Hardware authentication reimagined
Stop account takeovers in their tracks with easy-to-use authentication
Not all MFA is created equal
We know traditional authentication methods haven’t always been the most user-friendly. In fact, did you know that 59% of people still rely on username and password to authenticate?* This method has proven to not be effective against bad actors, which is why we created the YubiKey—it makes logging into your accounts simple and secure.
Here’s how YubiKeys have changed the game for secure login

YubiKeys and Security Keys:
- Are easy to use—simply touch the YubiKey to verify and you’re in. Provide modern, phishing-resistant MFA
- Are reliable and can be set up in minutes
- Eliminate the need to reach for your phone to open an app, or memorizing and typing in a code—simply touch the YubiKey to verify and you’re in
- Are trusted—You don’t need to use the YubiKey every time you log in. Once an app or service is verified, it can stay verified. It’s that easy
- Use NFC for mobile authentication
- Option to leave plugged into your laptop or USB hub
- Are a rugged and durable solution (even survives the washing machine!)
- Don’t require batteries, WiFi or network connection
- Start at a low cost of $29 USD
Enterprises that eliminate passwords report better business and security outcomes
New research finds organizations using passwordless technologies experience the fewest phishing attacks, are more productive and achieve greater levels of employee satisfaction.

Securing a new device made easy
Did you know that, within the last 2 years, nearly 40% of people admit to having broken their mobile phone and nearly 30% have lost it (a device individuals and organizations commonly use to authenticate).*
With the YubiKey, there’s no hassle! No matter what device you use, the YubiKey provides:
- Your portable root of trust that provides secure access to your accounts from desktops, laptops, tablets and smartphones seamlessly, instead of having to rely on a phone for authentication
- A simplified strong authentication solution when onboarding new devices
- Strong protection for your credentials as they reside on something that isn’t tied to any system or server
- Ability to register multiple keys with most services providing you with a primary and a backup key
Securing employees made easy
With employees busier than ever, 9 out of 10 cybersecurity breaches are caused by their mistakes** and what’s more, over 54% of employees are not required to go through cybersecurity training on a frequent basis.*
The YubiKey protects from human error by eliminating “MFA fatigue”. Remove the guesswork and ensure your employees, and only your employees, are the ones getting in.
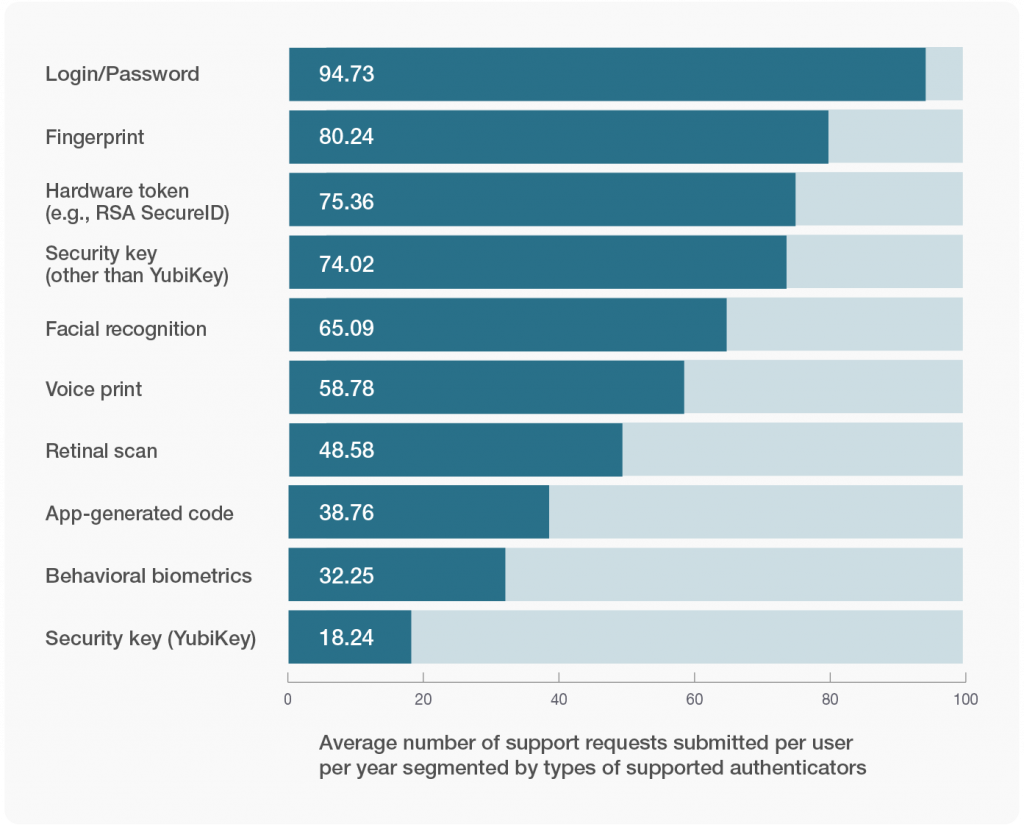
Low friction authentication = reduced support
Authentication needs to be easy, but also the highest level of security. The YubiKey achieves both. In a study by EMA, surveyed businesses using YubiKeys reported they received the lowest frequency of support tickets, taking a massive burden off of support teams when compared to basic and legacy MFA methods.
Convenient login made easy
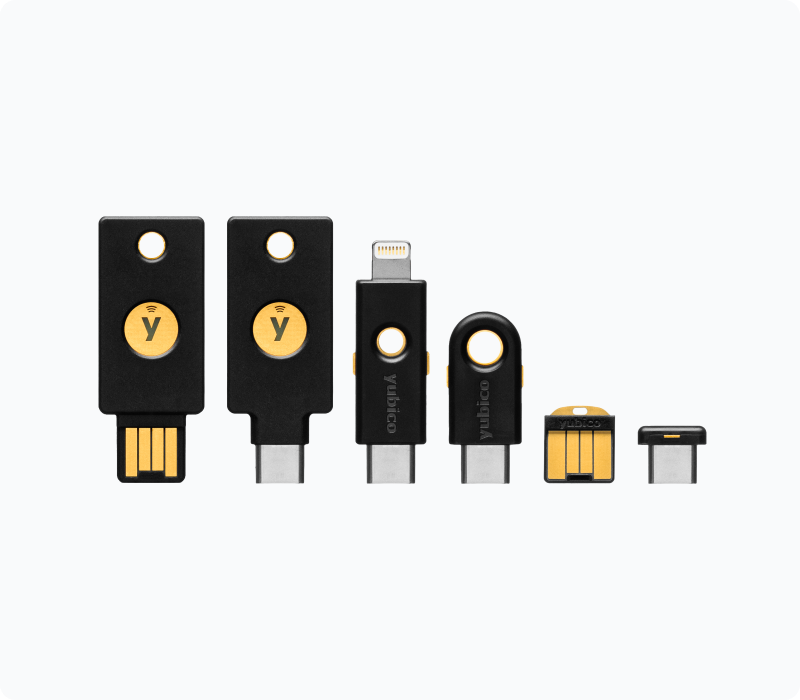
The YubiKey is built to fit your authentication needs. The devices come in many different form factors, all offer the same level of authentication protocol support and touch to activate convenience—It’s that simple!
Benefits include:
- YubiKeys in keychain form factors give you the option to carry the keys on your keychain just like you would a house or car key
- YubiKey Nano form factors allow you to keep it your device USB port, so it’s a simple tap when you want to authenticate
- Connections for USB-A, USB-C, Lightning and NFC

