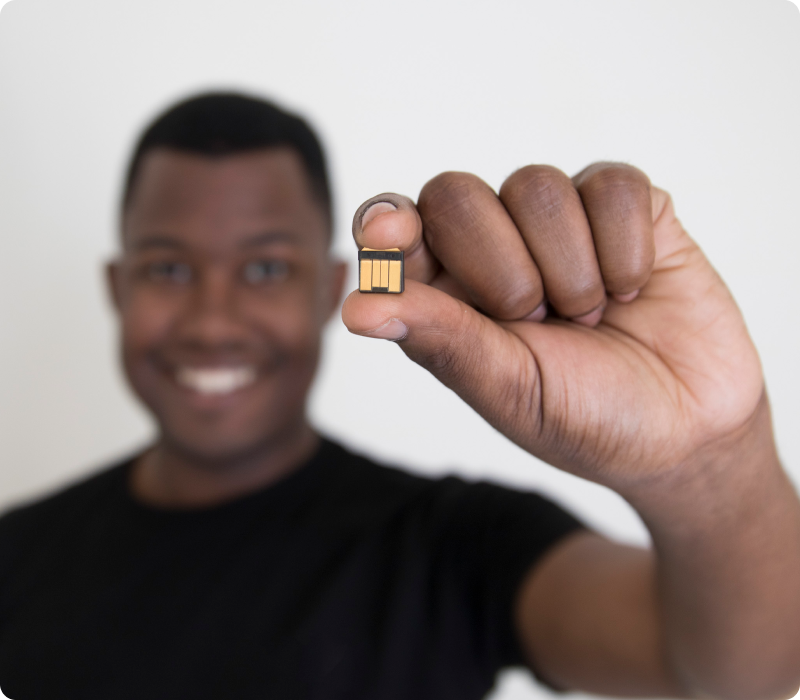
YubiHSM 2 and YubiHSM 2 FIPS
Game changing cryptographic protection for servers, applications and computing devices.
Not your traditional HSM
The world’s smallest HSM secures modern infrastructures other traditional HSMs with a bigger footprint simply can’t
Enhanced protection for cryptographic keys
Secure generation, storage and management of digital keys.
Rapid integration with hardware-backed security
A comprehensive cryptographic open source toolbox with support for PKCS#11.
Simplified deployment for organizations of all sizes
Ultra portable form factor at an affordable price secures a wide range of long-standing and emerging use cases.
| Is the YubiHSM 2 or YubiHSM 2 FIPS right for you? | |
|---|---|
| Do you need to secure your manufacturing process / supply chain? | Yes |
| Do you want to secure your software development process? | Yes |
| Do you need to secure your crypto currency environment? | Yes |
| Are you looking for an HSM that’s more cost effective than a traditional HSM? | Yes |
| Are you looking for an HSM that is compact and highly portable? | Yes |
| Looking for a FIPS 140-2 validated HSM? You may prefer the YubiHSM 2 FIPS Buy now | |
YubiHSM 2 and YubiHSM 2 FIPS Key capabilities

YubiHSM 2 and YubiHSM 2 FIPS highlights:
Game changing cryptographic protection for servers, applications and computing devices.
- Portable nano form factor with low-power usage
- Secure key storage and crypto operations on a tamper-resistant device
- Network shareable for use by applications on other servers
- Interfaces via YubiHSM KSP, PKCS #11 and native libraries
- Direct USB support beneficial for virtualized environments
- IP68 rated, crush resistant, no batteries required, no moving parts
- Enhanced control over multi-cloud security with Bring Your Own Key (BYOK) functionality
Enhanced protection for cryptographic keys
- Improve key management by preventing the local copying and distribution of cryptographic keys
- Defend against remote attacks and eliminate remote extraction of private keys by storing cryptographic keys securely on hardware
- Strong hardware-based security ensures the highest bar for protection of sensitive information and data
- Experience even stronger security with the ability to store YubiHSM 2 authentication keys on a YubiKey, to eliminate yet another password
- Asymmetric cryptography for wrapping of sensitive data for backups ensures no secrets are exposed even if wrapped data is sent over the internet to another location


Rapid integration with hardware-backed security
- Open source SDK enables rapid integration
- Frees developers to easily build support for hardware-based strong security into a wide array of platforms, applications and services
- Enables organizations to easily make the YubiHSM 2 features accessible through industry standard PKCS#11
Simplified deployment for organizations of all sizes
- Ultra-portable and fits easily into a front USB slot on computers and servers
- Secures modern use cases such as cryptocurrency exchanges, IoT gateways and proxies and cloud services
- Secures Microsoft Entra ID certificates
- Available in multiple form factors including nano, USB-A and USB-C
Secure your manufacturing and supply chain operations
| Looking to enhance security for the following areas? The YubiHSM 2 can help. | |
|---|---|
| Are you looking to secure your PKI environment, including protecting your certificate authority (CA)? | Yes |
| Are you looking to encrypt your files or databases? | Yes |
| Do you need to sign code or any digital artifact, such as firmware or an element embedded on an electronic device? | Yes |
| Looking for a FIPS 140-2 validated HSM? You may prefer the YubiHSM 2 FIPS Buy now I Download deployment documentation | |
Learn how YubiHSM 2 safeguards corporate secrets and secure manufacturing
Read this white paper to learn how manufacturing companies can protect supply chains and intellectual property with the YubiHSM.
YubiKey protects the world’s leading brands
Get Started

Learn about the HSM
Contact our sales team for a personalized assessment of your company’s needs.

Already have YubiHSM? Visit our support page for deployment guides and practical implementation considerations