Tag: authentication
-
Accelerate YubiKey adoption at scale Learn deployment best practices to enhance your security posture with phishing-resistant MFA Read more -

Laying the groundwork for continuous authentication Continuous authentication is an emerging concept—a future ‘nirvana’ state of security that would provide the capability to validate a user’s identity in real-time as they maneuver between systems, applications, and devices. In theory, continuous authentication solutions would use risk signals from a variety of monitoring sources to authenticate users, identify potential threats and proactively remediate […] Read more -

Yubico Releases MFA Guide in Recognition of World Password(less) Day PALO ALTO, CA and STOCKHOLM, SWEDEN – May 4, 2022 – In recognition of World Password Day, Yubico, the leading provider of hardware authentication security keys, today issued a multi-factor authentication (MFA) guide to help better define common and new industry terms, as well as the standards that are supporting modern authentication. While it is […] Read more -
Making sense of the alphabet soup within authentication and modern MFA terminology The vast majority of all cyberattacks start with stolen login passwords or other credentials. In a world that is moving to the cloud, our work, personal and government communication systems have become more accessible and vulnerable for anyone on the internet. Of all the different cyberattacks, credential phishing is by far the largest problem and […] Read more -

YubiKeys protecting critical IT infrastructure in Ukraine The Russian invasion of Ukraine is a battle in both the physical and the digital world. On both sides, information warfare plays a more critical part of the battlefield than any other war in human history, with the biggest attack vector and threat being weak login credentials. According to a Ukraine cybersecurity executive at a […] Read more -

The real reason legacy authentication doesn’t work for shared workstations Most organizations struggle with legacy authentication, with passwords and mobile-based solutions a source of security risk, high IT cost, and frustrated users. However, for organizations with shared workstations and shared device environments, these pain points are only intensified. Shared workstations—common across industries such as healthcare, manufacturing, retail and hospitality, financial services, energy, utilities, oil and […] Read more -

Shopping for cyber insurance? Six questions to ask before you call the insurer The cyberthreat landscape has always been worrisome, but today there are many more CISOs noticing new gray hairs in the mirror given an anticipated uptick in cyber attacks from nation states and other bad actors. Ransomware attacks and other forms of account compromise continue to grace the news every month with malicious actors – state-sponsored […] Read more -
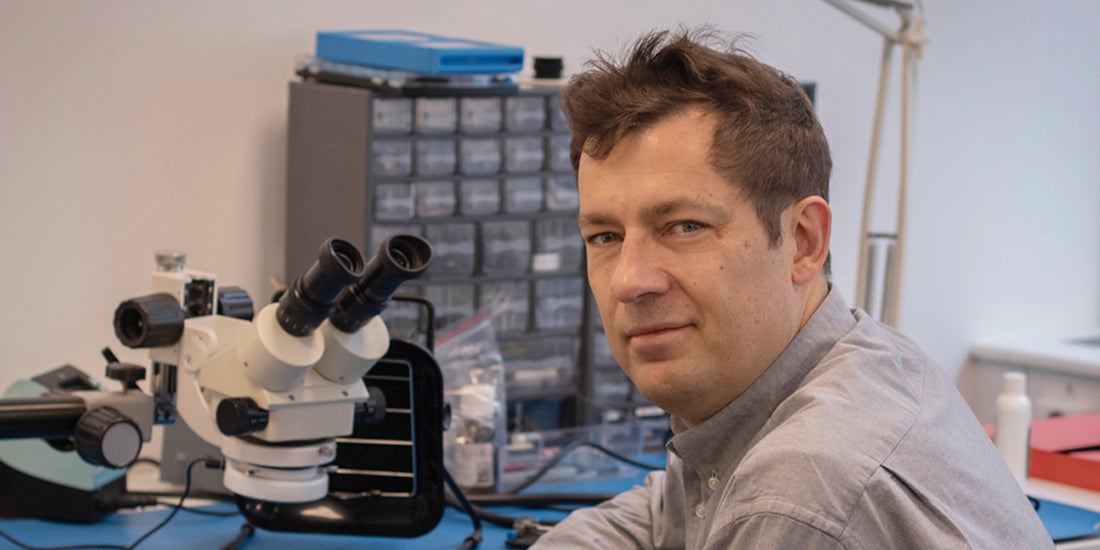
Q&A: Yubico’s Co-Founder & Chief Innovation Officer Jakob Ehrensvärd It’s not every day you get to hear a pioneer of internet security share why you and the rest of the world needs modern, reliable and easy-to-use Multi-Factor Authentication (MFA). If you want to understand phishing-resistant authentication and why it matters, there’s nobody better to ask than Jakob Ehrensvärd, Yubico’s co-founder. Jakob built his first […] Read more -

White House declaration: act now for cybersecurity attack protection Last week, President Biden made a statement that couldn’t have been clearer in its message regarding cybersecurity attack protection to the private sector: “If you have not already done so, I urge our private sector partners to harden your cyber defenses immediately by implementing the best practices we have developed together over the last year […] Read more -

Donating YubiKeys globally to those who need it most – Yubico With current events unfolding daily around the world, the reality that everyone can be affected by impending cyberattacks has set in. Now, individuals around the world are wondering how to stay secure during tumultuous times like this (and in the future). So, what exactly are the best ways to secure oneself online and mitigate the […] Read more