Tag: YubiKey
-
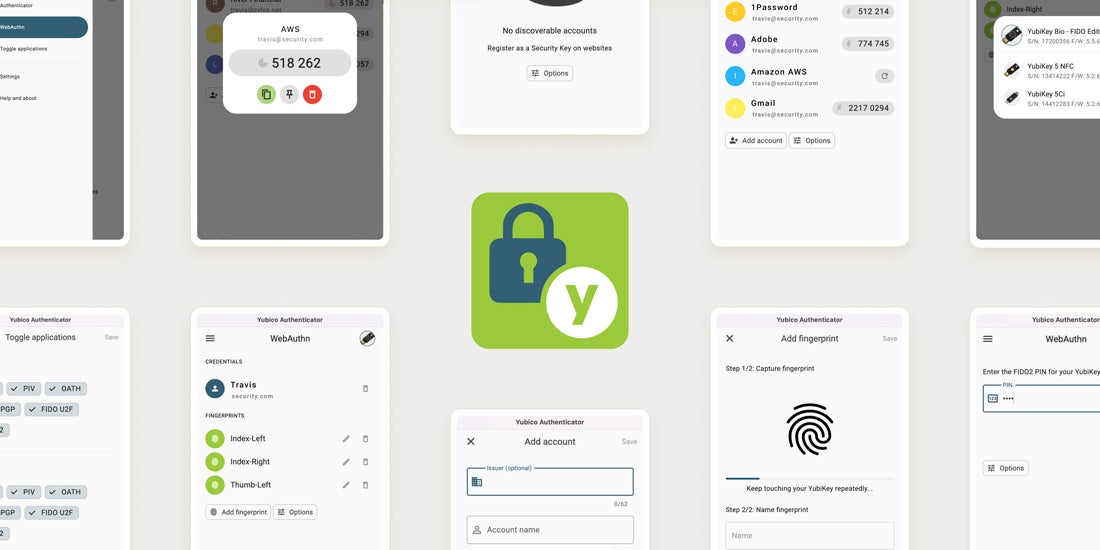
Introducing Yubico Authenticator 6 for Desktop Today we’re releasing the first public beta version of Yubico Authenticator 6 for Desktop. This new version has some big changes under the hood, so let me explain what they are and why we’re doing them. Or, if you’re just eager to try it out, skip to the bottom of this post and click on […] Read more -

A Yubico FAQ about passkeys In March, we published a blog called “YubiKeys, passkeys and the future of modern authentication” which took a look at the evolution of authentication from when we first introduced the YubiKey back in 2008, to where the industry is heading with the adoption and adaptation of WebAuthn/FIDO authentication. In recent months, there have been several […] Read more -
Compliant PINs and MFA: Modern direction for staying secure Entities within the US Federal Government are in the midst of a drastic change regarding how they approach the services they are using—moving away from traditional on-prem and proprietary systems to cloud services based on private platforms, like Azure and Amazon Web Services. However, the requirements for security remain the same regardless of the platform […] Read more -

YubiKeys protecting critical IT infrastructure in Ukraine The Russian invasion of Ukraine is a battle in both the physical and the digital world. On both sides, information warfare plays a more critical part of the battlefield than any other war in human history, with the biggest attack vector and threat being weak login credentials. According to a Ukraine cybersecurity executive at a […] Read more -
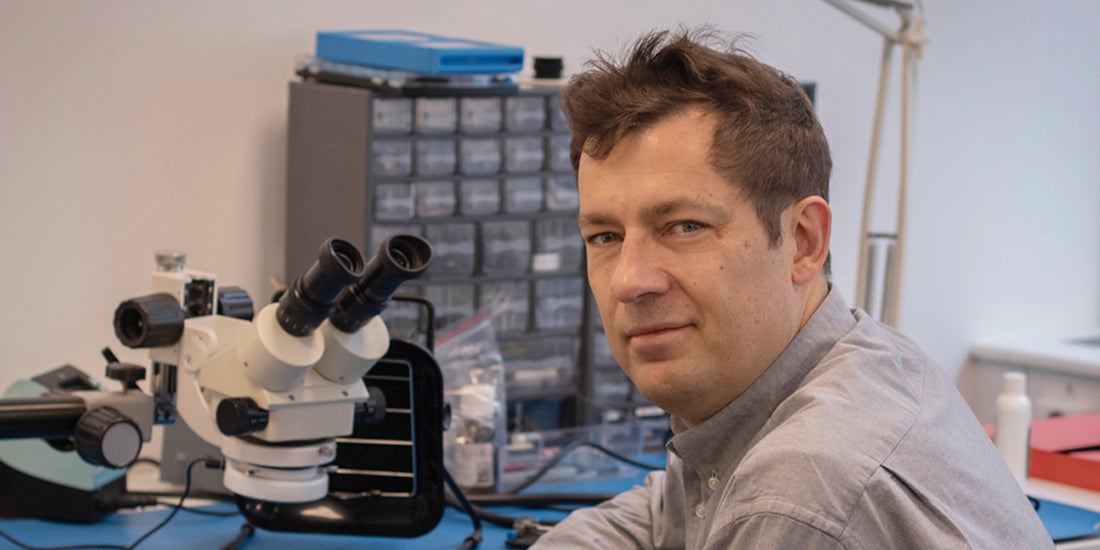
Q&A: Yubico’s Co-Founder & Chief Innovation Officer Jakob Ehrensvärd It’s not every day you get to hear a pioneer of internet security share why you and the rest of the world needs modern, reliable and easy-to-use Multi-Factor Authentication (MFA). If you want to understand phishing-resistant authentication and why it matters, there’s nobody better to ask than Jakob Ehrensvärd, Yubico’s co-founder. Jakob built his first […] Read more -

