Today, the World’s Largest Developer Expo + Conference, DeveloperWeek 2018, opens at the Oakland Convention Center with thousands of developers participating from all over the globe. As a warm up for the conference, hundreds of developers participated in the DevWeek 2018’s hackathon and pulled an all-nighter on Saturday. Over 160 teams coded and collaborated for 24 hours. Our challenge was simple – incorporate YubiKey two-factor authentication (2FA) support into a standalone project for the chance to win a YubiCrown.
And the winning project is… PetitionThat
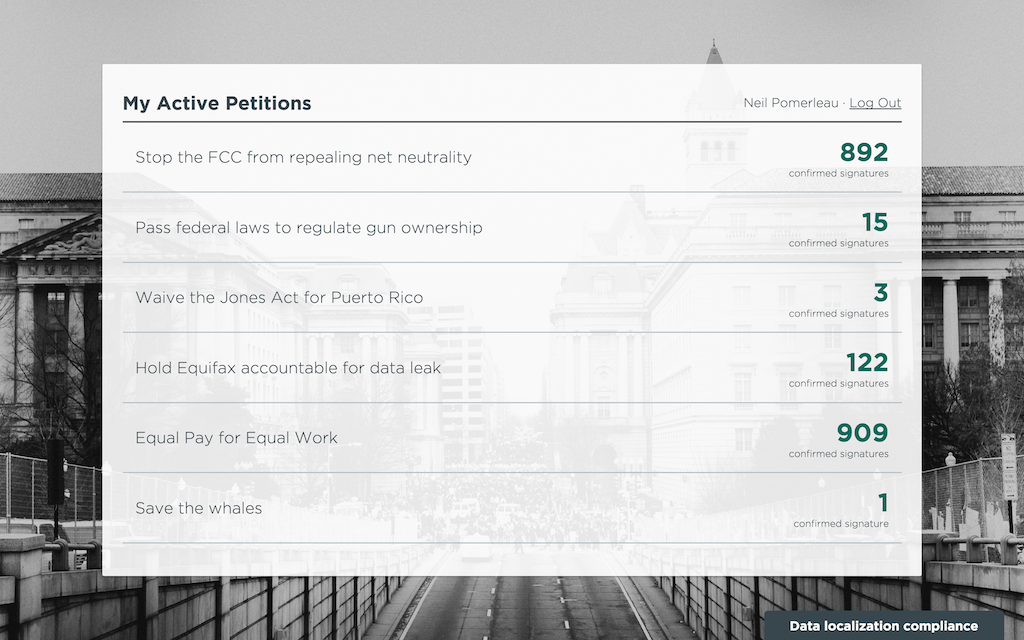
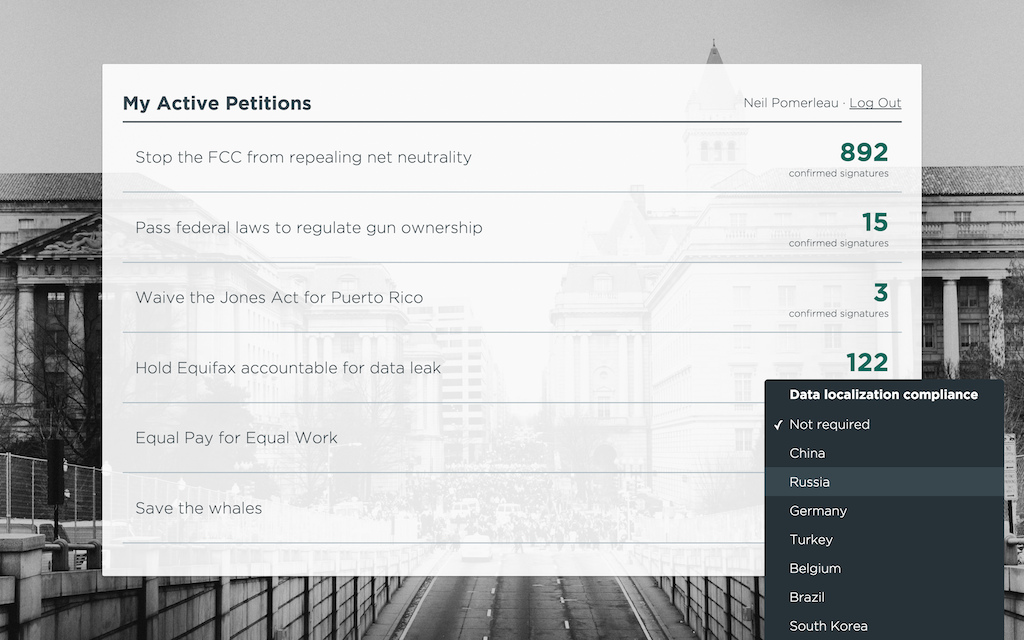
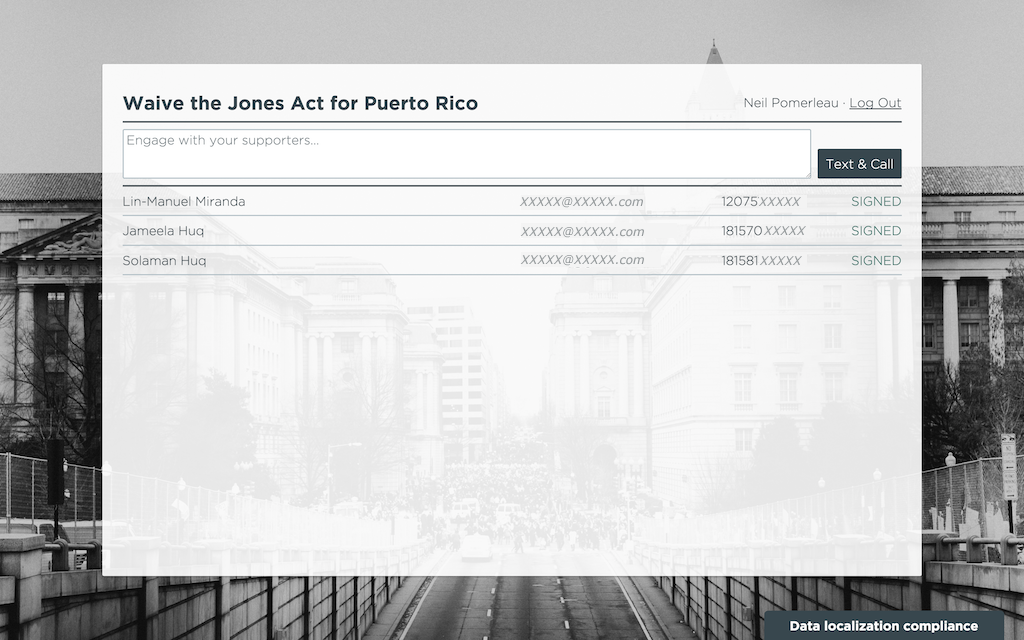
PetitionThat is a proof of concept that enables petition organizers to collect personal contact information about supporters for the purpose of continued outreach via text, phone, and email after the petition is signed. The platform’s inventors are siblings Solaman and Jameela, and their longtime friend Neil. The three Software Engineers joined forces to tackle an idea they’d been kicking around for awhile. They said, “it’s hard to find time to start a new project. When we saw the tools and technologies that were being promoted for the hackathon and how well they could service our idea, we knew that this was finally the time to build it.”
We were blown away by the progress the team made in just 24 hours. They successfully demonstrated secure login to the PetitionThat organizer platform using the YubiKey, real-time signing of a petition by a verified citizen, and re-engagement with the petition-signer over SMS. What really stood out, however, was this team’s fundamental understanding of the importance of privacy and security of the data they aim to collect.
Here’s what they have to say
