Okta | Yubico
Strong phishing-resistant MFA for compliance with the EO
Strong phishing-resistant MFA for EO 14028 compliance
Executive Order (EO) 14028 and OMB memo M-22-09 shift the cybersecurity principles for federal agencies, their staff, contractors, and partners from perimeter-based defenses to a Zero Trust architecture strategy that includes the requirement for phishing-resistant MFA.
Phishing-resistant MFA refers to an authentication process that is virtually immune to sophisticated attacks that could intercept or trick users into revealing access information. Phishing-resistant MFA establishes an authenticated protected channel with the verifier, protecting against verifier impersonation attacks through impostor websites or fraudulent push authorization attempts.
As defined by the Federal Information Processing Standards (FIPS) 140-2 and NIST SP 800-63B, only two authentication technologies currently meet this requirement: the federal government’s Personal Identity Verification (PIV) standard/smart card and the modern FIDO2/WebAuthn standard.
According to this guidance, agencies and their supply chain partners must move beyond authentication methods that fail to resist phishing, including passwords, as well as those that rely on SMS or voice calls, one-time codes, or mobile push notifications.
Zero Trust with Yubico
and Okta is mission critical
Yubico and Okta are globally recognized leaders in cybersecurity working across public and private organizations on their journey to Zero Trust. Both are FIDO Alliance members working to set security standards.

Achieve federal compliance with Yubico and Okta
Yubico offers the YubiKey— a FIPS 140-2 validated hardware security key proven to stop 100% of account takeovers in independent research. Users of Okta Identity and Okta Adaptive MFA can combine adaptive authentication and contextual access management with native support for the YubiKey as a PIV-compatible smart card for immediate compliance with the authentication requirements of OMB M-22-09 in a Zero Trust framework:
- FIPS 140-2 validated (overall level 1 and level 2, physical security level 3)
- Validated to NIST SP 800-63-3 Authenticator Assurance Level (AAL) 3 requirements
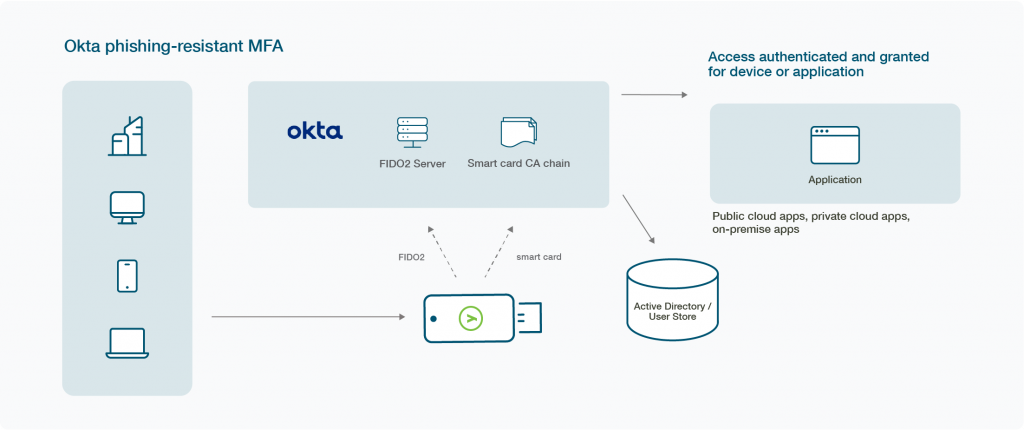
With Okta and the YubiKey, government agencies can deploy FIPS validated, hardware-backed MFA across multiple applications and operating systems, as well as modern devices, with single-sign-on (SSO) capabilities. With certificate-based authentication supported by a PKI, a user can leverage the YubiKey as a PIV-compatible smart card with Okta to access protected applications and services using a x.509 compliant digital certificate.
The easy and highly-secure solution has been tested and proven in the most security conscious government and enterprise environments.
Integrate your solution with YubiKey and Okta Adaptive MFA
Phishing-resistant MFA for your journey
to Zero Trust
FIDO2/WebAuthn
FIDO2 passwordless via supported browser or desktop login.
Certificate-based Authentication
With certificate-based authentication supported by a PKI, a user can leverage the YubiKey as a PIV-compatible smart card with Okta to access protected applications and services using a x.509 compliant digital certificate.
Derived FIDO2 Credentials
With Okta and the YubiKey, government agencies can simply deploy FIPS validated, hardware-backed MFA across multiple applications and operating systems, as well as modern devices, with single-sign-on (SSO) capabilities.
Stronger together
YubiKey, combined with Okta Identity and Okta Adaptive MFA, offer the best of both worlds – intelligent, modern phishing-resistant MFA to protect against account takeovers, as well as a simplified user experience that is adaptive to the level of identity assurance all the way up to hardware-based authentication for stronger levels of protection. YubiKeys are also durable, don’t require batteries or need a cellular connection, and are water-resistant and crush-proof. Here are some additional benefits to using YubiKeys with Okta:
Enable the bridge to passwordless authentication
Yubico and Okta work together to meet organizations where they are on their journey to passwordless, seamlessly supporting legacy infrastructures with multi-protocol flexibility as well as modern, cloud-based systems that leverage the latest FIDO2/WebAuthn standards.

Secure privileged users, mobile-restricted environments
Improve security and productivity for privileged users or those sharing workstations and provide support for remote workers, contractors, air-gapped/isolated networks, cloud services, high-risk military scenarios, and mobile-restricted environments.
PIV-compatible smart card
For organizations with PKI infrastructure, YubiKey enables smart cards as a primary authentication method to sign in to Okta managed applications and services using a x.509 compliant digital certificate; Okta accesses the certificate revocation list from the certificate authority.
Superior authentication
High-assurance authentication provided by the combination of the YubiKey 5 FIPS Series (FIPS 140-2 / NIST SP800-63B AAL3 validated) hardware security key and Okta Adaptive MFA policy framework.

Convenient login for higher employee productivity
No matter the device, user or login context, Okta Adaptive MFA and YubiKey together deliver a more reliable, secure and simplified login experience to Okta’s SSO, reducing support calls and downtime.
Adaptive and risk-based authentication
Administrators can define advanced authentication with Okta Adaptive MFA, pairing and device posture policies to trigger intelligent step-up MFA with the YubiKey or to accept trust within geo-fenced or other defined scenarios.

Supply chain and customer access
Provide federated support to partners, 3rd party entities and even customers to prevent breaches.
Enhance security posture with streamlined deployment
Okta and the YubiKey add strong authentication to identity platforms to bring a complete, easy-to-scale offering to organizations of all sizes, supported by YubiEnterprise subscription and delivery options.
Are you impacted by EO 14028?
Some organizations may believe that the Executive Order is focused towards federal agencies, but it has critical implications for many regulated and private sector industries such as defense, supply chain, healthcare, technology, and financial services. In March 2022, President Biden called on both state and local governments and the private sector to step up cybersecurity defenses in line with EO 14028 with all urgency, starting with “the use of multi-factor authentication on your systems to make it harder for attackers to get onto your system…”
Zero Trust is the new regulatory minimum for federal agencies. What does that mean for authentication?

Phishing-resistant MFA is mission critical for EO compliance and Yubico can help
Implement YubiKeys with help from Yubico

Professional Services Operational Deployment workshops
Get started

Find the right YubiKey
Contact our sales team for a personalized assessment of your company’s needs.