Phishing-resistant MFA and passwordless for Healthcare
Modern phishing-resistant MFA and passwordless to secure patient data and drive compliance
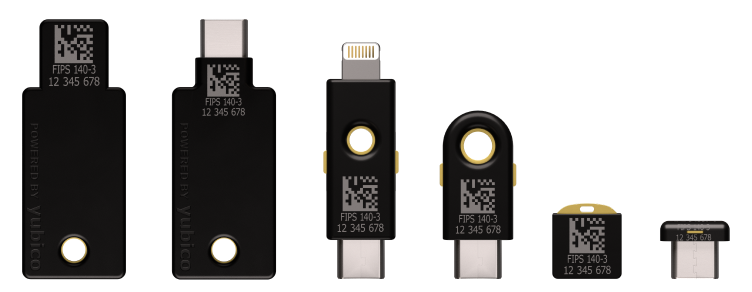
The YubiKey 5 FIPS Series will be FIPS 140-3 validated soon.
The ideal security key for phishing-resistant MFA and modern passwordless
Easy, efficient, strong authentication ensures compliance—securing highly sensitive patient information and high-assurance transactions.
Across the healthcare sector, organizations need solutions that can offer modern security capabilities, helping transition to a more secure, phishing-resistant MFA and passwordless workflow for a better user experience and overall efficiency.
The multi-protocol YubiKey with support for SmartCard/PIV and FIDO2 authentication protocols, offers phishing-resistant MFA and modern passwordless with exceptional user experience in a portable form factor. With the YubiKey, healthcare organizations can ensure that employees, contractors and end customers are always protected against modern cyber threats.
What is phishing resistant MFA?
Phishing-resistant MFA refers to an authentication process that is virtually immune to sophisticated attacks that could intercept or trick users into revealing access information.
As defined by the Federal Information Processing Standards (FIPS) 140-2 and NIST SP 800-63B, only two authentication technologies meet this requirement: the federal government’s Personal Identity Verification (PIV) standard/ SmartCard and the modern FIDO2/WebAuthn standard.
Modern phishing-resistant MFA for Healthcare with the YubiKey
Let us help you create a custom plan for your business!
Benefits from the phishing-resistant YubiKey

Protect critical apps and sensitive data
Legacy authentication such as username and passwords and mobile-based authenticators are leaving healthcare organizations exposed to modern cyber threats. Usernames and passwords are easily hacked, and mobile-based authenticators are highly susceptible to phishing attacks, account takeovers, SIM swaps and man-in-the-middle (MitM) attacks.
The YubiKey provides phishing-resistant two-factor, multi-factor, and passwordless authentication at scale. The hardware authenticator protects the private secrets on a secure element that cannot be easily exfiltrated, preventing remote attacks. YubiKeys are the only solution proven to stop 100% of account takeovers in independent research.

Provide the best user experience
Usernames and passwords, and SMS, OTP, and push notification apps don’t provide the best user experience. Users can get locked out of their accounts, and reliance on cell phone battery and network connectivity can cause delays in user access to critical patient data.
YubiKeys require no software installation, battery, or cellular connection, making them ideal for mobile-restricted environments and shared workstation environments that are common across healthcare. A user can simply insert the YubiKey into a USB port and touch the key to authenticate. YubiKeys also support tap-and-go authentication using NFC. When combined with a silicone wristband, the YubiKey can solve critical pain points around sanitation and efficiency.

Ensure compliance to global regulations
As a result of evolving cyber attacks, regulatory changes such as the CURES Act, revised HIPAA, EPCS (SUPPORT Act), 21 CFR Part 11, and various federal and state laws are introducing new security requirements related to user authentication, which passwords and legacy authenticators can no longer fulfill.
For regulated healthcare environments, YubiKeys are available in FIPS 140-2 validated form factors that meet the highest authenticator assurance level 3 (AAL3) requirements from NIST SP 800-63B.

Reduce IT support costs and drive high ROI
The combination of frictionless user experience, data breach prevention, mobile device and service cost savings, and the YubiKeys versatility with multi-protocol support results in high ROI. YubiKeys also enable self-service password resets, eliminating IT support costs related to help desk password-reset requests.
Yubico solutions, and flexible YubiKey procurement and deployment options through YubiEnterprise Subscription, you can experience an estimated 203% ROI over three years and, a reduction of password-related helpdesk support tickets by 75% by year 3.

READ THE WHITE PAPER
Modernize MFA and go passwordless across healthcare
Read the Yubico white paper to learn the challenges with legacy MFA and how to bridge to modern passwordless authentication.

BEST PRACTICES GUIDE
How to get started with phishing-resistant MFA to secure healthcare
Learn the six deployment best practices that can help your organization accelerate adoption of modern, phishing-resistant MFA at scale using the YubiKey.

WATCH THE WEBINAR
How to bolster your authentication strategy for PCI DSS 4.0
Learn about what this new standard means for you and how not all forms of multi-factor authentication (MFA) are created equal in terms of compliance and mitigating cyber risk.
Risk reduction, business growth, and efficiency enabled by YubiKeys
A recent Forrester Consulting Total Economic Impact™ (TEI) study commissioned by Yubico found that a composite organization representative of interviewed customers who use YubiKeys reduced risk of successful phishing and credential theft attacks by 99.9%, saw a drop in password-related helpdesk tickets by 75%, and experienced a 203% 3-year ROI with YubiKeys.
BUT…. all organizations are different. Enter your own company data to create a custom Dynamic TEI study and instantly see how Yubico’s solutions can help your organization!