Tag: Microsoft
-

Contact Us passwordless Read more -

Building cyber resilience with Yubico and Microsoft In today’s digital landscape, cyber threats are evolving at an unprecedented pace: every second, a phishing attack takes place. In fact, over 80% of these attacks are the result of stolen login credentials and almost 70% of phishing attacks relied on AI last year alone. Recent data from Microsoft Entra also reveals a staggering increase […] Read more -

Navigating cyber threats: Building resilience with Yubico and Microsoft Join us to learn what Chad Thunberg, Yubico CISO, and Derek Hanson, Yubico VP of Alliances, have to say about cyber resiliency. Read more -
Yubico Enrollment Suite for Microsoft users is here: Meet Yubico at Microsoft Ignite 2024 On the heels of announcing the availability of Yubico Enrollment Suite for Microsoft users today, we’re excited to be back at Microsoft Ignite in Chicago this week to meet with all our valued customers and partners. If you’ll be at the conference, be sure to visit us at booth #333 to see live demos of […] Read more -

Yubico Announces Yubico Enrollment Suite for Microsoft users, a Turnkey Passwordless Onboarding Experience Enterprise users further empowered to be phishing-resistant and go passwordless on day one SANTA CLARA, CA and STOCKHOLM, SWEDEN – November 19, 2024 – Today Yubico (NASDAQ: YUBICO), the leading provider of hardware authentication security keys, announced the availability of Yubico Enrollment Suite for Microsoft users, including Yubico FIDO Pre-reg and the new YubiEnroll. These […] Read more -

Streamline Phishing-Resistant MFA: Simplified Passkey Provisioning with Microsoft and Yubico Join us as we explore the seamless adoption of phishing-resistant multi-factor authentication (MFA) through Microsoft’s new Entra ID passkey (FIDO2) provisioning APIs. Read more -
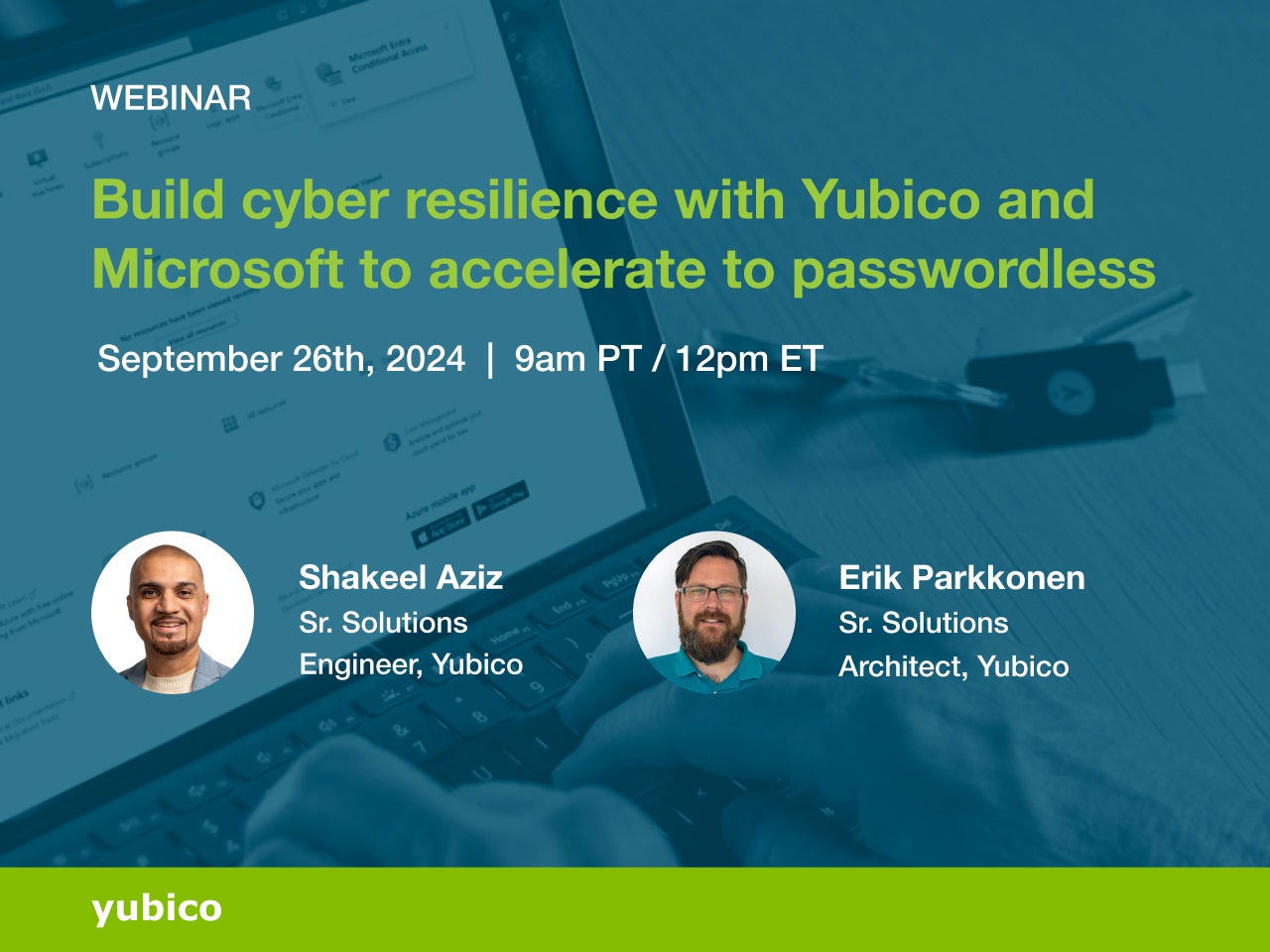
Build cyber resilience with Yubico and Microsoft to accelerate to passwordless Join us as we investigate lessons learned from incidents such as Crowdstrike and MGM Grand, and examine different passkey solutions and how they fit into building a resilient, phishing-resistant organization. Read more -
Simplifying break glass account security with YubiKeys Break glass accounts are crucial accounts that provide access to critical systems during a variety of emergencies. Microsoft’s recent announcement on the enforcement of multi-factor authentication (MFA) for Microsoft Entra ID sign-ins highlights the impact on break glass accounts and improved security postures: “We have heard your questions about break glass or ‘emergency access’ accounts. […] Read more -
Microsoft Entra ID strengthens security with FIDO2 APIs Yubico has worked closely with Microsoft for over a decade to keep businesses around the world and the Microsoft solutions they use both secure and phishing-resistant. Recognizing the importance of multi-factor authentication (MFA), Microsoft recently mandated that MFA be used by all Azure users – a critical move to require stronger authentication for end users […] Read more -

Works with YubiKey Spotlight: Fortifying Microsoft environments by fostering phishing-resistant users In today’s digitally interconnected world, Microsoft products serve as the backbone for countless industries and innovations. Through a cohesive ecosystem of enterprise-focused tools like Copilot, Microsoft 365, Azure, and Entra ID, Microsoft enables businesses to streamline operations and enhance productivity. These tools have fostered technological innovation, empowering organizations to stay ahead in a competitive landscape […] Read more