What is Passwordless?
Ask ten security experts to define passwordless and you’ll get ten different answers. But Yubico’s definition is quite simple: “Passwordless authentication is any form of authentication that doesn’t require the user to provide a password at login.” Seems obvious, yes, but starting with that basic foundation is useful for knowing where to go next.
Passwordless definition
Passwordless is best thought of as a strategic direction for a company’s security to take. How fast you accelerate toward that goal all depends on how many steps are included in a passwordless strategic plan. Every company, depending on specific security context, is going to get there at a different speed — but the general threat landscape today dictates that they get there as fast as possible. Some may wave off passwordless as a buzzword or just a marketing term. But it speaks to something much deeper about how we secure our professional and consumer-based online experiences. So it’s worth discussing what kinds of strategies, technologies and authentication methods might go into a move toward a passwordless world. Of course “passwordless” is not a terminal state of being. No CISO is going to stand up one day and shout, “We’re passwordless, the journey is over!”
Passwordless lies at the end of a yellow brick road that many companies have already started walking down, looking for new technologies that take the password — and more importantly, forcing a human to remember that password — out of front-end authentication processes. We don’t currently live in a world that allows us to securely roam the Internet without any password being used on the back-end, but we are moving closer to that world every year.
How to go passwordless and passwordless security are already on the agenda for many CISOs and security professionals. The primary questions remain: when will it happen, how quickly and with what form factors and standards? The speed of cloud migration may dictate the speed to passwordless, too. “The more an enterprise leans into the cloud,” says Ant Allan, a VP at Gartner, “the easier true passwordless authentication will be, enabled by access management tools or native FIDO2 support. However, more complex enterprise technology environments and more diverse users will make it more difficult to adopt a single passwordless authentication approach.”
Why are passwords so ubiquitous?
Passwords are still with us because for decades they’ve provided what we needed. A password is a shared secret, and shared secrets give us portability, compatibility and interoperability. They allow us to move smoothly through our everyday digital experience, so why rock the boat and get rid of them? We’ll discuss some of the vulnerabilities later, but let’s go more into detail on what passwords actually give us:
Portability
The need:
We have many devices, accounts, Web-based services and work-related authentications to set up. We want something that makes access easy, simple and reliable.
Passwords provide:
A shared secret doesn’t need a lot of infrastructure, physical keys or cards, or other dependencies to make it work. If you know your password, or your device knows it, you have a seamless user experience.
Compatibility
The need:
You want an authentication method that works with every app and service, especially the new ones you might register for.
Passwords provide:
Passwords are universal, even if some of them have different policies or may layer additional second factors to authenticate.
Interoperability
The need:
We access the Web through all sorts of different channels and devices. For example, you might log on through an Xbox, iPhone, computer and tablet all on the same day to access different forms of content. You don’t want to have to upgrade your device or install client software each time you switch modes of access.
Passwords provide:
There’s nothing fancy about inputting a password or creating fields to accept them. Nearly every channel we use provides a password input, so we don’t have to put much thought or effort into the process. They just work.
What is the password paradox?
Passwords are like that old roommate you wish you could get rid of. You’ve been sharing space with them for so long that you’ve really grown tired of their annoying living habits. You’d like to get rid of them and find a better roommate, but they pay the rent on time and usually stay out of your way, so you resign yourself to the status quo. Too bad they often leave the front door unlocked when they leave the house!
We know that passwords offer weak security and a poor user experience, but they do perform a necessary everyday function. The password paradox is the full circle of password practice that leads to increasingly poor security and user experience. First, the desire to improve security leads to best practices of making passwords unique and complex. But those complex passwords, often still ineffective in fighting off phishing attacks, make the user more tempted to share those passwords or write them down to remember them. That increase in sharing in turn makes the password insecure, leading to more attacks, in turn leading to a need for increasing complexity. You see where this is going — it’s a vicious circle that never stops. Security and usability are at odds with passwords. Better security leads to a worse user experience, and vice versa.
What is the problem with passwords?
If you’ve ever tried to keep a secret in a small circle of friends or family, you know how hard it is. The only way to ensure a secret is never disclosed is to never share it with anyone. But that’s not how the real world works, we have to share things if we’re going to communicate. Or in the case of authentication, we have to have common sense ways of remembering our passwords. The more unique and complex we make them, the harder they are to remember. Rather than remember 50 unique passwords (impossible for most people) or use a password manager, many people will reuse passwords across accounts, opening up 50 possibilities for a breach when just one password is shared.
