Tag: YubiKey FIPS Series
-
YubiKey 5 FIPS Series and YubiHSM 2 FIPS are now FIPS 140-3 validated: What it means for high assurance security Editor’s Note: This blog has been updated as of June 4, 2026 to reflect YubiHSM 2 FIPS 140-3 validation With the growing threat of Generative and Agentic AI, where phishing and other sophisticated attacks have become faster and more targeted than ever before, federal agencies and regulated industries need to protect all of their users […] Read more -

Yubico submits YubiKey 5 FIPS Series for FIPS 140-3 validation We’re excited to share that the YubiKey 5 FIPS Series latest 5.7 firmware has completed testing by our NIST accredited testing lab, and has been submitted to the Cryptographic Module Validation Program (CMVP) for FIPS 140-3 validation, Overall Level 2 and Physical Level 3. This marks a significant milestone in our ongoing commitment to providing […] Read more -
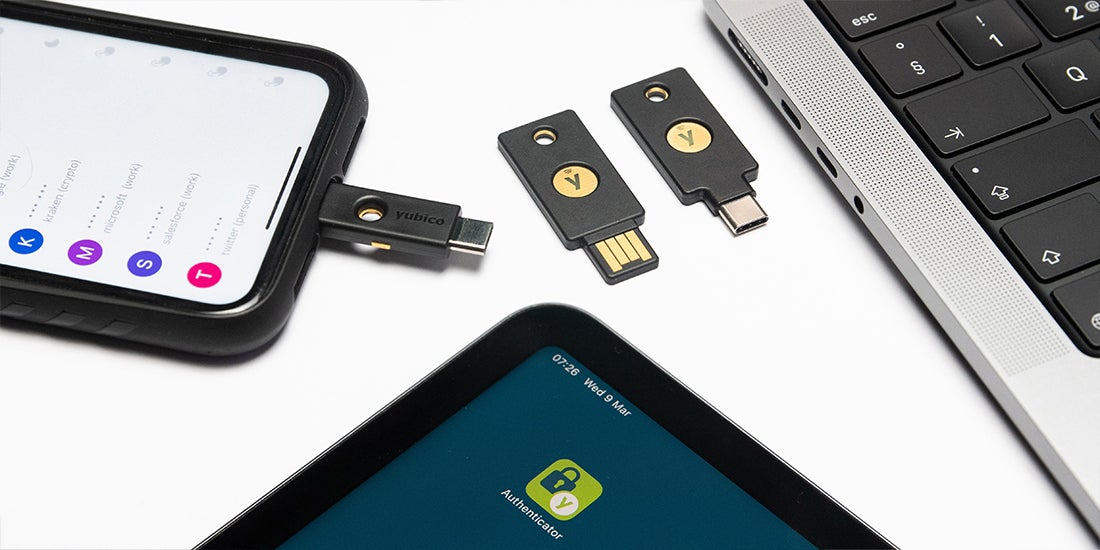
YubiKey as a smart card on iOS Certificate-based smart cards have been one of the most trusted and proven implementations of multi-factor authentication for over 20 years. There’s only one problem… the typical credit card-shaped smart card didn’t work well, if at all, on mobile devices without additional hardware and software. Today, smart cards come in many form factors, from a credit […] Read more -

Seven tips if you’re still scratching your head after reading Biden’s cybersecurity executive order Yubico works with a lot of federal agencies and contractors, as well as with customers in regulated industries, so we understand the challenges new compliance regulations can bring. The executive order that was released May 12 can be seen as the federal government fully embracing the move toward multi-factor authentication (MFA) for use cases where […] Read more -

The YubiKey 5 FIPS Series is here and there are 5 things you need to know Today, we’re thrilled to announce yet another product milestone in addition to the launch of YubiHSM 2 FIPS — the long-awaited YubiKey 5 FIPS Series is now generally available. It is the industry’s first set of multi-protocol security keys with support for FIDO2 and WebAuthn, along with smart card (PIV/CAC), to receive FIPS 140-2 validation, Overall […] Read more -

YubiKey 5 FIPS product brief FIPS 140-3 Validation Ensures Strong Security and Compliance. Read more -
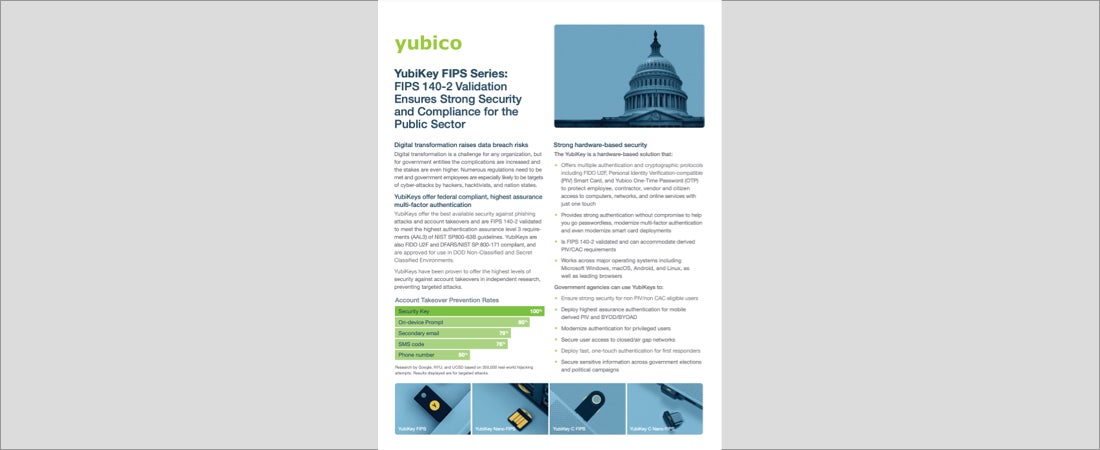
YubiKey FIPS Series public sector brief YubiKey FIPS Series brief for government and other public sector entities. Read more -

YubiKey FIPS Series Certified Security Meets High Compliance The YubiKey 5 FIPS Series is rigorously certified to meet the highest authentication requirements. Ensure secure access, compliance, and supply chain integrity with a key manufactured in the U.S. and Sweden. Certifications Learn more about the YubiKey 5 FIPS Series Read more -

What is FIPS 140-2? What does it mean to be FIPS 140-2 Certified/Validated? To be FIPS 140-2 certified or validated, the software (and hardware) must be independently validated by one of 13 NIST specified laboratories, this process can take weeks. The FIPS 140-2 validation process examines the cryptographic modules. Level 1 examines the algorithms used in the cryptographic component […] Read more -
YubiKey for Federal Government Hear best practices from government and security executives on how to get started with phishing-resistant MFA for federal use cases where PIV and CAC are not suitable. Read more