Lost key? Retrieval made easy
A question we get often is: What happens if I lose my key? No need to worry—we’ve got solutions!
- As best practice, we recommend having a primary key and a backup key registered to your accounts (just like you would with a car or house key)
- We also have our Yubico Authenticator app that can generate codes for logging into services

By deploying the YubiKey across their organization, Google was able to reduce help desk calls by 92%, and has not experienced a single account takeover since deploying the keys.

Learn how Hyatt hotel’s use of the YubiKey protects critical guest information, enhances their overall security posture and delivers improved customer experiences.

Following a sizable internal breach, Twitter turned to YubiEnterprise Delivery and YubiEnterprise Subscription services to distribute YubiKeys across their global workforce.
Ready to get started?
Are you an enterprise?
Learn more about how simple it is to deploy the YubiKey across your organization.
Are you an individual?
Looking to step up your security game? We’ll help you find the right key.
Get protected today!
Join customers in over 160 countries who are protecting their accounts with the YubiKey.
Risk reduction, business growth, and efficiency enabled by YubiKeys
A recent Forrester Consulting Total Economic Impact™ (TEI) study commissioned by Yubico found that a composite organization representative of interviewed customers who use YubiKeys reduced risk of successful phishing and credential theft attacks by 99.9%, saw a drop in password-related helpdesk tickets by 75%, and experienced a 203% 3-year ROI with YubiKeys.
BUT…. all organizations are different. Enter your own company data to create a custom Dynamic TEI study and instantly see how Yubico’s solutions can help your organization!
- *Survey ‘Yubico’s State of Global Enterprise Authentication Survey 2022’ from Yubico and Censuswide
- **Study “Psychology of Human Error” from Stanford University Professor Jeff Hancock and security firm Tessian
- ***Research Report ‘The Rise of Low-Friction Access Emerging Requirements and Solutions for Boosting Workforce Productivity and Security Assurance’ from Yubico and Enterprise Management Association (EMA)