What do you get when you mix six hundred developers, twenty-four hours, twelve challenges and a mass of cash and prizes? The nation’s largest challenge-driven hackathon, hosted by DeveloperWeek in San Francisco.
Hackathon participants get just twenty-four hours to create a working proof of concept to solve some of the world’s most pressing problems. Yubico challenged developers with a user-centric approach to security. We were looking for the best integration of strong two-factor, multi-factor or passwordless authentication with the YubiKey to protect sensitive user information. Ten teams took on the challenge, all with excellent use cases and implementations, but we could only nominate one winner.
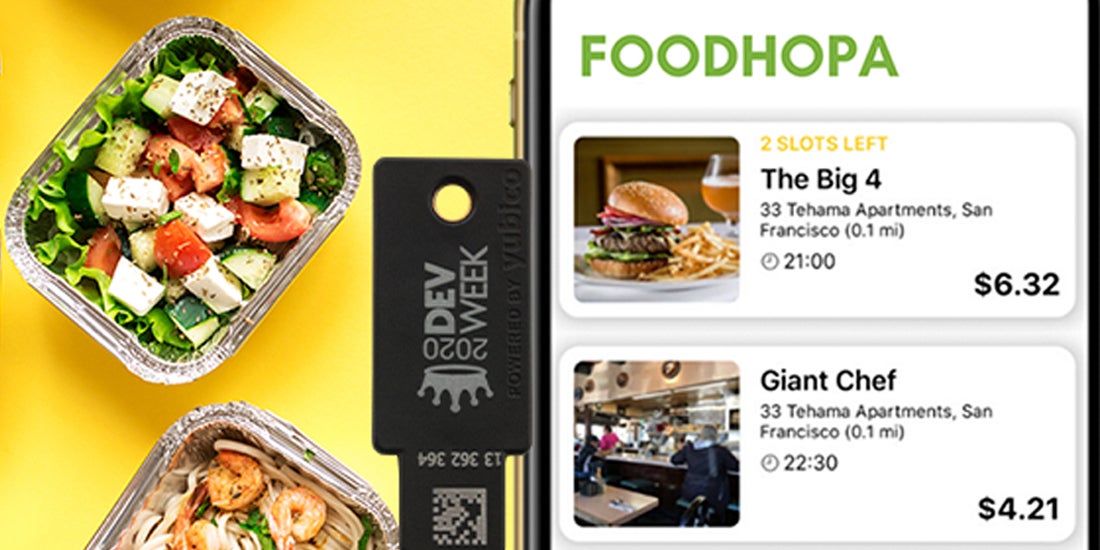
This year, Yubico chose FoodHopa as the winner of the 2020 Yubico DevWeek Hackathon Challenge. FoodHopa was born out of the simplest of concepts — how can environmentally conscious college students help reduce carbon emissions and save the world while feeding themselves and their friends, all on a shoestring budget?

Developed by engineering students Michael Winailan and Scott Sunarto, FoodHopa aims to match restaurants with surplus food to hungry eaters. The idea is that one driver delivers food to one centralized location instead of making multiple deliveries to multiple locations. By bringing eaters together, utilizing surplus food from restaurants, and reducing food delivery to one location, FoodHopa succeeds in reducing food waste and carbon emissions at the same time.
In just a few short hours, Michael and Scott built a mobile app for party-goers (eaters) and a web app for party hosts (drivers) and restaurant operators. Using a web-based management platform, restaurant operators can log in to the web app using a passwordless login flow with a YubiKey. This was all built on the WebAuthn standard.
When asked why they chose to go passwordless, the savvy students told hackathon judges that a passwordless login flow was important for three reasons:
- The food and beverage industry experiences high employee turnover rates, and YubiKeys are easy to re-issue to new employees.
- Inconsistent hourly work schedules make it challenging to remember a complex password.
- Memorizing complex passwords is hard, which results in weak or shared passwords among coworkers.
Enabling a passwordless login flow and providing YubiKeys for each restaurant employee that needs to interact with the web app ensures both the restaurant and their customers’ information is kept private and secure.
What’s next for these savvy students? The FoodHopa team hopes to productize their app and take it to the marketplace by implementing credit card payments through their app. By adding strong multi-factor authentication using YubiKeys into their payment flow, they will be well on their way to achieving PCI (Payment Card Industry) compliance.
Hackathon submissions don’t typically prioritize security—especially when the focus is on building an MVP as quickly as possible. Yubico has increased our participation in hackathons over the past few years in an effort to change that behavior, while also exploring better ways to empower non-security engineers to integrate strong authentication. If you’re hosting an upcoming hackathon, and would like Yubico to participate, please let us know at dev-mktg@yubico.com.
Are you interested in integrating security into the products, services, and applications that you’re building? Check out Yubico’s developer website to get started and sign up for the Yubico Developer Program mailing list to be notified of new documentation and resources, as well as get early access to SDKs and new products.