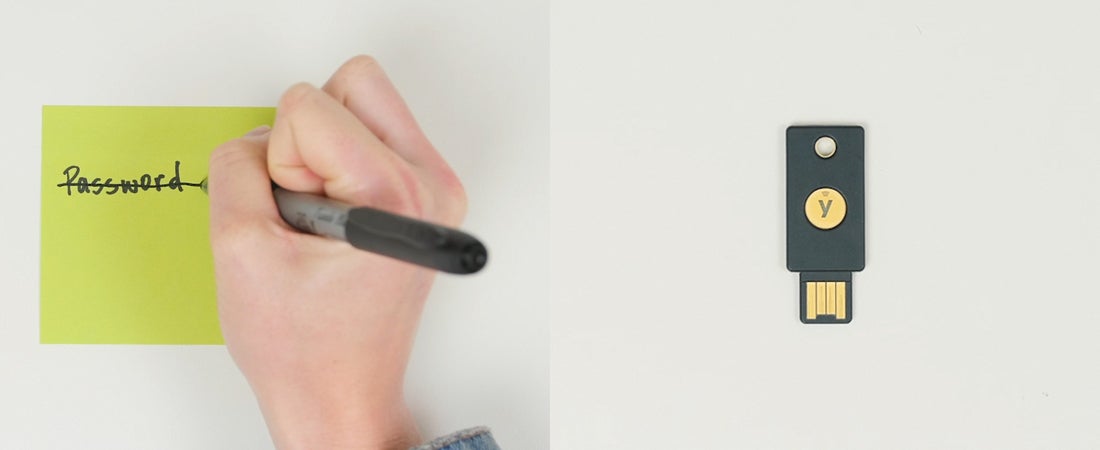
Given the number of breaches in the news today where passwords were at the root of the problem, many companies are now exploring the benefits of a secure passwordless future. Secure passwordless logins not only bring cost efficiencies and a more frictionless user login experience into the organization, but deliver the security that is necessary in the post-pandemic world, when many millions of workers may continue working remotely.
Some companies may have finished with planning their passwordless strategy, and are ready to pull the lever on an implementation. The customers we work with get the message: going passwordless is more of a journey than a destination. And even if it’s a long road, to make the journey smooth you’ll want to make sure you don’t fall into any deep potholes along the way.
No customer’s road to passwordless is going to be the same — your implementation could involve a smart card passwordless approach, a FIDO2/WebAuthn passwordless approach, or a hybrid approach that combines both approaches for different business needs. No matter what road you take, though, there are some common pitfalls you can avoid if you’re looking out for them:
Pitfalls to avoid on your passwordless strategy roadmap
- The “look, I can see the end of the road!” syndrome. Security professionals might be used to the traditional way of thinking about an implementation — here’s a product, let’s map out a plan, implement it, and then sort out the bugs. But passwordless can involve several products, installed at different times with different levels of users. The journey to passwordless isn’t always a short road. There may be a part of the road to passwordless that bends around the next mountain. You can’t necessarily see the entire road, but you can be prepared for whatever is coming around the bend. It’s OK to start with addressing the most important and critical use cases and user populations and then build on your passwordless implementation as you go.
- Planning in a silo. Passwordless is not just an IT implementation. It should involve all corners of the company because it can represent a significant change in company culture and processes. If a plan is written narrowly or only by a single department, it’s more likely to fail once it has to be communicated to users, the HR department and the C-suite. The key is to take a holistic approach and bring all key stakeholders along on the journey from the beginning for maximum user adoption, which is what ultimately enhances the security posture of the overall organization.
- Skip the pilot, we don’t have enough time! Sometimes there’s a real urgency on projects, especially if it’s a response to a breach or another emergency. But we don’t recommend skipping the proof-of-concept and pilot phases of your project, because they can be extremely helpful in mapping out where you’re headed. You can plan for a single pilot, or you may want to deploy several pilots targeting different user groups to measure readiness before a broader rollout to all users.
Typically you can take a few steps during proof of concept before you launch the pilot, including:- Validate the intended passwordless implementation work as expected with the essential systems, use cases, and users at the earliest phase.
- Set up a testing environment that demonstrates end-to-end connectivity between existing systems and authentication technology for key users/user groups.
- Verify that your defined success criteria can be met.
- Has anyone communicated with the users? When technical teams are leading a project, user communication and training often get overlooked. The communications/training team can help by planning live or virtual events that build anticipation and a greater understanding of the new solutions and processes.
- We can go solo on this implementation. You’ve heard the old adage about getting something done fast, cheap and good? Pick only two, right? Ideally, you want all three (or something close to it) and finding the right professional services as you drive down the road to passwordless may get you closer to that ideal. This is especially true if you are on a tight deadline — industry expertise from an outside source can help accelerate your passwordless journey.
Read Yubico’s Bridge to Passwordless series to learn more about how to plan and execute a passwordless strategy.