Tag: federal government
-
YubiKey 5 FIPS Series and YubiHSM 2 FIPS are now FIPS 140-3 validated: What it means for high assurance security Editor’s Note: This blog has been updated as of June 4, 2026 to reflect YubiHSM 2 FIPS 140-3 validation With the growing threat of Generative and Agentic AI, where phishing and other sophisticated attacks have become faster and more targeted than ever before, federal agencies and regulated industries need to protect all of their users […] Read more -

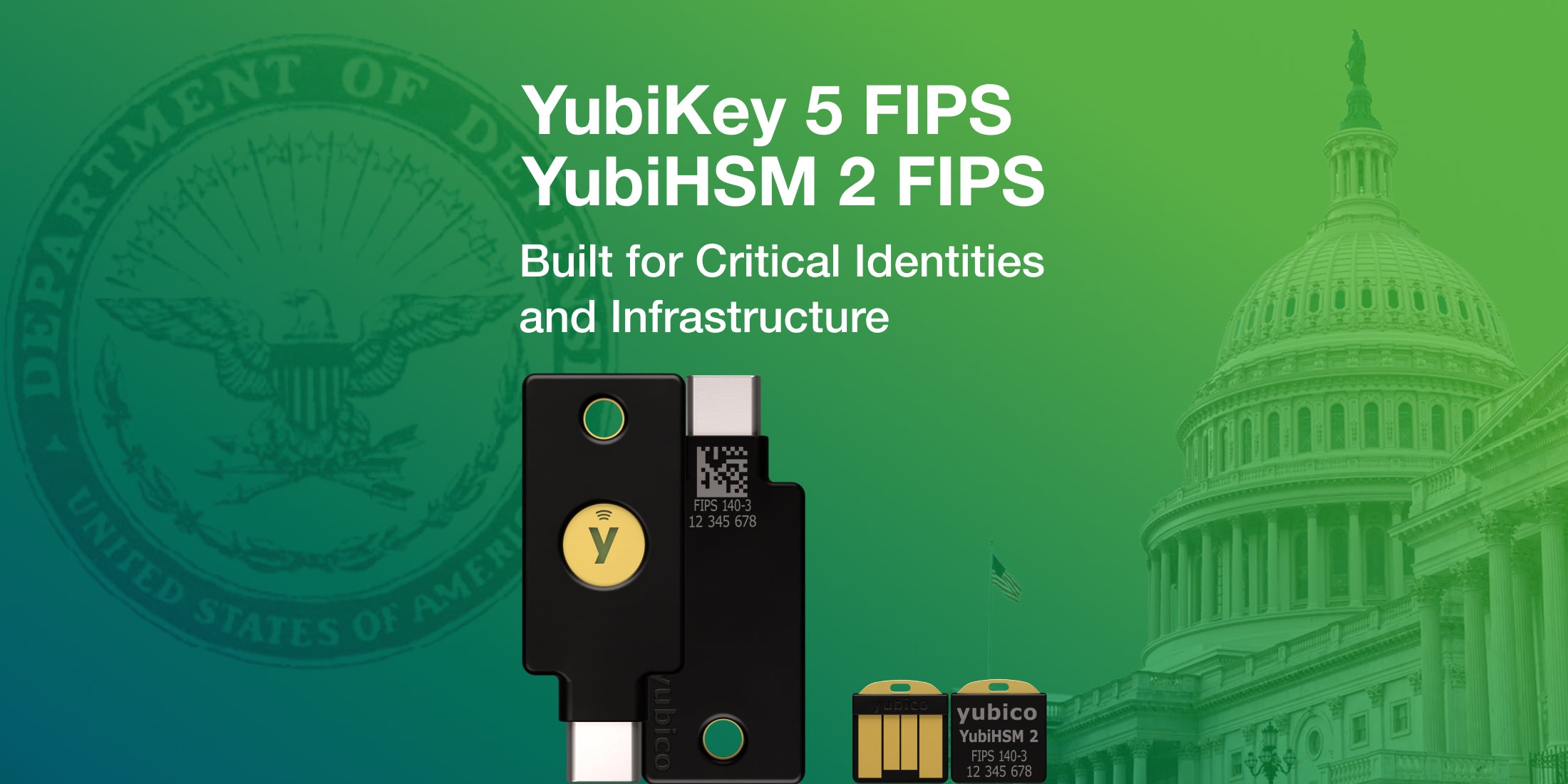
Yubico Announces Upgraded YubiKey 5 FIPS Series, Now FIPS 140-3 Validated YubiKey 5 FIPS Series uniquely recognized in DoD guidance for hardware-based FIDO2 passkeys, bridging modern authentication with existing identity systems SANTA CLARA, CA and STOCKHOLM, SWEDEN – May 26, 2026 – Yubico (NASDAQ STOCKHOLM: YUBICO), the pioneer of phishing-resistant authentication and creator of the most secure hardware-backed passkey, the YubiKey, today announced the certification of […] Read more -

Cybersecurity in 2025 – part two: Insights and predictions from Yubico’s experts In part one of our 2025 cybersecurity predictions, we highlighted insights from our experts on the topic of passkeys, digital identity wallets and the threats of AI-driven phishing – areas that saw a lot of focus in 2024, and ones that we expect to continue being a major focus this year. If you missed our […] Read more -

National Security Memorandum on AI: Key takeaways and recommendations Late last week, the White House issued a National Security Memorandum (NSM) on Artificial Intelligence (AI) which aims to ensure that ongoing and future advancements in AI technologies are beneficial to the US public. The memorandum also ensures that the US remains the top location to incubate and innovate in this developing space. Yubico applauds […] Read more -

Securing mobile web app browsing for the U.S. military: Q&A with Jason Christensen and Alex Antrim We’ve heard from customers and Yubico employees that have experienced first hand how difficult it can be for government employees to remotely and securely access essential web services like email, MyPay, and Defense Travel System. In the past, they would typically be required to login to a desktop, making access on the go essentially impossible. […] Read more -

Straxis and Yubico launch secure mobile web app to access essential U.S. military email, pay and travel services SANTA CLARA, CA, STOCKHOLM, SWEDEN and TULSA, OK – July 15th 2024 – Yubico, the leading provider of hardware authentication security keys and Straxis, a mobile application provider, today announced the availability of a new Secure Web browsing application called MilSecure Mobile. This application can be adopted by any Defense Department (DOD) organization to enable […] Read more -
Securing federal systems integrators and the defense industrial base with modern authentication FSIs have access to critical systems and hold large volumes of sensitive and Controlled Unclassified Information (CUI), making them targets of sophisticated cyber attacks. Any MFA is better than a password, but not all MFA is created equal. Download the visual industry brief to learn how FSIs and the DIB can protect themselves with modern, phishing-resistant multi-factor authentication (MFA). Read more -

Meeting the Sept 2024 White House phishing-resistant MFA deadline Learn best practices from government executives on their agencies’ journeys, how they navigated challenges and pitfalls to achieve compliance and what steps your agency can take right now to show intent and progress toward phishing-resistant MFA. Read more -
Securing Federal Systems Integrators with modern authentication Learn how Federal Systems Integrators (FSIs) can modernize their authentication stack and create phishing-resistant users and systems to protect against modern cyber threats. Read more -
Enhancing Federal Cybersecurity Explore our infographic on YubiKey’s phishing-resistant multi-factor authentication (MFA) solutions tailored for the federal government. Read more