Phishing-resistant MFA that stops modern cyberthreats. Trusted by the world’s largest brands.
Making the internet safer with modern authentication

Not all MFA is created equal
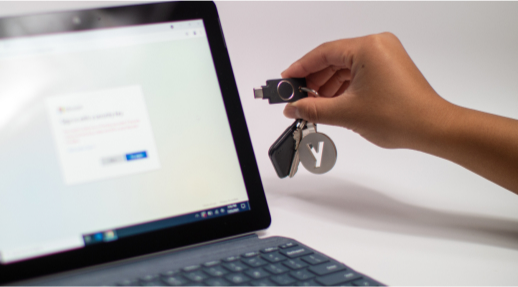
Stop phishing attacks and account takeovers before they start with modern, phishing-resistant multi-factor authentication (MFA). Stay ahead of evolving cyber threats and regulatory requirements with a proven solution which cannot be bypassed by malicious actors, unlike basic forms of MFA such as SMS, one-time passcodes and mobile authentication. Accelerate your zero trust strategy and gain a bridge to passwordless for enterprises, SMBs, individuals and developers.
We’re a force for good—against bad online actors
You deserve to collaborate and innovate across the internet while knowing you’re secure. That’s why Yubico co-created the FIDO authentication standards and made them open to drive an ecosystem of strong security across all platforms and services. And that’s why we’re trusted by regulatory bodies, government agencies and many of the most security-conscious organizations, individuals and industries around the world.
We make it easy to deploy modern,
hardware MFA at scale
Distributing YubiKeys and onboarding users is simple and seamless with our expert guidance, enterprise subscriptions and turnkey delivery services. With a tried and true process that hundreds of organizations have followed already, and with a ‘YubiKey as a Service’ model, it’s not a matter of if you’ll be successful but when you’ll be successful in raising your bar for security with modern, hardware-based security keys. No matter where you are on your MFA journey, we’ll meet you there.

Step 1 Plan
Ensure readiness and alignment ahead of execution

Step 2 Validate
Confirm the process with a small group of users before broader rollout

Step 3 Integrate
Ensure key apps and services are YubiKey-ready

Step 4 Launch
Distribute keys to users with turnkey delivery services or channel partners

Step 5 Adopt
Drive adoption with best practice training and support
Step 6 Measure
Report on security and business value impact

Our leading technology has 1,000+ integrations, meaning your users can use Yubico’s solutions out of the box with all the apps and services they love while keeping it simple for your IT team.
We know your organization is unique
Every organization has different business scenarios, third parties they work with and end users. Whether you’ve got shared workstations, remote employees, a sea of external vendors or high-value customers, Yubico’s solutions are flexible and agile. You’ll always have strong security that is right-sized for your evolving business needs.









We optimize your organization’s authentication security

Reduce credential threat risk by 1

Reduce IT/support tickets by 2

The YubiKey
YubiKey as a Service delivers enterprise-grade authentication with built-in Enrollment and Delivery services, helping organizations secure digital identities faster and at scale, for less than the cost of a cup of coffee per user, per month.

Yubico Hardware Security Module (HSM)
The world’s smallest HSM, YubiHSM 2, packs a lot of power, and offers game changing cryptographic protection for servers, applications and computing devices. Secure your public key infrastructure (PKI) environments, encrypt your files and databases and securely sign code or any digital artifact to raise the bar for security for your OT and IT systems.

YubiKey as a Service
YubiKey as a Service delivers enterprise-grade authentication with built-in Enrollment and Delivery services, helping organizations secure digital identities faster and at scale, for less than the cost of a cup of coffee per user, per month.
A team you can trust

Founded by Stina and Jakob Ehrensvard, Yubico is made up of a passionate, diverse workforce from around the world. We’re not just innovators—we enable you to bring your strong security vision to life to accelerate your business.
Protecting 4,000+ businesses & the world’s leading brands

Get started


1. Total Economic Impact of Yubico YubiKeys, Forrester Research, 2022
2. Ibid