Password security issues, by the numbers
3.3 Billion
stolen credentials reported in 2017
81%
of data breaches from weak/stolen passwords
123456
the most commonly used password along with the word password.
21 hours
per person, each year, spent on password resets
20-50%
of helpdesk calls are for password resets
$70
the average estimated cost of a password reset
#1
support cost is password resets
“Passwordless login represents a massive shift in how billions of users, both business and consumer, will securely log in to their Windows 10 devices and authenticate to Azure Active Directory-based applications and services.”

What are password usability issues?
Password fatigue is real. The average person just has too many passwords to keep track of, and that is the fundamental usability flaw. In one survey, 70% of respondents said they have more than 10 password-protected accounts online, with nearly 30% having “too many to count.” Another Google survey found that more than half of the respondents use one “favorite” password for the majority of their accounts. Not all of those people have made that decision out of ignorance, the hassle factor is just too great when passwords are so numerous and so lengthy.
Passwords at their core are less secure, difficult to remember, and create the kind of friction during authentication that leads to a number of bad outcomes (aborted purchases online, wasted work time while waiting for password resets, lower work satisfaction metrics, etc.)
Dozens of surveys have shown that the usability problems aren’t just severe, they are resilient over time. One LastPass survey found that the fear of a breach is topped by an even greater fear: 59% of people said the fear of forgetting their passwords was the top reason they reuse the same or similar passwords for multiple accounts. Password reuse doesn’t seem to be improving, despite increased threats, because the fear of forgetting is just a human trait that remains a constant.
While there’s a commonly held misconception that adding greater complexity to a password makes it safer, many security experts will tell you that composition, complexity and length actually don’t have as much impact as you think. Passwords can be stolen and people often use common complexity patterns.
Password vs. PIN
Modern MFA technologies, including passwordless authentication, may require the user to put in a PIN instead of a password. You’ll never get to the end of the passwordless yellow brick road without being clear on the benefits of PINs over passwords. A password is transmitted and validated on a server, which means it can be intercepted or stolen. A PIN, often numeric, is local to the device and is never transmitted. Think of the old standby ATM card. When you enter your PIN, the number unlocks the card but is not stored anywhere else. Once unlocked, a separate strong cryptographic authentication ceremony is used to provide access. The PIN is tied to the physical card, which is why you have to select a new PIN when your debit card is stolen and you get a new card. The PIN can be a very simple and rarely, if ever, changing number, unlike passwords that need to become ever more complex to be safe, and changed every 90 days or per the security policy of the organization.
The connection to the local device is what makes a PIN so much more secure than a password. For that reason, PINs are often used in strong authentication setups. If you plan to one day use a biometric authenticator (e.g. something that uses a face or fingerprint to release the device-stored PIN), a PIN may still be part of that process because the authenticator needs a backup if the biometric process fails.
Here are a few key technical differences between the two:
| Passwords | PINS |
| Shared secret between a user and server | No shared secret, only used to unlock the physical device. A separate asymmetric/public key cryptography ceremony is used for authentication |
| Stored on a server, susceptible to breach | Stored local on device; not susceptible to remote attack (PIN unlocks authenticator) |
| Policy may demand frequent change | May never need to change |
| May require complexity; difficult to remember | May be short, simple, with no complexity requirement; easy to remember |
| Not many biometric applications | Used with biometrics for day-to-day, but is available as a fallback mechanism (with FIDO2) |
| Vulnerable to brute force attacks | Less vulnerable to brute force attacks and requires physical access to device |
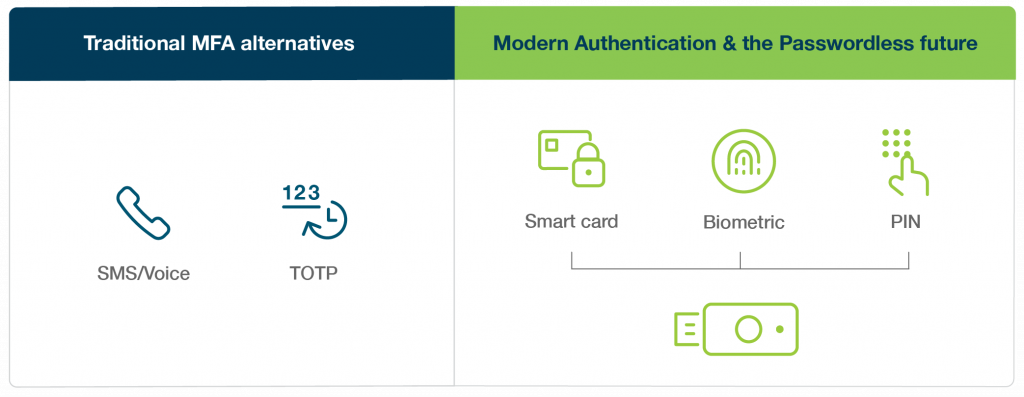
What kind of passwordless implementations exist?
