Protect against cyber security threats in manufacturing
Simple and cost-effective phishing-resistant authentication at scale
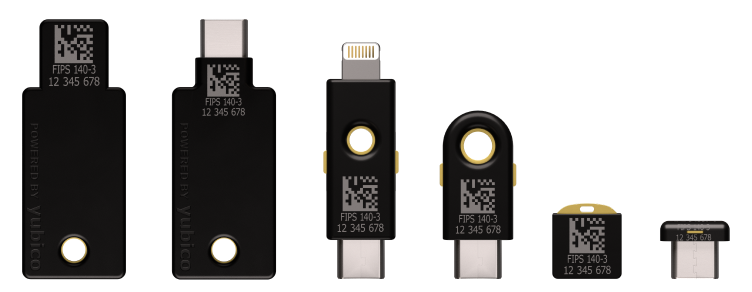
The YubiKey 5 FIPS Series will be FIPS 140-3 validated soon.
Accelerate Zero Trust with phishing-resistant authentication and hardware-backed security for manufacturers

Manufacturers of all kinds are being targeted by ransomware and phishing at an alarming rate. While multi-factor authentication (MFA) can be a strong first-line defense, not all forms of MFA are created equal to protect against account takeovers.
To protect against cyber security threats in manufacturing, you need an authentication solution to: navigate legacy infrastructure, restrictive production floor requirements, protect informational technology (IT), operational technology (OT), and industrial control systems (ICS), while enabling the move to stronger phishing-resistant methods either: Smart Card/PIV or FIDO.
There is increased urgency to adopt phishing-resistant MFA and cryptographic protection to ensure that no user or device is allowed into your network unless vetted. Even the Cybersecurity and Infrastructure Security Agency (CISA) and the National Security Agency (NSA) are recommending phishing-resistant authentication for all critical infrastructure sectors, including manufacturing.
Yubico solutions and services meet you where you are on the cybersecurity journey, while paving the way to a modern phishing-resistant authentication infrastructure. Secure your digital transformation and stop account takeovers with Yubico.
High-tech
(silicon & semiconductor)

Retail
Machinery
Medical

Energy

Transportation
(aerospace & automotive)
Protect people, data, and critical infrastructure against cyber security threats in manufacturing
Phishing-resistant authentication and cryptographic protection provides robust security at scale and accelerates Zero Trust

The YubiKey for phishing-resistant multi-factor and passwordless authentication, secures data and user access to critical IT, OT, and ICS systems.
- Simple to use a device-bound passkey with no battery or cellular connection needed
- IP68 certified and FIPS 140-2 validated to support any environment from industrial to highly regulated
- Provides multi-protocol support easily protecting existing systems while modernizing your infrastructure

The ultra-portable YubiHSM 2, provides cryptographic protection for servers, applications and computing devices.
- FIPS 140-2 validated to support highly regulated environments
- Ultra-portable with an innovative ‘nano’ form-factor that allows for flexible deployment
- Cost-effective by ensuring enterprise-grade high cryptographic security and operations without the traditional HSM price tag

WHITE PAPER
Protecting manufacturing with highest-assurance security
Learn the critical need to modernize MFA, authentication best practices, secure the supply chain, and ensure product integrity with the YubiKey and the YubiHSM 2.
Customer Spotlight:
Schneider Electric enhances global supply chain security
Yubico’s solutions enable Schneider Electric system operators to complete critical actions in power operations systems and also protect their supply chain.
See real stories of how global manufacturers and other leading brands changed the game for modern enterprise security

“By leveraging YubiKeys and the YubiHSM, a small formfactor and powerful hardware security module, we increase the security of our supply chain at Schneider Electric.“
Chad Lloyd
Director of Cybersecurity Architecture for Energy Management Schneider Electric

“YubiKeys are fast, robust and best-in-class: a best-in-class device and best-in-class security. It’s very smooth, and saves time compared to the people who have to enter the TOTP because you need to type six numbers, for every account. It’s much faster just to touch a key.”
Ángel Uruñuela
CISO for Fluidra Group

“The YubiKey is now used to log on and authenticate to our product, that’s part of what we mean by implementing stronger identity for our customers and partners. This will start with our cloud services and will make its way also into our various products as well.”
Christian Morin
Genetec CSO and Vice President of Integrations and Cloud Services
The Resilience Roadmap: Schneider Electric’s Strategy to Harden OT
Join Yubico and Schneider Electric in this webinar to explore how to bridge the gap between legacy infrastructure and a resilient future where post-quantum computing and AI are present. Learn how identity-centric security serves as the foundation for the next generation of industrial operations.

WEBINAR
Best practices to secure critical infrastructure with phishing-resistant MFA
Learn about the need for adopting phishing-resistant MFA to secure critical infrastructure and deployment best practices gathered from numerous global deployments across variety of sectors.
Benefits of Yubico solutions to protect against cyber security threats in manufacturing

Reduce IT support costs and drive high ROI
The combination of frictionless user experience, data breach prevention, mobile device and service cost savings, and the YubiKey’s versatility with multi-protocol support results in high ROI.
With flexible procurement and deployment options through YubiEnterprise Subscription, you can experience an estimated 203% ROI over three years and a reduction of password-related help desk support tickets by 75% by year 3. YubiKeys:
- Enable self-service password resets, eliminating IT support costs related to help desk password-reset requests.
- Are future-proof security investments, by acting as a bridge to modern authentication protocols and enabling secure passwordless login.
- Support the following protocols: FIDO U2F, WebAuthn/FIDO2 (passkeys), OTP/TOTP, OpenPGP and Smart Card/PIV.

Secure manufacturing assembly lines and the supply chain around the world
With supply chain integrity becoming increasingly paramount, manufacturing organizations are turning to Yubico to protect their supply chain and intellectual property, ranging from sensors and medical devices, to automotive and other products with electronic components.
- The YubiKeys offer secure, convenient, and scalable security making it easy for you and your supply chain vendors to deploy strong authentication.
- The YubiHSM 2 is built to safeguard corporate secrets and secure manufacturing assembly lines.
With YubiEnterprise Delivery from Yubico, it’s easy for your supply chain to get security keys directly into the hands of their users.

Secure shared workstations, mobile-restricted areas, and cloud services
YubiKeys are extremely portable and simple to use, increasing employee productivity. They offer fast, tap-and-go passwordless login that is 4x faster than login with SMS. A single YubiKey conveniently works across multiple devices including desktops, laptops, mobile, tablets, notebooks and shared workstations/kiosks.
YubiKeys integrate seamlessly with existing IAM solutions such as Microsoft, Okta, Duo and Ping, and provide secure authentication for hundreds of applications and services. With 1,000+ integrations your users can use them out of the box with all the apps and services they love.

Ensure compliance to global regulations
As a result of evolving cyber attacks, regulatory changes such as National Institute of Standards and Technology (NIST) SP 800-63-3, IEC 62443 Security for Industrial Automation and Control Systems, EU Network and Information Security (NIS2) Directive and others continue to introduce new security requirements related to stronger multi-factor authentication, which passwords and legacy authenticators can no longer fulfill.
For regulated environments, the YubiKey and YubiHSM can help manufacturers comply with required and voluntary data security standards.
Let us help you create a custom plan for your business!
Ready to take the next step?

Find the right YubiKey
Contact our sales team for a personalized assessment of your company’s needs.
Learn how to get started
Check out the deployment best practices that can help to accelerate adoption of modern, phishing-resistant MFA at scale using the YubiKey.