Today, together with the FIDO Alliance, we made a big announcement that paves the way to a passwordless future. We revealed the new Security Key by Yubico as well as our new Developer Program, both of which support the new FIDO2 open standard for passwordless authentication.
Why is this important? Think of a time when you have created a new account and didn’t have to create a new password.
For all of us, the account creation process for any application or online service has always started with the pairing of a password to your username, but with today’s announcement that is going to change. With FIDO2, it’s now possible to redesign the process to remove the weak link of passwords, and we’re gearing up to support the ecosystem and developer community to make that happen. Whether you’ve followed Yubico for years, or you’re just learning about us, read ahead to find out more about the significance of the FIDO2 project.
The FIDO2 Project
In 2011, Yubico invented the concept of a single security key to protect user accounts from phishing and unauthorized access, for any number of services with no shared secrets. We worked with Google to further develop this concept to what today is the FIDO U2F standard.
Now, Yubico has worked in collaboration with Microsoft on the evolution of the FIDO U2F authentication standard, to create FIDO2. With FIDO2, the Security Key with its strong authentication can now solve multiple use case scenarios and experiences:
- — second factor in a two factor authentication solution
- — strong first factor, with the possession of the device only, allowing for a passwordless experience like tap and go
- — multi-factor with possession of the device AND PIN, to solve high assurance requirements such as financial transactions, or submitting a prescription.
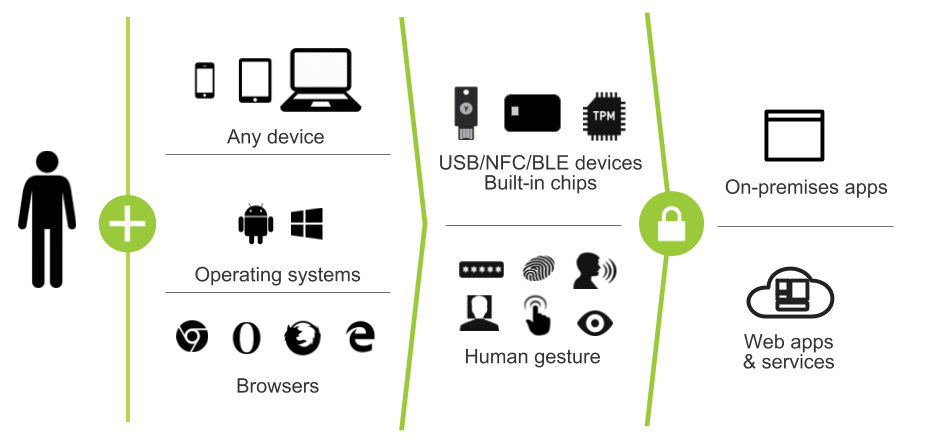
FIDO2 has already received support from the FIDO Alliance, World Wide Web Consortium (W3C), and all major web browsers to aid in its global standardization and adoption. With this foundation, FIDO2 is positioned to help services, applications, and enterprise organizations seamlessly transition to a more secure, easy to use replacement for the static password.
Read more about FIDO2 here. If you’re interested in developing with this new standard, you’ll need a Security Key by Yubico and we encourage you to sign up for FIDO2 updates as part of our newly announced Yubico Developer Program.
NEW Security Key by Yubico

The Security Key by Yubico delivers FIDO2 and FIDO U2F in a single device, supporting existing U2F two-factor authentication (2FA) as well as FIDO2 implementations.
The new Security Key by Yubico supports both the Web Authentication (WebAuthn) API, and Client to Authenticator Protocol (CTAP) which are required for FIDO2-based authentication.
FIDO2 and the Security Key are delivering on trusted, touch-and-go authentication for the modern, flexible and mobile workforce that is meeting the needs of our on-demand society. Together, these technologies will be integrated into many verticals including: retail, healthcare, transportation, finance, manufacturing, and more.
We will be demonstrating the new Security Key by Yubico and new FIDO2 functionality at the RSA South Expo hall at Booth #2241. You can purchase one up from our webstore today ($20 USD). Read more about the Security Key by Yubico here.
NEW Yubico Developer Program
This year marks the 10 year anniversary of the launch of the first YubiKey, that millions of users in more than 160 countries around the world love for its ease of use, security, and affordability. We made our YubiKeys available with free open source servers that encouraged adoption and growth of a thriving ecosystem of services supporting our technology. We’ve learned a lot from our partnerships, which is why we today announced a formalized Developer Program. This provides developers with the resources to rapidly integrate the YubiKey with mobile and computer login, across all our supported protocols including U2F, Yubico OTP, PIV-compatible Smart Card, OpenPGP, OATH (HOTP/TOTP), and the new FIDO2 Client to Authenticator Protocol (CTAP) specification, and the YubiHSM.
We encourage developers and security architects interested in FIDO2 to sign up for updates as part of the Yubico Developer Program, to get access to resources needed to aid in early implementations of the FIDO2 open authentication standard.