There are few processes that have become commonplace as companies move down the passwordless road.
Let’s start with those that try to solve the usability problem of a password.
SMS
SMS verification is one form of many passwordless authentication solutions because you don’t need to remember a password. Usually, you’re sent a One-Time-Password (OTP) code valid for a short time to be used for authentication. Many people are getting too used to seeing these text messages sent to their phone, often in the form of a 6-digit numerical code. Even though it looks like a PIN, they are not as they are a form of a shared password that provides access. These are vulnerable to being intercepted so considered a weak form of authentication.
An additional vulnerability lies in the assumption that the user is in possession of the phone that is associated with the phone number. The phone number can be switched to other phones for the purpose of stealing SMS codes. SIM Swapping attacks are a serious problem where an attacker tricks the phone company to associate the phone number to their phone to receive the access codes.
Email Magic Link
This is also a commonly used way to circumvent having to remember a password. A unique link with an embedded token is created and delivered to a verified email address (we hope it’s verified and not compromised!) Clicking the link verifies the user for that particular service, and there may be an expiration time for that link.
You can even use SMS to deliver the magic link, but what you’re gaining in usability you may be losing in security. Both of these methods are highly susceptible to phishing. If a user is tricked into typing in a fake OTP or clicking on a “phishing bait” magic link, that user might just give away the store. You can read more about modern phishing techniques here.
Smart cards
A third, and perhaps the most familiar passwordless implementation, uses the trusty smart card. Government employees know these as PIVs (personal identity verification) and CACs (common access card). Smart cards are one of the most effective ways to protect against phishing. The user must insert their smart card into a reader, and validate the smart card with a unique PIN. This is one of the best ways to stop remote phishing attacks, but traditional smart cards aren’t very portable, compatible or interoperable. It can be complex and costly to implement traditional smart cards at scale, making them hard to use and inaccessible for most individuals and many businesses.
What’s the relationship between open standards and passwordless implementation?
All the major industry organizations along with authentication experts, like Yubico, recognized the need for a better passwordless solution. They came together and built the FIDO2/WebAuthn passwordless standard that is becoming the way to achieve secure passwordless authentication. A solid open standards foundation is needed in order to make FIDO2/WebAuthn possible and ubiquitous across devices, browsers and platforms.
A rich open standards ecosystem helps solve the issues we’ve already identified with security while keeping all those usability benefits we still want — portability, compatibility, and interoperability. Yubico advocates for open security standards because we know that the yellow brick road to a form of passwordless security is paved by open standards like WebAuthn and FIDO. Collaboration with tech giants (Google, Microsoft and Apple, for example) is key to making sure standards are integrated into the operating systems and browsers we use every day. Seamless integration of a FIDO2 passwordless experience won’t work without standards across devices, apps, and services that do not require additional proprietary software. If the success of the passwordless strategy is going to rely on improved user experience, then having broad interoperability across devices, browsers and platforms is a prerequisite.
Identity and access management (IAM) solutions (e.g. Okta, Duo Security, Ping Identity) have embraced open standards by layering on top of commonly used platforms and operating systems, to deliver the functionality and scale that enterprises need to adopt strong passwordless authentication for their applications and services.
Passwordless options provided by IAM platforms often rely on a mobile authentication app, an alternative non-WebAuthn passwordless / FIDO passwordless solution, to help improve user experience on legacy systems. While mobile authentication may be a step up from passwords, they are still phishable, so the best IAM platforms offer native support for FIDO-compatible hardware security keys.
What kind of credentials are used in a passwordless environment?
New passwordless authentication methods and keys are constantly evolving, but you can organize today’s methods into three main categories.
Hardware authentication devices
These “hard tokens” use a physical device — a smart card, a bluetooth token, or a keyfob like the YubiKey — to authenticate users.
