As sophisticated cyberattacks continue their relentless pursuit towards SMBs and enterprises, companies must prioritize improvements to their cybersecurity infrastructure to better secure their customers, employees, and partners. Username and passwords no longer provide adequate security against the ever evolving landscape of cyberattacks.
Late last year, Salesforce took a strong and decisive stance, announcing that beginning February 1, 2022, the company will require its customers to enable multi-factor authentication (MFA) to access its products, solutions, and platforms. This requirement complements similar initiatives from other tech giants like Google and Twitter, and most recently the US Government via its Executive Order 14028, which states that by 2024, SMS tokens and push notification authentication apps utilizing one-time passcodes will no longer comply with US government requirements.
Yubico applauds Salesforce’s latest move to enforce MFA and its support for phishing-resistant, FIDO-based security key authentication. With MFA in place, companies like Salesforce are greatly enhancing the security of their customers and platforms, while delivering a positive user experience.
Salesforce’s requirement will significantly accelerate the adoption of strong and modern hardware authentication across the globe and better secure hundreds of thousands of customers and companies against cyber threats that can cripple businesses.
According to Ian Glazer, Senior Vice President of Identity Product Management at Salesforce, “At Salesforce, trust is our number one value, and protecting customer data is paramount. Driving adoption of strong MFA, the single best thing people and organizations can do to protect their user accounts and data, requires a range of MFA options, such as hardware keys. Through partnership with our customers to spread the use of MFA, we can make it much harder for common threats like phishing and credential stuffing to succeed.
I’m ready to implement MFA, but which one should I pick?
Most traditional (or legacy) MFA methods, such as SMS, one-time passcodes, and mobile authenticator apps, do help prevent cyberattacks—but it is worth noting that not all MFA options are created equal. For example, SMS-based authentication has time and time again been proven to not be effective enough to secure an enterprise. And it is important to note that Salesforce is requiring the use of strong MFA methods and not allowing email or SMS-based one-time passwords.
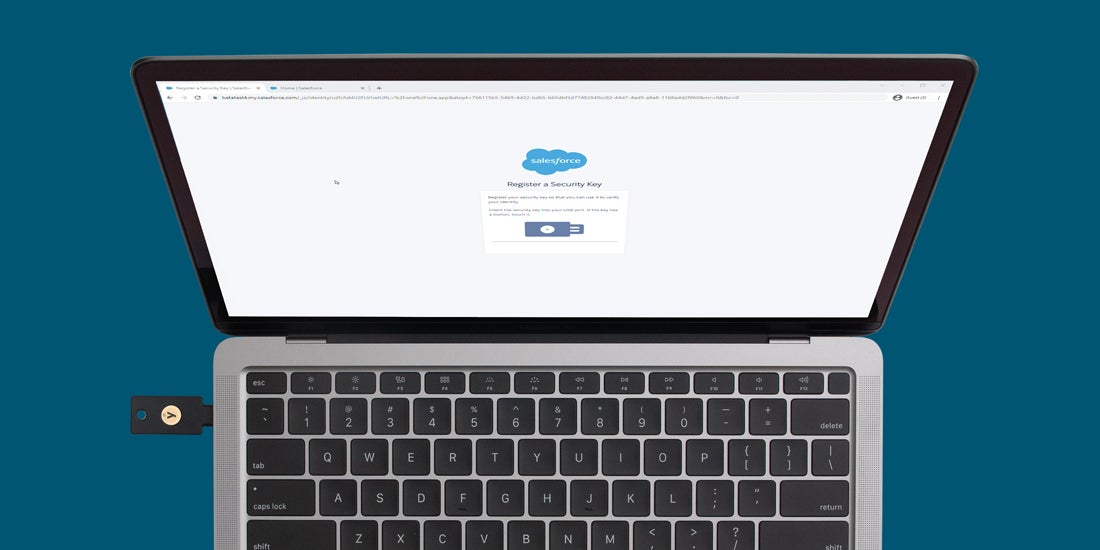
Moving to modern FIDO-based (U2F/FIDO2/WebAuthn) authentication allows an organization and their users to achieve phishing-resistant MFA. Physical security keys, like the YubiKey, allow organizations to meet the most stringent of cyber security requirements for authentication, while being extremely user friendly—a simple touch to the YubiKey is all that is needed to authenticate identity and provide secure access.
These hardware-based security keys are highly secure and fully comply with Salesforce’s MFA requirements. They work across all devices and operating systems to enable secure login to hundreds of online services and applications (without needing network service or batteries), to help eliminate nearly all account takeover risks.
Choosing the right YubiKey for my business
Whether your business is an enterprise with a complex hybrid IT environment or a cloud native SMB, Yubico has the right key to protect your infrastructure and employees. The YubiKey 5 Series offers multi-protocol security keys in a full range of form factors and the YubiKey 5 FIPS Series is designed to meet all compliance and regulatory requirements.
If you are looking to support your organization at scale, YubiEnterprise Subscription offers flexible purchase options and in today’s remote and hybrid working environments, YubiEnterprise Delivery gets YubiKeys to your employees regardless of location.
To find out which YubiKey is the best fit for your organization, visit https://www.yubico.com/quiz/
We remain committed to providing the best in class solutions to make the internet a safer place for everyone, from consumers to SMBs to large enterprises.
——–
To learn more about adding MFA to secure your Salesforce account with your YubiKey, see here.