Within a few days of last year’s pandemic shut down in March, the business world knew something had permanently changed about the workplace. Millions of workers flooded out of traditional office environments, perhaps never to return. Security professionals worldwide scrambled to make transitioning to remote work painless, but in many cases they weren’t prepared for a bevy of challenges ranging from authentication to remote onboarding, to securing the supply chain.
The biggest challenge was pretty obvious: how to authenticate and secure the countless remote workers accessing corporate apps from outside the traditional perimeter?
Yubico teamed up with 451 Research to learn more about how multi-factor authentication adoption has fared during the pandemic. In our latest study, Work-from-Home Policies Driving MFA Adoption, But Still Work to be Done, we found that COVID-19 and the new work environment born from the crisis spurred a sprint toward multi-factor authentication adoption and increased spending. Nevertheless, there is still work to be done and several gaps still exist when it comes to MFA best practices.
COVID-19 spurred rapid growth in multi-factor authentication adoption and spending
Remote work is making us more vulnerable to attack — more than half (53%) of the survey respondents reported experiencing a breach in the past year. But there is some good news for MFA advocates: the virtual workplace has driven most firms to run toward MFA methods:
- MFA is the top security technology to be adopted (by 49% of respondents) as a reaction to COVID-19.
- Nearly three out of four of respondents (74%) plan to increase spending on MFA, and that proportion is greater in retail (81%) and financial services (80%).
- Half of all firms are increasing spending on MFA by more than 10%.
- Half of firms have restricted the use of usernames and passwords or have multi-factor authentication adoption as a direct reaction to COVID-19.
So the conditions on the ground are making more enterprises aware of increased threats and more willing to invest budget dollars to address them. However, there is no “one-size-fits-all” plan for MFA — each company will have to assess its security profile and adopt at its own pace. But the survey leaves no doubt that there’s an acceleration (and accompanying education process) toward MFA adoption.
Enterprises eye passwordless authentication, despite existing MFA gaps
The familiar challenges to MFA remain. When we asked firms about what obstacles they’ve encountered to adoption, the human factor was cited. User experience (43%) and complexity (41%) were seen as obstacles to adoption, followed by cost at 36%. Alternatively, 57% of respondents listed increased security as the number one reason for multi-factor authentication adoption.
Interestingly enough, mobile MFA methods continue to rank as most popular, despite increased vulnerabilities:
