Secure privileged access management with phishing-resistant MFA
Protect privileged users and accounts against phishing attacks and account takeovers
Zero account takeovers with the YubiKey

Privileged users are the most highly targeted users by cyber attackers as these users hold higher ‘privileges’ to critical and sensitive applications and data. These could be IT, security, network and database admins, as well as C-suite, HR, finance and marketing employees.
Securing privileged users across both IT and business with legacy authentication such as usernames and passwords or mobile-based authenticators, can put your organization at risk of being hacked. Usernames and passwords are easily hacked and while multi-factor authentication (MFA) can be a strong first-line of defense against phishing, account takeovers, and ransomware attacks, not all forms of MFA are created equal. SMS, OTP codes, and push notifications are highly susceptible to modern phishing attacks, malware, SIM swaps, and attacker-in-the-middle attacks.
Yubico offers the phishing-resistant YubiKey for highest-assurance multi-factor and passwordless authentication. YubiKeys stop phishing attacks and account takeovers 100% and are simple to deploy and use. They also help reduce IT help desk costs related to password resets by 75%.
Whether your privileged users are on-site, hybrid or remote, Yubico makes it easy to get keys directly into the hands of your users with YubiEnterprise Delivery, a cloud-based service that streamlines the distribution of YubiKeys to end-users, serving both domestic and international locations including residential addresses.

BeyondTrust enforces Zero Trust for privileged accounts using YubiKeys
“Attacks are becoming privileged-based, identity-based and pretty much every report reinforces that identity is the real number one problem. As a security company, we have to practice what we preach, use all of our own products, and have very strict controls on any type of privileged access within our environment. Once the YubiKey started to be adopted, it became a very strong case for the right way to do things to protect the organization.”

WHITE PAPER
The critical strong authentication need for privileged users
Read the Yubico white paper to learn who really is a privileged user, and industry best practices to secure your privileged users against phishing attacks and account takeovers.
Benefits from the phishing-resistant YubiKey

Modern, hardware-backed phishing-resistant security
Any software downloaded on a computer or phone is vulnerable to malware and hackers and legacy authentication such as usernames and passwords, and mobile-based authenticators rely on centralized servers with stored credentials that can be easily breached.
With the modern, phishing-resistant YubiKey, security is enhanced using strong hardware-based public key cryptography, similar to smart cards PKI technology. Private keys are securely stored on a separate secure chip on the YubiKey that cannot be exfiltrated. Additionally, the touch sensor on the YubiKey verifies that the user is a real human and the authentication is done with real intent, and is not triggered remotely by an attacker or trojan.

Exceptional user experience drives high productivity
Not all forms of MFA offer the optimal balance of strong security with a fast and easy user experience that enables high productivity. Mobile authenticators typically increase the number of steps in the authentication process, requiring users to wait for SMS, OTP or push app codes.
The YubiKey offers strong MFA and passwordless authentication with just one touch or tap of the YubiKey, and is 4 times faster than typing in an OTP, ensuring that your users can quickly access the services they need even without requiring a battery or a network connection—driving high productivity anytime and anyplace.

Easy to deploy and use
YubiKeys integrate seamlessly with existing identity and access management (IAM), identity provider (IDP) solutions, and privileged access management (PAM) solutions such as Microsoft, Okta, DUO, Ping, CyberArk, Axiad, Google, and work out-of-the-box with over 1,000 applications and services, making it easy to to get started.The YubiKeys‘ multi-protocol support for FIDO2, FIDO U2F, Smart Card, OTP and OpenPGP, ensures a seamless, single solution for both legacy and modern IT environments, as well as a bridge to a passwordless future.

Reduce IT support costs and drive high ROI
The combination of frictionless user experience, data breach prevention, mobile device and service cost savings, and the YubiKeys versatility with multi-protocol support results in high ROI. YubiKeys also enable self-service password resets, eliminating IT support costs related to help desk password-reset requests.
Yubico solutions, and flexible YubiKey procurement and deployment options through YubiEnterprise Subscription, you can experience an estimated 203% ROI over three years and, a reduction of password-related helpdesk support tickets by 75% by year 3.
Let us help you create a custom plan for your business!
Fluidra enhances its global workforce security with YubiKeys
“Return on investment in cybersecurity is a very complicated matter, but I would say the return is very good. We have a token that ensures maximum security for access to certain systems. That was the goal: we achieved it, easily and painlessly. And the product works very well.”


WEBINAR
Learn why securing users and accounts with phishing-resistant multi-factor authentication (MFA) is a critical need across the industry.
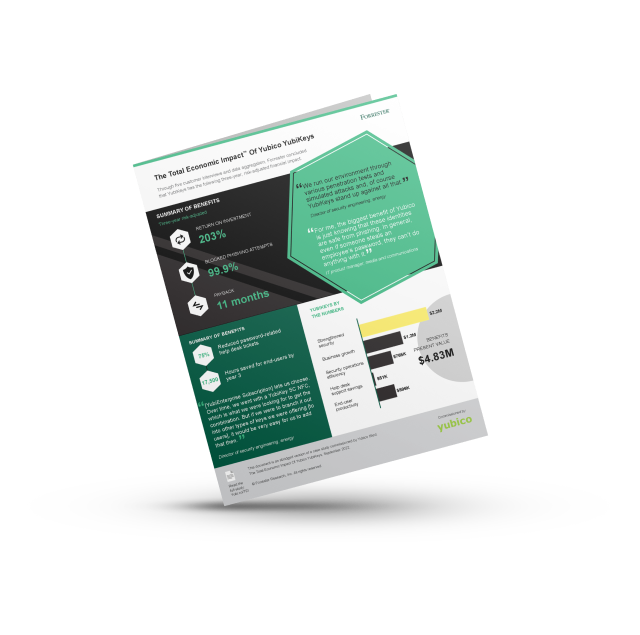
THE TOTAL ECONOMIC IMPACTTM OF YUBICO YUBIKEYS
Read the Forrester Consulting study commissioned by Yubico and see how a composite organization reduced risk by 99.9%, saw a drop in password-related tickets by 75%, and experienced a 203% 3-year ROI with YubiKeys.