Tag: WebAuthn
-

Expanded Security Key Series: Phishing-resistant, FIDO-only MFA Security Key Series Expansion Last month, we announced the expansion of both Yubico’s YubiEnterprise Subscription and our Security Key Series lineup, which included the addition of two new enterprise, FIDO-only (FIDO2/WebAuthn and FIDO U2F) security keys. We’re excited to share that the Security Key Series are officially available today and can be purchased via our […] Read more -

What is Web Authentication? Learn the definition of Web Authentication and get answers to FAQs regarding: What is Web Authentication? How does it work? and more. Read more -

Twitter’s changes to MFA: What the move means for the future of authentication A recent announcement by Twitter has begun to rock the multi-factor authentication (MFA) boat, and the ripples have spread throughout the tech world. The company announced that starting on March 20, 2023, unless a user is subscribed to its Twitter Blue program (an $11/month subscription), they will lose access to SMS-based two-factor authentication (2FA). SMS […] Read more -

Q&A: Yubico Software Engineer Emil Lundberg on the past, present and future of WebAuthn With the proliferation of distributed work globally and as cybercriminals become more sophisticated by the day – it’s clear that traditional passwords and legacy MFA simply aren’t strong enough. Enter WebAuthn, an API that makes it easy for web services to integrate strong authentication into applications using support built in to all leading browsers and […] Read more -

WebAuthn Explained: Advancing Authentication with Hardware Security Keys & Establishing a Root of Trust – Yubico Insights Establishing a “root of trust” is the mechanism in which a user recovers an account or establishes their identity on a new device Read more -
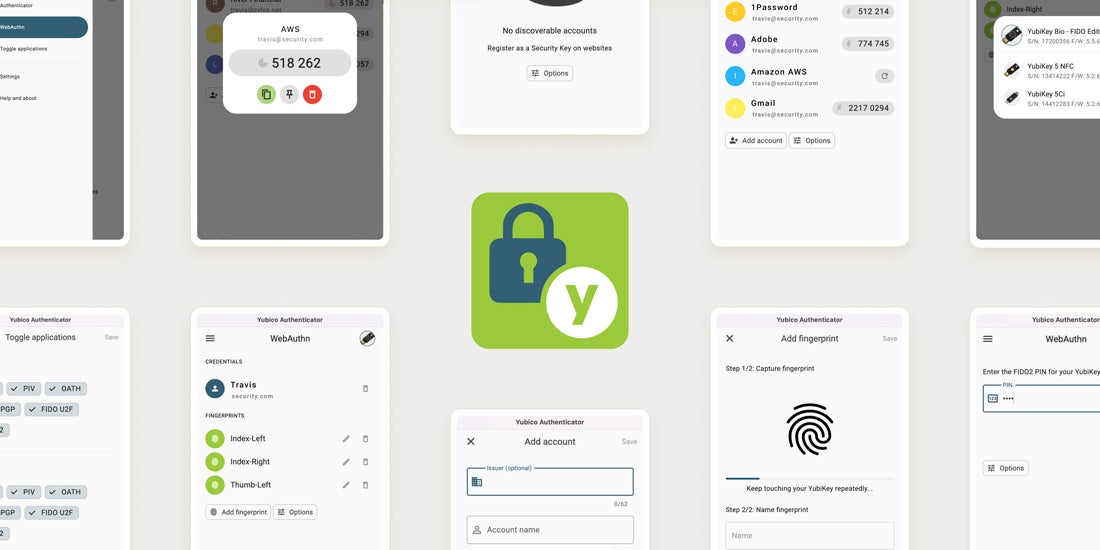
Introducing Yubico Authenticator 6 for Desktop Today we’re releasing the first public beta version of Yubico Authenticator 6 for Desktop. This new version has some big changes under the hood, so let me explain what they are and why we’re doing them. Or, if you’re just eager to try it out, skip to the bottom of this post and click on […] Read more -
WebAuthn implementation: What’s what, why should you care and new updates from Yubico When it comes to WebAuthn, there’s certainly no shortage of acronyms or protocols. But what do they mean, and which ones do you need to care about? Fret not – both clarity and help are available! In this blog, we’ll share tips on how to implement WebAuthn, as well as share news about java-webauthn-server library […] Read more -

Security considerations for the top 8 mobile device-restricted workplaces When looking at enterprises and organizations, there are many different business scenarios that can be present when addressing secure authentication. Whether those be shared workstations, remote workers, or even privileged accounts, there is one in particular that introduces its own difficulties: mobile device-restricted workplaces. It’s safe to say that there will always be workplaces which, […] Read more -

Google Chrome U2F API decommission: What the change means for your users and how to prepare With advancement often comes change. Some changes are exciting, like providing new features and broader support, while other changes can be a minimal bump in the road or, in extreme cases, cause adverse effects on end users. With Yubico’s commitment to keeping our customers updated on the latest in changes to security protocols, we wanted […] Read more -

Put Your Finger on the Pulse of What’s New with the YubiKey Bio Series Today, we are announcing the YubiKey Bio Series, Yubico’s first-ever YubiKeys supporting biometric authentication. The YubiKey Bio was first previewed at Microsoft Ignite in 2019 where we showed a live demo of passwordless sign-in to Microsoft Azure Active Directory accounts. We’ve taken the time to ensure that we are launching products that are highly secure […] Read more