Blog
Stay up to date on company and partner news, product tips, and industry trends.
-
 Empowering enterprise security at scale with new product innovations: YubiKey 5.7 and Yubico Authenticator 7
Empowering enterprise security at scale with new product innovations: YubiKey 5.7 and Yubico Authenticator 7As phishing attacks evolve and are on the rise, organizations are continuously seeking modern, strong authentication technologies like FIDO-based passwordless logins and smart card solutions to safeguard their digital assets, employees, customers and partners. By embracing passwordless authentication and implementing unmatched security measures, organizations can safeguard their sensitive data and ensure a resilient defense against […]
Read more -
 Works with YubiKey Spotlight (World Password Day Edition): Empowering enterprises to a passwordless future through integrated solutions with key partners
Works with YubiKey Spotlight (World Password Day Edition): Empowering enterprises to a passwordless future through integrated solutions with key partnersToday, May 2nd, is World Password Day. Each year, this serves as an annual reminder to take action and steps to ensure our digital lives are secure. Now, more than ever with data breaches relying on poor password management to gain access to sensitive data, this day has become a cornerstone in promoting cybersecurity awareness […]
Read more -
 From passwords to passkeys: Entering a new era in cybersecurity
From passwords to passkeys: Entering a new era in cybersecurityNote: This article is also featured in Fortune Magazine here. Phishing, a common tactic used by hackers to obtain access to sensitive information, is accredited as a contributing factor in over 80% of all security breaches. Phishing occurs when malicious actors impersonate a legitimate entity to deceive people into providing personal information – typically via […]
Read more -
 QR codes within enterprise security: Key considerations and best practices
QR codes within enterprise security: Key considerations and best practicesEvery second, a phishing attack takes place. In fact, over 80% of cyber attacks are a result of stolen login credentials from attacks like phishing – mostly due to the relatively low cost and high success rate to execute these attacks. Unfortunately, this pattern will continue to grow as attackers become more sophisticated, utilizing tools […]
Read more -
 Introducing the expanded YubiKey Bio Series: YubiKey Bio Multi-protocol Edition (Early Access)
Introducing the expanded YubiKey Bio Series: YubiKey Bio Multi-protocol Edition (Early Access)As the threat of sophisticated attacks like phishing continue to rise, enterprise users and cybersecurity teams are seeking a solution that offers robust security and user-friendly functionality. With the increasing adoption of biometric logins, enterprises aim to marry strong security with user convenience to boost productivity and job satisfaction. Hardware security keys that leverage biometrics, […]
Read more -
 Works with YubiKey Spotlight: ‘Leap’ into modern, phishing-resistant security with robust partner support for YubiKeys
Works with YubiKey Spotlight: ‘Leap’ into modern, phishing-resistant security with robust partner support for YubiKeysWith 2024 being a leap year, this gives business an extra opportunity to “leap” toward reflecting, adjusting and aligning all aspects of their organization – including an increasingly critical area in cybersecurity. With bad actors and cyber attacks like phishing becoming increasingly sophisticated, enterprises need to stay ahead of evolving cyber threats and regulatory requirements […]
Read more -
 QR code phishing attacks (Quishing): What to know and how to stay secure
QR code phishing attacks (Quishing): What to know and how to stay secureIf you immediately think of email when you think of phishing, you’re not alone. However, a new form of a text-based scam is making waves – highlighted by a seemingly legitimate text from the USPS which lets receivers know that their “package” arrived at the warehouse. To receive the package, it instructs users to click […]
Read more -
 Microsoft updates: Entra ID FIDO2 security key support and Azure Virtual Desktop passwordless sign-in
