Tag: 2FA
-

What is 2 Step Verification? Learn the definition of 2 Step Verification and get answers to FAQs regarding: What is 2 Step Verification, Benefits of 2SV and 2SV vs 2FA. Read more -
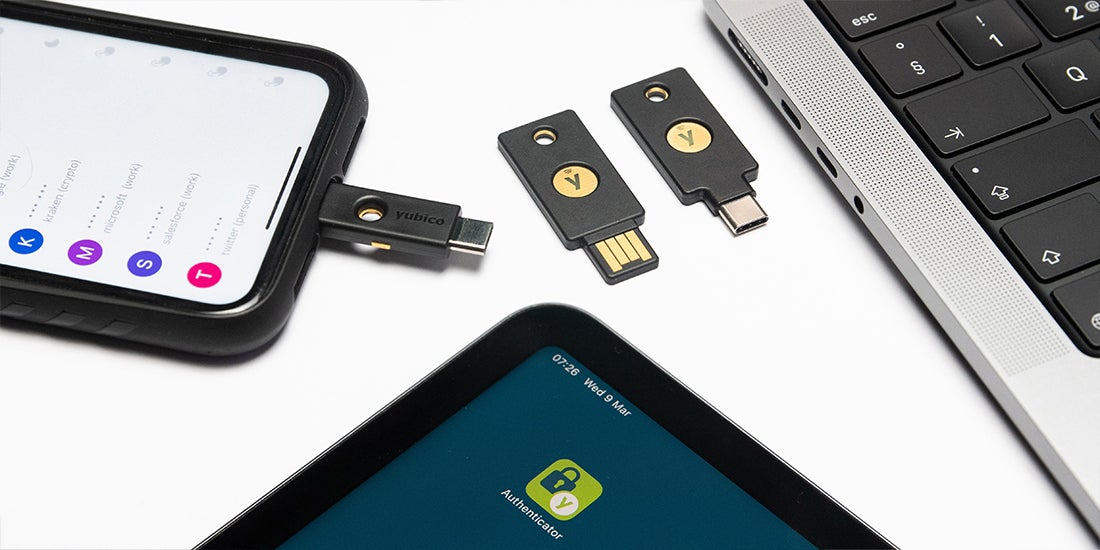
YubiKey as a smart card on iOS Certificate-based smart cards have been one of the most trusted and proven implementations of multi-factor authentication for over 20 years. There’s only one problem… the typical credit card-shaped smart card didn’t work well, if at all, on mobile devices without additional hardware and software. Today, smart cards come in many form factors, from a credit […] Read more -

Yubico for SMBs Get started with phishing-resistant YubiKey MFA for your favorite services and applications State of Global Enterprise Authentication Survey Yubico’s exclusive research asks employees around the world how they authenticate. Discover the common mistakes that leave organizations vulnerable to attacks, hear from decision makers about the cybersecurity issues that keep them up at night, and learn […] Read more -

A Day in the Life: Dispelling the Myths of Mobile Authentication COVID-19 initiated the most rapid digital transformation ever witnessed—organizations fast-tracked two-factor and multi-factor authentication to transition millions of employees to work from home. But with remote and hybrid work likely to continue in 2022 and beyond, it’s time to step back and ask: is my in-use authentication as secure as I think it is? Is […] Read more -

In passwordless authentication, who is holding the keys? Strong authentication practices are based on validating a number of authentication factors to a relying party (RP) or identity provider (IDP) to prove you are who the RP expects. Examples of relying parties could be Dropbox or Salesforce. Identity providers, who can also be a relying party that interacts with the authenticator, include Microsoft Entra […] Read more -

Making the internet safer for everyone, one YubiKey at a time When the internet was designed 30 years ago, security was not a priority as it was primarily created as a way to connect and easily share information with others around the world. Fast forward to today with news of hacks and breaches almost daily, much of the online world is trying to play catch up […] Read more -

Why Financial Services Shouldn’t Wait for Regulators to Address Strong Authentication Financial institutions face some of the most stringent and complex regulatory requirements, including financial service compliance requirements around authentication. So much so that the financial service industry is broadly considered the gold standard from a compliance perspective. To comply with existing regulations and thwart cyber attacks, financial institutions were early adopters of two-factor authentication (2FA) […] Read more -

What is Yubico OTP? How does Yubico verify Yubico OTPs? In order for Yubico OTP to work with YubiCloud (Yubico’s validation service) the information programmed into the YubiKey must also be uploaded to the YubiCloud. As part of the process of manufacturing every YubiKey, a Yubico OTP credential is programmed into slot 1, and its information is also transferred to YubiCloud, […] Read more -

What is a One-Time Password (OTP)? Key Takeaways Compromised credentials are a factor in the vast majority of data breaches, making the static password’s failure as a security mechanism well-documented. This weakness prompted a necessary evolution in access management, such as the adoption of the OTP as a second factor from around the mid-2000s, which even accelerated through the early 2010s. […] Read more -

What is an Authenticator App? How does an authenticator app work? An authenticator app is usually installed on a smartphone or other device and generates a random passcode every 30 seconds. The passcode can be used for sign-in, two factor authentication, an more. Passcodes generated by an authenticator apps are generated from a secret code that is shared between the […] Read more