Advantages: Circumvents needing any kind of password, instead using the “something you have” concept to identify users. A unique PIN can be paired with the token for increased security. Can be very durable and last a long time which improves total cost of ownership (TCO).
Disadvantages: As with any physical token, there can be added complexity in both IT support and delivery of the product itself. They can be lost or stolen, requiring even more IT support to re-ship and activate.
Biometric scanners
Biometric uses something uniquely biological (a face, a fingerprint, an iris, or other feature) as a credential.
Advantages: As with a hard token, no password is required, though often a PIN is necessary as a backup in case of a device failure.
Disadvantages: Though we think of biometrics as passwordless and therefore more secure than passwords, it’s worth remembering that biological data (facial recognition, fingerprints, etc.) are still stored on servers and checked for authentication. That means that hackers can still access it with a breach, so it is vulnerable to having that data falsified. Biometric scanners could be fooled by deep fakes. The industry is looking for ways to store more biometric data locally to defend against these vulnerabilities. The biometric information for FIDO based authentication is stored locally.
Software tokens
“Soft tokens” are stored on devices like phones as access credentials. They can come in many forms: knowledge-based authentication, one-time-password (OTP) by SMS (but we’ve already discussed SMS vulnerabilities), or biometric using the device’s own scanner.
Advantages: Like the other two methods, soft tokens dodge the need for a password by acting as “something you have” (and we know that, for better or worse, we are almost always with our phones).
Disadvantages: Phones can be stolen or cloned, and they tend to run out of power or mobile service range at the most inopportune times. Phone restrictions, legal and operational, can also make them not suited as an authentication mechanism. When you rely on a single device to store that soft token you create a single point of failure. The added expense of IT support and the high cost of backup mobile devices are something to consider when going in this direction.
What does FIDO2 offer and why is it important for implementing a form of passwordless authentication?
FIDO2 is a combination of two open authentication standards. Client to Authenticator Protocol (CTAP2), hosted by the FIDO Alliance, and the W3C Web Authentication specification (WebAuthn API). CTAP is an application layer protocol used for communication between a client (browser) or a platform (operating system) with an external authenticator. Yubico is a core contributor to the CTAP2 and WebAuthn. FIDO2 was developed with a passwordless journey in mind. It will make it easier for users to leverage common devices and easily authenticate to online services in both mobile and desktop environments. .
FIDO2 is built on the work of FIDO U2F, the previous standard, and is based on public key cryptography. FIDO2’s public/private-key credential — one that can’t be reused, replayed, or shared across services — protects users from phishing and is not subject to phishing, session hijacking, malware attacks, “man-in-the-middle” (MiTM) attacks or server breaches. Fortunately it is backwards-compatible with FIDO U2F and supports hardware authenticators that use either U2F or CTAP2.For managers who want to move to FIDO2/WebAuthn passwordless, FIDO2 enables strong passwordless multi-factor authentication (MFA). And FIDO-based hardware security keys can also enable second factor authentication, adding a layer of security on top of a password. What an open standard does best, other than strengthening security, is giving security staff more flexibility in how to enhance the security posture of the organization using either strong 2FA or strong passwordless MFA. Strong authentication can be enabled on existing phones and computers, for many authentication modalities, and with different communication methods including USB, Lightning and NFC.
FIDO2’s flexibility as an open standard also helps move you further down the road to passwordless. But we are still in the early stages of FIDO2/WebAuthn passwordless. Many organizations can consider smart card passwordless as well to solve for the majority of their use cases.
A passwordless enterprise can mix and match components and devices depending on security context. For example, security-conscious companies like a large bank, may want to consider using a PIN with a security key. But another organization may opt to not use a PIN as part of the login flow.
Strong security
Replaces weak passwords with strong hardware-based authentication using public key crypto to protect against phishing, session hijacking, man-in-the-middle, and malware attacks. No secrets are shared between services.
Open standard
Open standards provide flexibility and product choice. Designed for existing phones and computers, for many authentication modalities, and with different communication methods including USB and NFC.
Step up authentication
For services requiring a higher level of authentication security, FIDO2 supports step up authentication allowing use of strong single factor (passwordless), two-factor and multi-factor authentication for additional protection.
The journey to passwordless
The most important thing we understand about the road to passwordless is that every company sits at a different mile marker. CISOs must design a security strategy that speaks to the enterprise’s particular infrastructure, mission-critical functions and threats, and overall security and usability goals.