“In the current political climate, too many people feel like they don’t have a voice. They wish they could improve some aspect of society, but they don’t really feel empowered to inspire change. People have traditionally proven support for an idea by gathering signatures, and today, there are petition websites that go further by leveraging the reach and connectedness of the internet. However, the problem with these sites is that there’s no verification of supporters. It’s too easy for petition organizers and supporters alike to game the system, creating a lack of confidence in the actual support for an idea,” shared the PetitionThat team.
PetitionThat solves this problem by filtering submissions that appear to be fraudulent and requiring a verified electronic signature for an individual to be counted among the supporters of a cause.
“Our service requires two-factor authentication from petition organizers before they can access the contact information of their supporters. We can associate a YubiKey with their account to make two-factor authentication as easy as pressing a button,” they said.
“The YubiKey gives us confidence that a petition organizer’s account isn’t being accessed by a malicious third party to collect personal contact information about supporters for a cause. And for organizers, it’s easier to use than other two-factor authentication methods, such as taking out a phone, waiting for a text message, and manually typing in a code. We get the security of two-factor authentication in a way that doesn’t slow down our users when they’re logging in.”
When asked about the experience of developing with and using the YubiKey and our developer tools, they said, “We explored a lot of new technologies when working on this project, including the YubiKey. The service advertises integration in less than an hour; it took us 15 minutes! It was so easy! There were some APIs from other hackathon sponsors that were so complicated or poorly documented that we had to re-architect our service to avoid using them. The YubiKey and YubiCloud just integrated seamlessly.”
Yubico applauds PetitionThat for their vision, hard work, and excellent performance at the DevWeek hackathon. To learn more about the YubiKey and how to deploy 2FA into your software or service, please visit https://developers.yubico.com/. If you are at Developer Week 2018, stop by and meet the Yubico team at booth # 513.