private key corresponding to a derived PIV credential can thus be stored in a cryptographic module in an alternate form factor in addition to a government-issued PIV credit card style.
The YubiKey advantage
The advantages of using the YubiKey as a smart card are the portability, smaller form factor, and its ability to communicate with iOS devices via Lightning connector and contactless (NFC) interfaces without requiring additional card readers or software.
Within the PIV-compatible smart card module of the YubiKey, you can store multiple digital certificates in individual slots for a variety of different use cases. Each of the PIV slots in the smart card module of the YubiKey is capable of holding an X.509 certificate, together with its accompanying private key.
Remember, for holders of derived PIV credentials or those needing a NIST assurance level, the YubiKey FIPS series key is a PIV-compliant FIPS 140-2 validated smart card that meets the requirements for achieving the highest authenticator assurance level 3 (AAL3) of NIST SP800-63B guidance.
Yubico Authenticator
Yubico Authenticator for iOS is an authenticator app that adds a layer of security for mobile and desktop users. The Yubico Authenticator app was originally designed to interface with the OATH-TOTP module of the YubiKey for one-time passcodes as a form of 2nd factor authentication.
As of version 1.6, the Yubico Authenticator app for iOS allows a YubiKey smart card to interact with X.509 certificates on the PIV module over the Lightning connector or NFC.
When using your YubiKey as a smart card on iOS, the Yubico Authenticator app is an essential tool providing two functions:
First, it provides the intuitive user interaction for extracting the public portion of your certificate(s) on the YubiKey and placing it into the iOS keychain, thereby making the certificate available to any native app like the Safari browser, the Mail app, or any 3rd party app.
The second function of the authenticator app is to interact with the YubiKey over Lightning or NFC during authentication, signing, or decryption. This is the 2nd factor part where you enter your PIV PIN to allow interaction with the private key during authentication.
Why is the Yubico Authenticator app necessary?
The authenticator app integrates the new Apple APIs for interacting with a digital certificate on a smart card as if the certificate was installed on the device. The iOS device and native apps are looking for a reference to a certificate that can be used for authentication or other cryptographic operations.
Let’s take a look at how this all works.
How it all works
Now that we have a better understanding of YubiKey as a smart card on iOS and how it works with the Yubico Authenticator app, let’s dive into a demo of how this all works.
With remote work exploding and a continually expanding attack surface in both public and private sectors, there are increasing needs and requirements to provide secure mobile authentication. To address those changing needs and requirements, developers are moving away from username + password authentication and moving towards two-factor authentication (2FA). However, we need strong hardware-backed 2FA solutions.
Let’s say that you are working remotely and need to securely access corporate resources from any device and any location. Instead of authenticating to a website via username + password and a 2FA code via SMS, you are given a YubiKey with a PIV certificate to access corporate resources. In this scenario, the YubiKey as a smart card completes the requirements for strong 2FA by providing something you have (a hardware-backed security key protecting your certificate) and something you know, which is the PIN code required to protect your PIV credentials on the YubiKey.
To demonstrate this scenario, we’ll use a publicly available X.509 certificate, a PIV-compatible YubiKey, YubiKey Manager desktop tool, and the Yubico Authenticator app on an iOS device. We’ll use these tools and credentials and run through a simple certificate-based authentication scenario, satisfying the strong 2FA requirement. You can try this at home as we are using a downloadable certificate from badSSL.com, placing it onto a YubiKey, and then authenticating via the Safari browser to a website that is protected by the certificate.
This entire process shown in the video is documented in more detail in the Yubico Smart card on iOS guide.
To use the YubiKey as a Smart Card on iOS feature as shown in the demo, you must have the following (all prerequisites are discussed in the Yubico guide here):
- Apple iPhone or iPad (Lightning connector only) with iOS/iPadOS 14.2 or later.
- A YubiKey 5 Series key (5Ci, 5C NFC, or 5 NFC).
- Yubico Authenticator iOS app (v.1.6 or newer).
- YubiKey Manager GUI or CLI tool. Download for MacOS, Windows, or Linux.
- X.509 smart card certificate capable of PIV authentication.
What’s next?
Certificates and smart cards have been around for decades through various hardware and software solutions for desktop but now we are seeing a huge shift to mobile as these proven strong cryptographic technologies are now accessible to anyone with an iOS device and a YubiKey.
With the latest PIV compatible smart card integrations on iOS and the updated derived credentials requirements satisfied by FIPS 140-2 validated YubiKeys, a whole host of use cases have been unlocked.