Enterprises have all kinds of environments — on-premises, hybrid, or cloud-first, for example. Those environments contain several forms of legacy authentication, including 2FA, legacy MFA tools like SMS, and mobile authentication. That journey will take a different path depending on the organization — smart card passwordless, FIDO2/WebAuthn passwordless or passwordless in conjunction with an IAM solution or partner are all good options.
Not every passwordless setup will look the same. Some won’t use passwords on the back-end authentication flow, opting for a PIN or biometric authentication to validate identities. But another implementation might still need a password on the back-end, perhaps to be used when creating or recovering an account. The user experience is still passwordless even though some back-end systems have not yet matured to a passwordless model. In this instance, the user should not need to provide it when logging in, validating through other means like a hardware security token or mobile authentication app.
Hardware keys can come in handy as they are designed to support the broadest set of security protocols. One company might just want to use hardware keys as a second factor on top of a password. But in a different context it could be deployed in a passwordless environment with IAM partners as a smart card or a FIDO2/WebAuthn security key.
New research on work-from-home MFA adoption and passwordless
Research on how work-from-home policies have driven MFA adoption shows that, while the new hybrid and full-remote work environments have boosted spending and interest, there is still a long way to go for many industries. MFA adoption is only one step on a journey to passwordless.
451 Research’s study, Work-from-Home Policies Driving MFA Adoption, But Still Work to be Done, found that COVID-19 has spurred rapid growth in multi-factor authentication adoption and spending. Here are a few important findings on that front:
- MFA is the top security technology to be adopted (by 49% of respondents) as a reaction to COVID-19.
- Nearly three out of four of respondents (74%) plan to increase spending on MFA, and that proportion is greater in retail (81%) and financial services (80%).
- Half of all firms are increasing spending on MFA by more than 10%.
- Half of firms have restricted the use of usernames and passwords or have multi-factor authentication adoption as a direct reaction to COVID-19.
While MFA is not a “one-size-fits-all” proposition, it’s clear that spending is accelerating on MFA adoption, one of the first steps to passwordless. Additionally with all the attacks on SMS, OTP and mobile app based MFA, phishing resistant MFA, such as FIDO, is receiving more attention and in some industries becoming a requirement.
What obstacles to MFA remain?
When firms were asked about what obstacles they’ve encountered to MFA adoption, the human factor was cited. User experience (43%) and complexity (41%) were seen as obstacles to adoption, followed by cost at 36%. Alternatively, 57% of respondents listed increased security as the number one reason for multi-factor authentication adoption.
Interestingly enough, mobile MFA methods continue to rank as most popular, despite increased vulnerabilities:
- Mobile one-time password (OTP) authenticators are still the most popular MFA form factor (58% of respondents), with single-gesture, phishing-resistant USB security keys ranking lowest (40%).
- Most surprisingly, 41% of respondents still rely on SMS authentication and only 22% perceive security as an issue with SMS authentication.
- Privileged admins and IT staff are the most likely group to use MFA (79%), while organizations are less likely to implement MFA for non-IT internal staff. Unfortunately, despite the increased use of MFA, privileged admins are still most reliant on usernames and passwords (58%) as an authentication method, followed by mobile OTP authenticators (53%).
The survey demonstrated that, even if multi-factor authentication adoption best practices are not there yet for all enterprises, plans are in the works this year to push passwordless authentication forward. Roughly one third (34%) of respondents have already deployed passwordless technology, and 27% report having passwordless authentication in pilot.
Educating users is key to making MFA happen
Ongoing migrations to the cloud, digital transformation projects, and extended work-from-home policies accelerated the pace of MFA adoption and spending in 2021, and that trend is likely to continue through the decade. There’s a learning curve on any new technology, but enterprises can do practical things to quicken the pace of adoption.
Educating employees, focusing on a seamless user experience, and setting aside significant budgetary resources for adoption are all ways to push MFA forward and reduce ongoing threats. The post-pandemic era won’t be any safer than before the pandemic — in fact, the threats will have grown. The move to remote work is opening up new vulnerabilities, and the enterprise can’t be caught flat-footed when inevitable breaches and attacks happen.
Find out more about Yubico’s passwordless solutions here.
Get started

Find the right YubiKey
Take the quick Product Finder Quiz to find the right key for you or your business.
