Tag: MFA
-
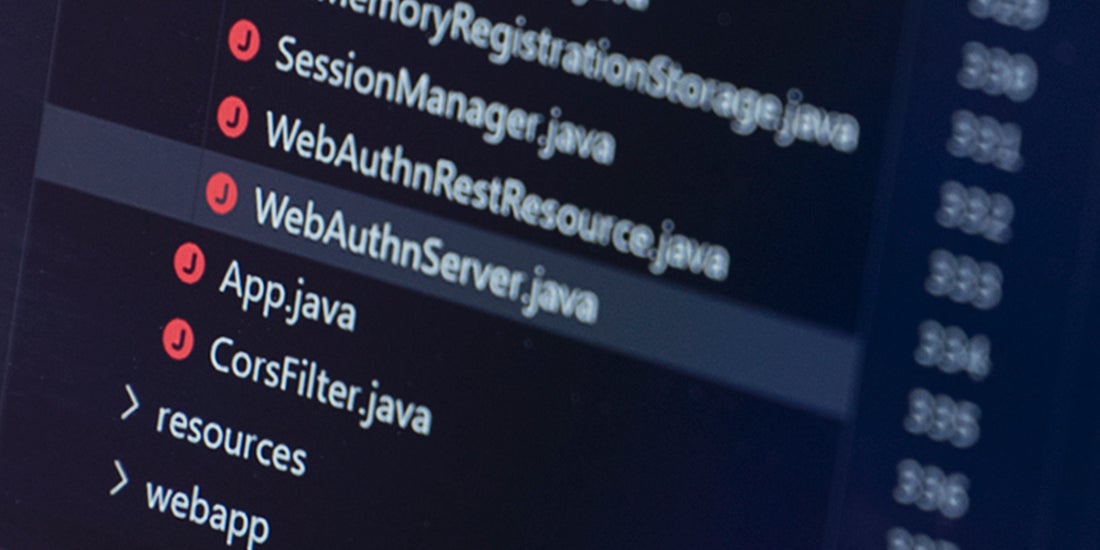
WebAuthn implementation: What’s what, why should you care and new updates from Yubico When it comes to WebAuthn, there’s certainly no shortage of acronyms or protocols. But what do they mean, and which ones do you need to care about? Fret not – both clarity and help are available! In this blog, we’ll share tips on how to implement WebAuthn, as well as share news about java-webauthn-server library […] Read more -

YubiKeys protecting critical IT infrastructure in Ukraine The Russian invasion of Ukraine is a battle in both the physical and the digital world. On both sides, information warfare plays a more critical part of the battlefield than any other war in human history, with the biggest attack vector and threat being weak login credentials. According to a Ukraine cybersecurity executive at a […] Read more -

The real reason legacy authentication doesn’t work for shared workstations Most organizations struggle with legacy authentication, with passwords and mobile-based solutions a source of security risk, high IT cost, and frustrated users. However, for organizations with shared workstations and shared device environments, these pain points are only intensified. Shared workstations—common across industries such as healthcare, manufacturing, retail and hospitality, financial services, energy, utilities, oil and […] Read more -

Shopping for cyber insurance? Six questions to ask before you call the insurer The cyberthreat landscape has always been worrisome, but today there are many more CISOs noticing new gray hairs in the mirror given an anticipated uptick in cyber attacks from nation states and other bad actors. Ransomware attacks and other forms of account compromise continue to grace the news every month with malicious actors – state-sponsored […] Read more -

Cyber Insurance requirements Cyber insurance requirements are fast changing in light of large financial payouts due to cybersecurity breaches. YubiKeys deliver phishing-resistant MFA to stop breaches. Read more -
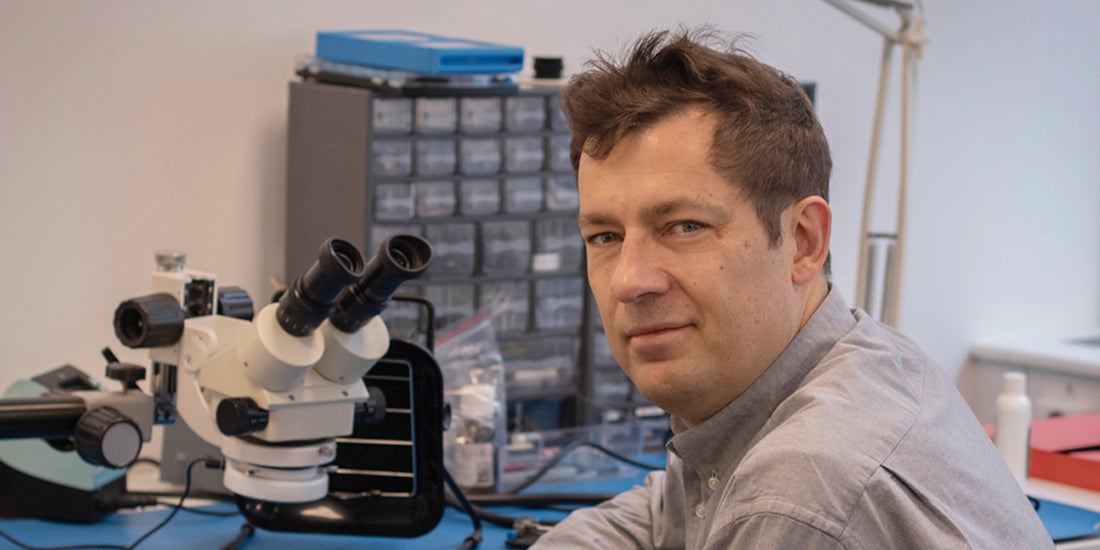
Q&A: Yubico’s Co-Founder & Chief Innovation Officer Jakob Ehrensvärd It’s not every day you get to hear a pioneer of internet security share why you and the rest of the world needs modern, reliable and easy-to-use Multi-Factor Authentication (MFA). If you want to understand phishing-resistant authentication and why it matters, there’s nobody better to ask than Jakob Ehrensvärd, Yubico’s co-founder. Jakob built his first […] Read more -

White House declaration: act now for cybersecurity attack protection Last week, President Biden made a statement that couldn’t have been clearer in its message regarding cybersecurity attack protection to the private sector: “If you have not already done so, I urge our private sector partners to harden your cyber defenses immediately by implementing the best practices we have developed together over the last year […] Read more -

Security considerations for the top 8 mobile device-restricted workplaces When looking at enterprises and organizations, there are many different business scenarios that can be present when addressing secure authentication. Whether those be shared workstations, remote workers, or even privileged accounts, there is one in particular that introduces its own difficulties: mobile device-restricted workplaces. It’s safe to say that there will always be workplaces which, […] Read more -

Supply chain security in 2022 The SolarWinds and Colonial Pipeline security breaches are two (of many) incidents that have made supply chain attacks go mainstream. The primary challenge for businesses is that supply chain defense isn’t easy given the hundreds, if not thousands of entry points that need to be monitored along the way. But there are best practices that […] Read more -

Privileged Access Management at CERN: Q&A with Dr. Stefan Lüders In an era of increasing cyber attacks, how do you balance the desire for unrestricted research freedom against the need to protect that research from cyber threats? This is the challenge faced by CERN, leaders in the scientific research community. Their solution? Provide a clear articulation of what constitutes privileged data, and create flexible security […] Read more