White House declaration: act now for cybersecurity attack protection Last week, President Biden made a statement that couldn’t have been clearer in its message regarding cybersecurity attack protection to the private sector: “If you have not already done so, I urge our private sector partners to harden your cyber defenses immediately by implementing the best practices we have developed together over the last year […] Read more -
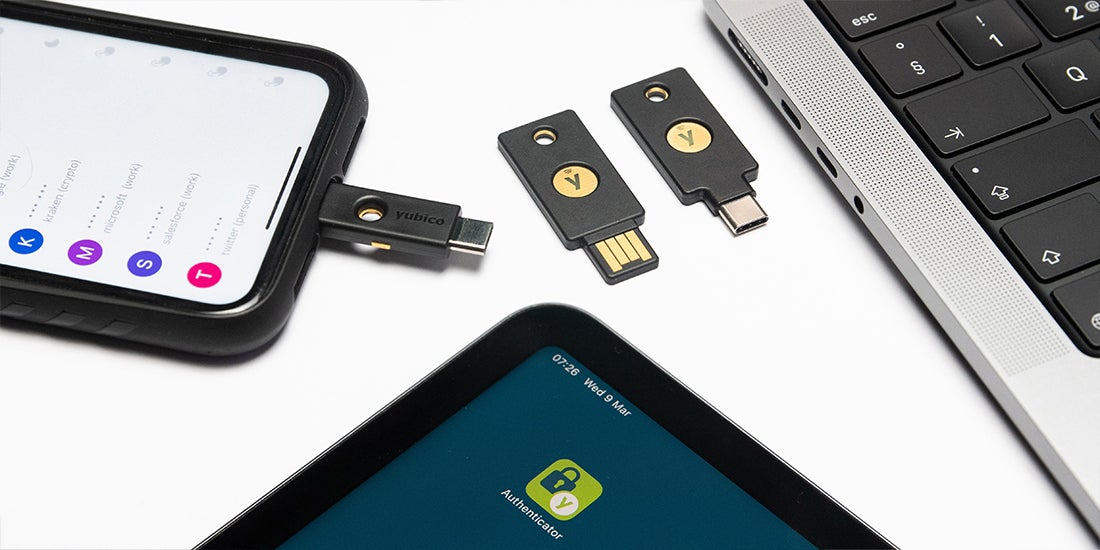
YubiKey as a smart card on iOS Certificate-based smart cards have been one of the most trusted and proven implementations of multi-factor authentication for over 20 years. There’s only one problem… the typical credit card-shaped smart card didn’t work well, if at all, on mobile devices without additional hardware and software. Today, smart cards come in many form factors, from a credit […] Read more -

Donating YubiKeys globally to those who need it most – Yubico With current events unfolding daily around the world, the reality that everyone can be affected by impending cyberattacks has set in. Now, individuals around the world are wondering how to stay secure during tumultuous times like this (and in the future). So, what exactly are the best ways to secure oneself online and mitigate the […] Read more -

Supply chain security in 2022 The SolarWinds and Colonial Pipeline security breaches are two (of many) incidents that have made supply chain attacks go mainstream. The primary challenge for businesses is that supply chain defense isn’t easy given the hundreds, if not thousands of entry points that need to be monitored along the way. But there are best practices that […] Read more -

Privileged Access Management at CERN: Q&A with Dr. Stefan Lüders In an era of increasing cyber attacks, how do you balance the desire for unrestricted research freedom against the need to protect that research from cyber threats? This is the challenge faced by CERN, leaders in the scientific research community. Their solution? Provide a clear articulation of what constitutes privileged data, and create flexible security […] Read more