In conjunction with Data Privacy Day, Yubico is releasing today new research in a report entitled, The 2019 State of Password and Authentication Security Behaviors Report, conducted by Ponemon Institute. The findings reveal that despite a growing understanding of security best practices, user behavior is still falling short. The problem? Passwords continue to trip up users and compromise security and many users are not taking advantage of stronger two-factor authentication solutions that are available.
The annual Data Privacy Day initiative, led by the National Cyber Security Alliance (NCSA), has grown in popularity each year — and with good reason. Massive data breaches like the recent Collection #1 continue to happen. With nearly 773 million records exposed, including email addresses and passwords, Collection #1 is one of the largest breaches to date; and yet, are individuals taking the actions needed to protect their online accounts? According to the report findings, it appears not.
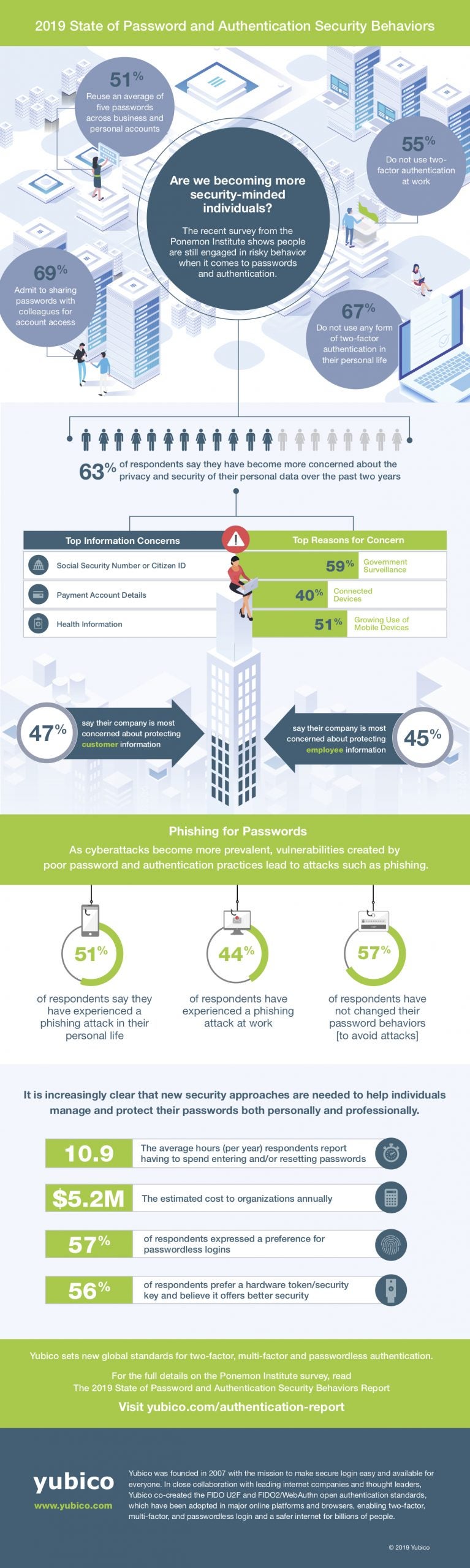
Are we becoming more security-minded, and better yet, are we following best practices? Some of the most interesting stats revealed that: (Click to Tweet your favorites!)
2 out of 3 (69%) respondents share passwords with colleagues to access accounts
51 percent of respondents reuse passwords across business and personal accounts
Beyond the above listed highlights, the full 2019 State of Password and Authentication Security Behaviors Report delivers further data on the following topics:
How privacy and security concerns affect personal password practices
Risky password practices in the workplace
Authentication and account security in organizations
Differences in password practices and authentication security behaviors by age
Differences in password practices and authentication security behaviors by country (Germany, France, UK, USA)
To read more of the research highlights, please check out our infographic below or download our full research report here.