Modern security for shared workstation environments
Secure users, applications, and data across shared workstations
and devices against modern cyber threats, using phishing-resistant MFA
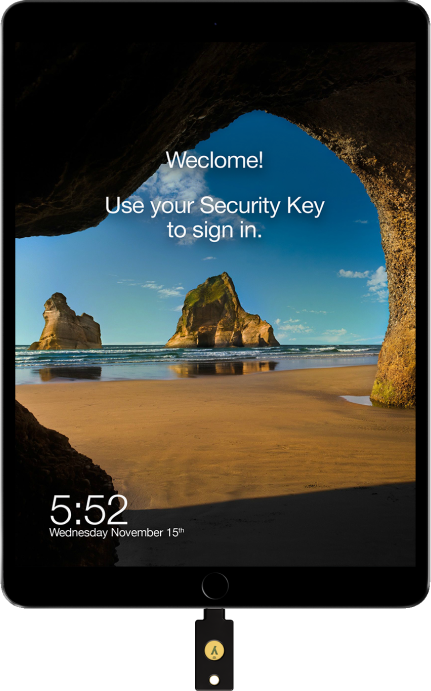
The ideal hardware security key for use across
shared workstations and devices
YubiKeys offer phishing-resistant MFA and an exceptional user experience in a
portable form factor, ensuring that your employees are always protected and productive.

Shared workstation environments such as shared kiosks, point-of-sale (POS) terminals, mobile-restricted areas, and grab-and-go devices are common across industries such as healthcare, financial services, retail, hospitality, manufacturing, energy, utilities, and education.
But shared workstations can be a high security risk if strong protection measures aren’t in place. High employee shift rotations, seasonal employees, and high turnover combined with the prevalence of password sharing and use of legacy MFA such as mobile authenticators, can put company and customer data at risk of being easily hacked.
Hyatt secures front-of-house shared workstations with the YubiKey
Hyatt Guest Services chose YubiKeys over mobile-based authenticators, for securing access to shared workstation front desk operations.
Using a YubiKey not only provides a more seamless experience for Hyatt Guest Services while keeping data safe, but also allows those colleagues to keep their cell phones stored away while performing guest-facing roles to provide the best customer experience.

Securing shared workstations against modern cyber threats
Read the white paper to learn how to achieve phishing-resistant MFA with exceptional UX across shared workstations and devices.
Let us help you create a custom plan for your business!
Secure critical and sensitive data across shared workstations
How do you secure shared workstations and devices with multiple rotating users, making sure both the user accounts are secure and that the users are gaining access to only the applications, services and data they should have access to?
The YubiKey provides phishing-resistant MFA in a portable form factor for users that need to securely authenticate across shared workstation environments.
A single YubiKey works across multiple shared devices including desktops, laptops, mobile, tablets, and notebooks, enabling users to utilize the same key as they navigate between devices, and helping you deploy phishing-resistant MFA at scale. YubiKeys are also easily re-programmed, making them suitable for rotating-shift and temporary workers across these environments.

Improve efficiency, enhance user experience, and increase productivity
Any authentication mechanism adopted for shared workstations should provide fast and easy authentication for employees, to avoid workflow disruption and unapproved workarounds. Not all forms of multi-factor authentication (MFA) offer the optimal balance of strong security with a fast and easy user experience that enables high productivity. Mobile authenticators typically increase the number of steps in the authentication process, requiring users to wait for SMS, OTP or push app codes.
The YubiKey offers strong MFA (multi-factor authentication) and passwordless authentication with just one touch or tap of the YubiKey, and is 4 times faster than typing in an OTP, ensuring that your users can quickly access the services they require—driving high productivity.
No batteries or network connection needed—YubiKeys with NFC capability are highly suitable for shared workstation environments such as call centers or manufacturing kiosks that have USB port restrictions (or OT environments that have ‘no spark’ or low voltage requirements).
Reduce IT support costs and drive high ROI
The combination of frictionless user experience, data breach prevention, mobile device and service cost savings, and the YubiKeys versatility with multi-protocol support results in high ROI for any shared workstation environment.
YubiKeys also enable self-service password resets, eliminating IT support costs related to help desk password-reset requests.
In addition to reducing risk by 99.9%, the YubiKey has been shown to drive a 203% 3-year ROI and a drop in password-related help desk tickets by 75%.
99.9%
Reduced risk
203%
3-year ROI
75%
Drop in password-related help desk tickets

Watch the webinar
How do you ensure high security across shared workstations without impacting employee productivity? Watch this webinar to learn critical authentication requirements for shared workstations and devices, and best practices to ensure your organization stays protected against modern threats.