Microsoft updates: Entra ID FIDO2 security key support and Azure Virtual Desktop passwordless sign-inWith the use of phishing-resistant multi-factor authentication (MFA) like passkeys growing more every day, it’s exciting to see the widely popular service, Microsoft 365, announce availability recently for passkeys on YubiKeys with mobile devices. This new Microsoft preview not only opens up support on iOS and iPadOS for Microsoft 365, but for a whole range […]
Read more -
 YubiEnterprise Services update: Expansion of YubiEnterprise Delivery to secure users worldwide, and Single Sign-On (SSO) capabilities for customers using Duo/Cisco
YubiEnterprise Services update: Expansion of YubiEnterprise Delivery to secure users worldwide, and Single Sign-On (SSO) capabilities for customers using Duo/CiscoThis year, Yubico is continuing to focus on delivering phishing-resistant multi-factor authentication (MFA) to enterprises monthly at value and on a great scale through its YubiEnterprise Subscription offering. Today we’re excited to announce these latest updates, including: With these enhancements, YubiEnterprise Subscription continues to make it easy and flexible for enterprises to adopt phishing-resistant MFA […]
Read more -
 Remaining robust and resilient: A CISOs top recommendations for 2024
Remaining robust and resilient: A CISOs top recommendations for 2024As expected, 2023 was another challenging year for information security as organizations continued looking for ways to stay ahead of hackers. We saw an increasing amount and complexity of phishing attacks overall, driven by a major trend throughout the year making a significant impact: AI-driven phishing. Phishing remains the most prevalent attack method due to […]
Read more -
 Yubico joins CISA and the Joint Cyber Defense Collaborative’s High-Risk Communities Protection initiative to continue helping secure high-risk individuals and organizations
Yubico joins CISA and the Joint Cyber Defense Collaborative’s High-Risk Communities Protection initiative to continue helping secure high-risk individuals and organizationsWe’re honored to share that today we are joining the Cybersecurity & Infrastructure Security Agency (CISA) as they launch a new webpage to provide resources for high-risk individuals and organizations to receive the tools they need to protect themselves online. This webpage is the product of the Joint Cyber Defense Collaborative’s (JCDC) High-Risk Communities Protection […]
Read more -
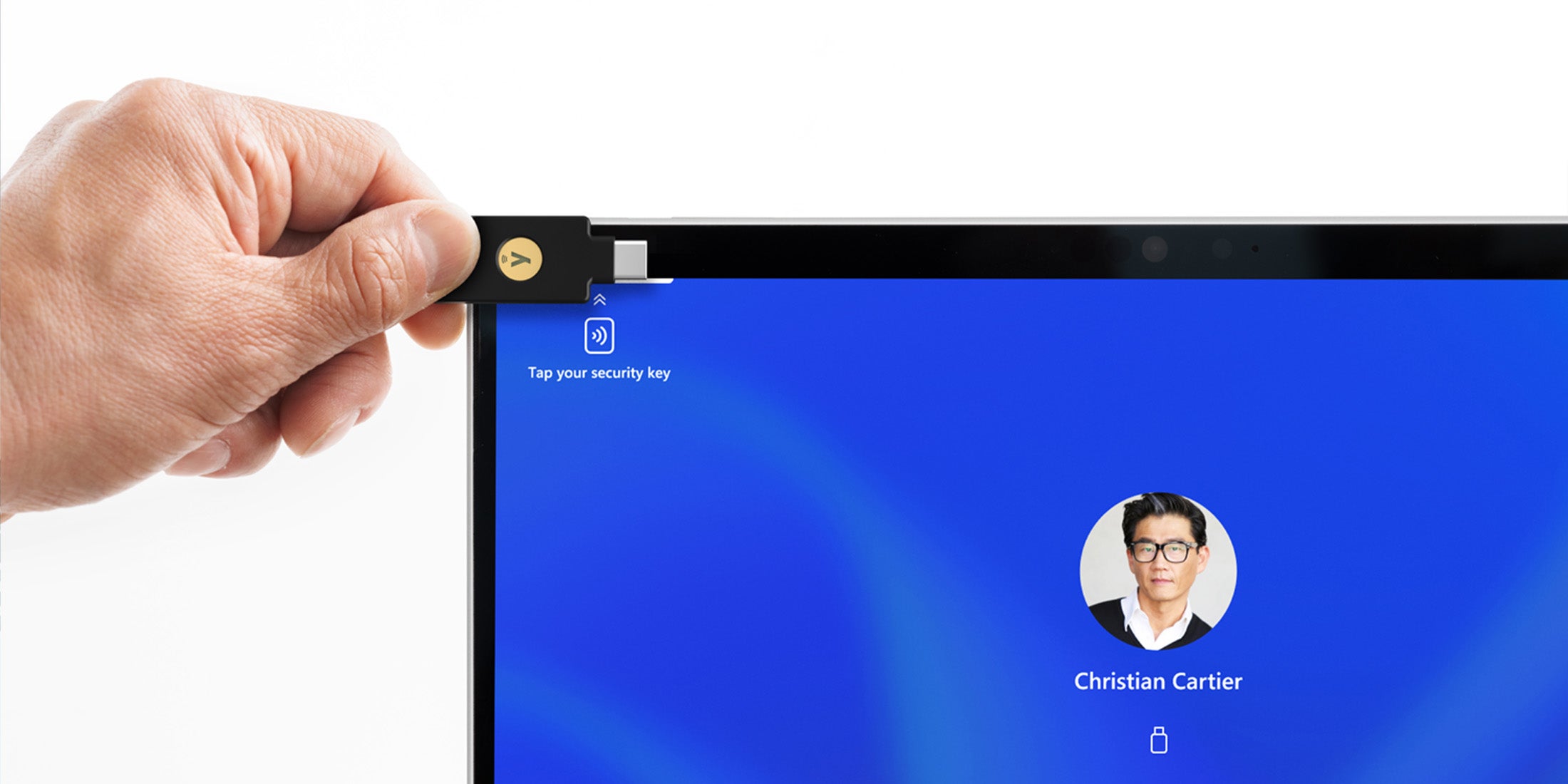 Microsoft’s Surface Pro 10 for Business enables NFC-based passwordless authentication with YubiKeys
Microsoft’s Surface Pro 10 for Business enables NFC-based passwordless authentication with YubiKeysTake advantage of the longstanding collaboration between Microsoft and Yubico by deploying YubiKeys together with the new Surface Pro 10 for your enterprise.
Read more -
 Five tips to maximize your consumer-facing passkey implementation
Five tips to maximize your consumer-facing passkey implementationPasskeys have taken the online security world by storm since their inception in mid-2022, even if the underlying technology can technically be traced back to FIDO2 and its breakthrough onto the world stage in 2018. Popularity has no doubt exploded due to their widespread adoption by the world’s largest tech companies – who also happen […]
Read more -
 Yubico and Defending Digital Campaigns survey highlights how AI and cybersecurity is shaping the 2024 election landscape
Yubico and Defending Digital Campaigns survey highlights how AI and cybersecurity is shaping the 2024 election landscapeThe election ecosystem is a prime target for cybersecurity threats and the 2024 United States election cycle will be no different. Though many security improvements have been made in recent years, bad actors continue to become more sophisticated in gaining access to private information – most often driven by phishing attacks. As the 2024 U.S. […]
Read more -
 How businesses can protect the identities of its leaders and employees from the perils of rising sophisticated cyber attacks
How businesses can protect the identities of its leaders and employees from the perils of rising sophisticated cyber attacksOn a daily basis, organizations around the world contend with increasingly sophisticated cyber attacks like phishing that exploit human error, leverage compromised accounts and employ convincing, yet deceptive, tactics to infiltrate corporate networks. Balancing security with a seamless user experience for their front line, employees should be a top goal forevery executive since those are […]
Read more
