Authentication without compromise
Unlock protection for your workforce of 500 users or more with phishing-resistant hardware MFA as a service. YubiEnterprise Subscription delivers flexibility and peace of mind in uncertain times.
The #1 security problem: stolen login credentials

Phishing and ransomware are on the rise and hackers easily bypass legacy MFA
SMS, and authentication software or security codes downloaded on a computer or phone are vulnerable to modern phishing and Man-in-the-Middle (MITM) attacks.
Underspending on addressing the human layer where most breaches start
Though global enterprise cybersecurity spending is in excess of $100B/year, the number of breaches are also increasing. And less than 10% is spent on addressing social engineering, realistic looking phishing emails and related tactics where 80% of breaches actually originate.


Path to phishing-resistant MFA and passwordless seems challenging
Moving away from weak passwords, SMS and other vulnerable methods is a journey. Many organizations are not aware that hardware authentication that offers the strongest security can be made easy with best practices and a service-based approach.
Hyatt Hotels is going passwordless
State of Global Enterprise Authentication Survey
Yubico’s exclusive research asks employees around the world how they authenticate. Discover the common mistakes that leave organizations vulnerable to attacks, hear from decision makers about the cybersecurity issues that keep them up at night, and learn how and why modern enterprises are embracing phishing-resistant MFA.
The YubiKey is the answer
Proven at scale
Thousands of companies and millions of end-users use YubiKey to simplify and secure logins to computers, internet services, and mobile apps. Our customers include 9 of the top 10 internet companies, 3 of the 5 leading financial and retails companies, and several of the largest governmental entities around the world.
Deploying YubiKeys in your organization? We can help


Strong Authentication at scale is here!
Now enterprises can benefit from improved cost efficiencies, predictable spending, flexible YubiKey upgrades, and turnkey delivery to corporate and residential addresses with YubiEnterprise Subscription, designed to accelerate your journey towards modern authentication and rapid protection for all your users.
Interested in YubiEnterprise Subscription? Learn more
Interested in YubiEnterprise Delivery? Learn more
Pioneering global standards
The first YubiKey launched in 2008, inspired by the word ubiquity and the vision of one security key to keep all of your online accounts safe. To make it happen, our founders moved from Sweden to Silicon Valley to spearhead a new global security standard, today supported by all the leading platforms and browsers.

Secure access with YubiKey

Computers
Insert your YubiKeys and touch it!

Mobile
Just tap it!
Why use a YubiKey?
Faster
Decrease time to authenticate by > 4x
More Value
Reduce support desk costs by > 90%
Strongest Security
No account takeovers when deployed fully
Trusted Production
Made in Sweden and USA; secrets controlled by customers
One Key to All
Access to nearly 1,000 apps and services with no shared secrets
Highly Robust
Water and crush-resistant; no network connection or batteries
Do you have more than 500 users?
Contact us about YubiEnterprise Subscription
Easy to deploy and manage across the enterprise
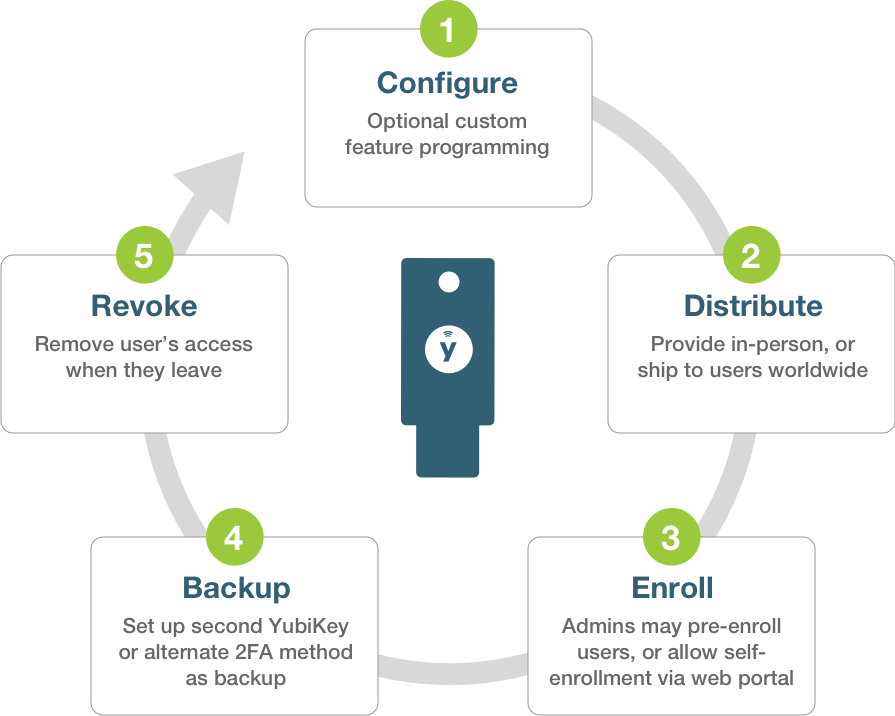
Not sure how to get started with an enterprise deployment? Check out our best practices
Let us help you create a custom plan for your business!
Protect your systems with YubiHSM
Did you know the YubiHSM 2 can protect your servers and applications? Give your team the world’s smallest but powerful and affordable Hardware Security Module (HSM) that offers Yubico’s hallmark security in the palm of your hand. Our HSMs are available in FIPS 140-2 validated and non-FIPS versions.
YubiKey protects the world’s leading brands