Tag: federal government
-

Yubico joins industry cybersecurity leaders at White House symposium to collaborate, discuss top security challenges and solutions Last week, several Yubico leaders traveled to Washington, DC to attend the White House’s symposium focused on modernizing authentication in support of Executive Order 14028 on Improving the Nation’s Cybersecurity, and the OMB Memo M-22-09 describing the Federal Zero Trust architecture. This event, organized by the Federal CIO & CISO and the Cybersecurity and Infrastructure […] Read more -
Federal Government Deployment Best Practices Guide Learn the six deployment best practices that can help your agency accelerate adoption of modern, phishing-resistant MFA at scale using the YubiKey. Read more -

NIST SP 800-63-4: What the new phishing-resistant definition means for federal agencies The recent drafts from National Institute of Standards and Technology (NIST) around cybersecurity highlight important updates on where the government is moving on technology and the focus on increasing security against cyber threats. This is because NIST’s primary goal is to develop and disseminate the standards that allow technology to work seamlessly and businesses to […] Read more -

Implications of outdated federal identity strategies Join Yubico and our esteemed panel for a roundtable discussion on challenges with current ICAM strategies and what’s needed for the makings of a modern identity strategy to enable digital modernization and cyber risk reduction. Read more -

A new White House directive: Phishing-resistant MFA! The US Government’s Office of Management and Budget recently issued its Zero Trust Strategy, which would require that Federal agencies only use phishing-resistant multi-factor authentication. This strategy comes on the heels of a number of other actions from the Executive Office of the President including a cybersecurity executive order in May. This executive order directed […] Read more -

How the YubiKey meets US Government regulations | Yubico Learn how the YubiKey, a DOD approved alternate authenticator meets federal PIV/CAC requirements and government compliance regulations. Read more -
Modern Authentication for the Federal Government – Yubico Learn how DOD approved hardware security keys such as the YubiKey are ideal to fill PIV and CAC related authentication gaps across the federal government, and meet the MFA mandate in the Biden Executive Order 14028. Read more -

Portable root of trust for government The YubiKey is a portable root for remote workers, non PIV/CAC eligible workers, mobile/BYOD, and shared devices/workstations. Read more -
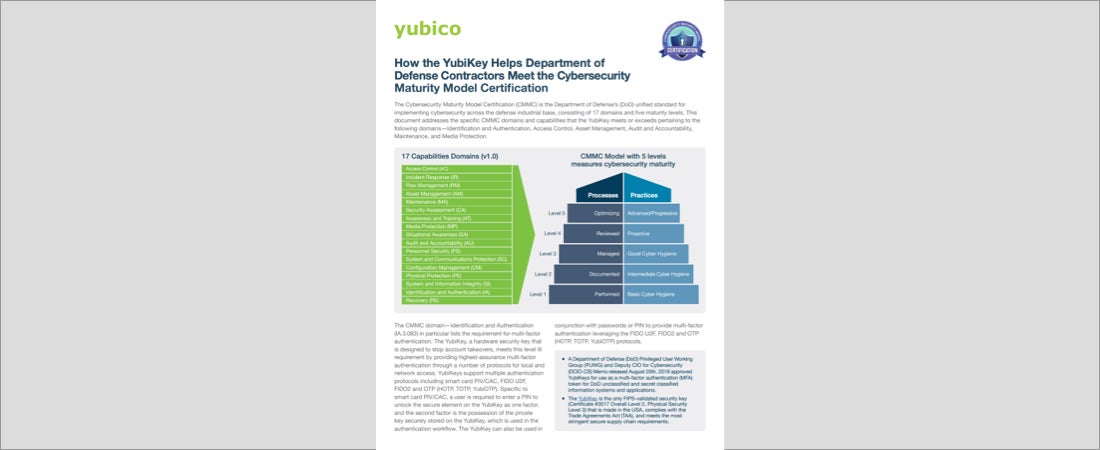
How the YubiKey Helps Department of Defense Contractors Meet the Cybersecurity Maturity Model Certification The CMMC is the Department of Defense’s unified standard for implementing cybersecurity. Read more -
DUO Federal partner brief Duo and Yubico together satisfy government guidance. Read more