Last year’s SolarWinds attack was caused by intruders who managed to inject Sunspot malware into the software supply chain. The hackers exploited a breach in the SolarWinds code signing system, which allowed them to fraudulently distribute malicious code as legitimate updates to installations across the world. While this attack taught the industry many lessons, one of the most important takeaways is to properly sign code that will be distributed and executed.
Attacks like that of SolarWinds have even prompted the White House to issue a recent executive order requiring organizations working with the government to secure their supply chain and ensure code signing and other elements are properly secured as part of a zero-trust architecture and multi-factor authentication requirements.
Code signing is commonly used to protect all types of software modules and executables. Software drivers, applications, installation files, scripts, and firmware modules in vehicles or industrial systems can all be signed with PKI (Public Key Infrastructure)-based keys and certificates, providing a mechanism to trust that the code provided is legitimate. Code signing has been used for decades, but the need for secure code signing solutions has increased in the recent past, as demonstrated in the aftermath of the SolarWinds attack.
Ensuring Secure Code Signing
Protecting the signing keys and certificates are crucial in any code signing software system, and (HSMs) hardware security modules offer a secure way to generate, store and protect cryptographic keypairs and X.509 certificates on secure, purpose-built hardware. For organizations with increasingly high demands on IT security or those in regulated industries or high-risk environments, FIPS 140-2 certified HSMs are recommended or even mandatory for such deployments.
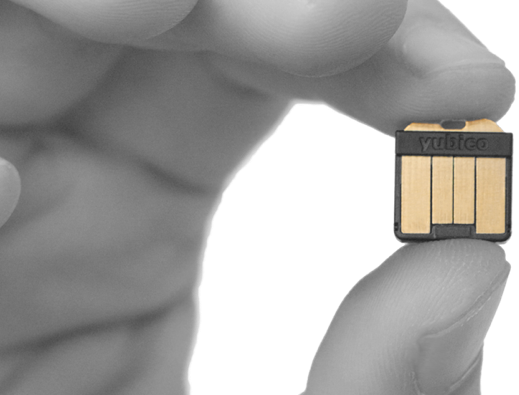
Yubico offers the YubiHSM 2 and the YubiHSM 2 FIPS for protecting keys and certificates for signing code. For organizations that need to meet the FIPS 140-2 requirements, they have the option of a FIPS 140-2, Level 3 validated HSM if they are in regulated industries or high-risk environments, to ensure the highest levels of data protection.
There are different cryptographic APIs for signing different types of code: The Microsoft Cryptographic API Next Generation (CNG) is designed for signing Windows executables, while the Java Cryptographic Architecture (JCA) can be used for signing Java code and JAR-files.
The YubiHSM2 and YubiHSM 2 FIPS can both be used with both APIs for signing code. On Microsoft Windows, the YubiHSM 2 KSP extends the Microsoft CNG architecture, which allows for the Microsoft SignTool to sign Windows executables with keys and X.509 certificates that are stored in the YubiHSM 2.
As regards to the Java Cryptography Architecture (JCA), the YubiHSM 2 PKCS#11 module can be loaded by the native Oracle SunPKCS11 provider. We have recently published a reference implementation package on GitHub YubicoLabs with scripts and deployment instructions for certificate enrollment to the YubiHSM 2. Once the X.509 certificate is enrolled to the YubiHSM 2, it can be used with the Java tool Jarsigner or third-party applications for Java code signing.
SolarWinds also taught us that the source code repository must be safely managed to ensure that only proper code modules are signed. This puts additional requirements on signing the source code in a secure environment, preferably where the HSM with the code signing certificate is located.
There can also be industry specific demands on the code signing process, in particular for segments that are specifically exposed to SolarWinds type supply chain attacks. For instance, in the transportation sector there are cases where customized code modules are deployed in vehicles that travel across the world. Security is essential when deploying code in vehicles, so the code modules, in many cases, are signed to guarantee the integrity and authenticity. This means that the HSMs with the signing certificates often have to be distributed to remote locations, requiring building a PKI based chain to ensure the validity of the data from origin to where the code is ultimately deployed to, and providing a signature and verification for each step of the way in the supply chain.
Yubico recommends protecting code signing keys and certificates on an HSM, to protect Java and Windows solutions from a SolarWinds type of supply chain attacks. The YubiHSM 2 and YubiHSM 2 FIPS, which come in a portable nano form factor and offer a cost-effective price/performance ratio, are well-suited for such deployments. This makes them well suited for cost-efficient, distributed and secure code signing.
For common usage of the YubiHSM 2 and the YubiHSM 2 FIPS, please visit the Yubico developer web site.



