Tag: MFA
-

Google Chrome U2F API decommission: What the change means for your users and how to prepare With advancement often comes change. Some changes are exciting, like providing new features and broader support, while other changes can be a minimal bump in the road or, in extreme cases, cause adverse effects on end users. With Yubico’s commitment to keeping our customers updated on the latest in changes to security protocols, we wanted […] Read more -
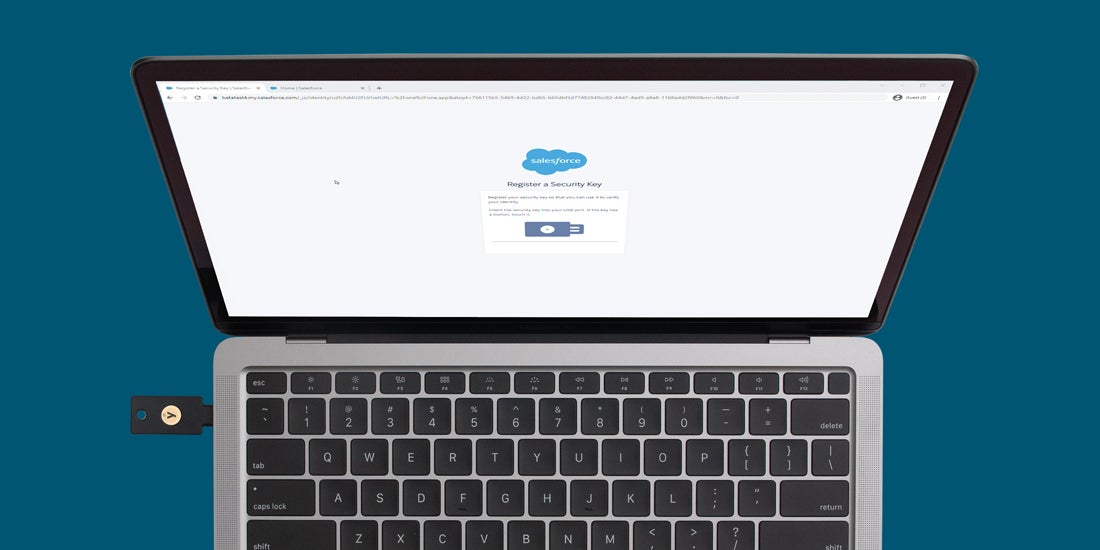
Salesforce is requiring MFA: Why this matters and what you can do As sophisticated cyberattacks continue their relentless pursuit towards SMBs and enterprises, companies must prioritize improvements to their cybersecurity infrastructure to better secure their customers, employees, and partners. Username and passwords no longer provide adequate security against the ever evolving landscape of cyberattacks. Late last year, Salesforce took a strong and decisive stance, announcing that beginning […] Read more -

Yubico’s top information security recommendations for 2022 Last week, we shared a look back at 2021, which experienced an increase in the number of high profile security breaches, many involving devastating ransomware attacks. Attackers preyed on traditionally softer targets like hospitals, schools, and local governments, in addition to the continued focus on the supply chain. Although the root cause for many of […] Read more -

2021: Both challenging and promising for cyber security 2021 was a challenging, yet promising year for cyber security. This past year, we saw critical infrastructure, which we may have taken for granted in the past, breached and disrupted. My father, who lives in Sweden, could not buy food in his local grocery store, and coworkers and friends on the east coast in the US […] Read more -

MFA implementation and the users you need to reach: overachievers, traditionalists and cautious employees When a breach investigation team assembles after an incident at a company or organization, misinformed users often get added to the ‘suspects list’ because accidents happen that sometimes lead to holes in security. Though everyone in a company means well, just like accidentally dropping a glass or losing your car keys, the reality is that […] Read more -

A Day in the Life: Dispelling the Myths of Mobile Authentication COVID-19 initiated the most rapid digital transformation ever witnessed—organizations fast-tracked two-factor and multi-factor authentication to transition millions of employees to work from home. But with remote and hybrid work likely to continue in 2022 and beyond, it’s time to step back and ask: is my in-use authentication as secure as I think it is? Is […] Read more -

In passwordless authentication, who is holding the keys? Strong authentication practices are based on validating a number of authentication factors to a relying party (RP) or identity provider (IDP) to prove you are who the RP expects. Examples of relying parties could be Dropbox or Salesforce. Identity providers, who can also be a relying party that interacts with the authenticator, include Microsoft Entra […] Read more -

Mitigation and incident response plans to help prevent ransomware attacks We’ve all grown accustomed to a flood of ransomware attack news almost every week, with no end in sight. The recent arrest of two Ukrainian ransomware attackers demonstrates that the White House is serious about going on the offensive against ransomware distributors. But often enforcement could end up being a game of whack-a-mole — hit […] Read more -

YubiEnterprise Delivery Service expands to 49 countries to help customers increase remote work security for distributed workforces The past two years have seen a tremendous amount of change regarding normal business processes for companies around the world, and our customers are no exception. When YubiEnterprise Delivery was first launched in May of 2020, organizations and their workforces, partners, and customers were just beginning to grapple with the new challenges that the pandemic […] Read more -

A new White House directive: Phishing-resistant MFA! The US Government’s Office of Management and Budget recently issued its Zero Trust Strategy, which would require that Federal agencies only use phishing-resistant multi-factor authentication. This strategy comes on the heels of a number of other actions from the Executive Office of the President including a cybersecurity executive order in May. This executive order directed […] Read more