- Mobile one-time password (OTP) authenticators are still the most popular MFA form factor (58% of respondents), with single-gesture, phishing-resistant USB security keys ranking lowest (40%).
- Most surprisingly, 41% of respondents still rely on SMS authentication and only 22% perceive security as an issue with SMS authentication.
- Privileged admins and IT staff are the most likely group to use MFA (79%), while organizations are less likely to implement MFA for non-IT internal staff. Unfortunately, despite the increased use of MFA, privileged admins are still most reliant on usernames and passwords (58%) as an authentication method, followed by mobile OTP authenticators (53%).
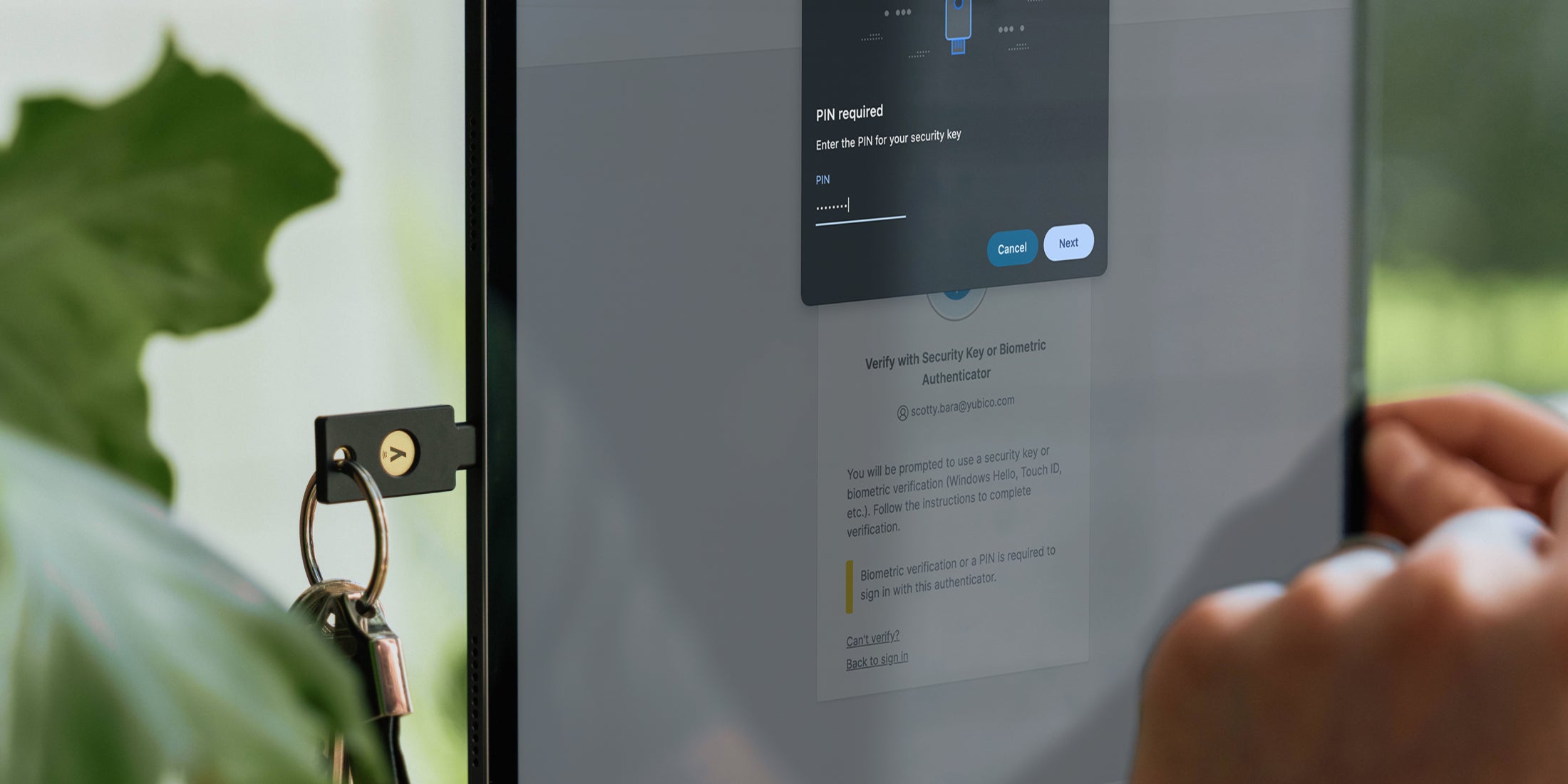
Based on research conducted by Google, it has been proven that hardware-backed security keys, like the YubiKey, protect against targeted phishing attacks 100% of the time in comparison to other MFA methods, and are up to four-times faster than mobile MFA methods, offering an improved user experience.
The survey demonstrated that, even if multi-factor authentication adoption best practices are not there yet for all enterprises, plans are in the works this year to push passwordless authentication forward. Roughly one third (34%) of respondents have already deployed passwordless technology, and 27% report having passwordless authentication in pilot. Of course, not all forms of passwordless authentication are created equal, but this shift further demonstrates the strong desire among enterprise security and risk managers to implement solutions that deliver a delightful user experience.
Digital transformation and multi-factor authentication adoption trends continue
Ongoing migrations to the cloud, digital transformation projects, and extended WFH policies accelerated the pace of MFA adoption and spending in 2021, and that trend is likely to continue through the decade. There’s a learning curve on any new technology, but enterprises can do practical things to quicken the pace of adoption.
Educating employees, focusing on a seamless user experience, and setting aside significant budgetary resources for adoption are all ways to push MFA forward and reduce ongoing threats. The post-pandemic era won’t be any safer than before the pandemic — in fact, the threats will have grown. The move to remote work is opening up new vulnerabilities, and the enterprise can’t be caught flat-footed when inevitable breaches and attacks happen.
Read the full report here to learn how companies in your sector have implemented MFA to address pandemic-driven security concerns — from the form factors being deployed to the user groups adopting them.
For a deeper dive into the findings from this report, sign up for the upcoming Yubico webinar, Remote Work During COVID-19 Drives MFA Adoption, on May 18 at 10 a.m. PST.
About the study
Yubico worked with 451 Research, part of S&P Global Market Intelligence, to find out how the pandemic-driven, remote-worker environment has changed authentication technology adoption. We surveyed 200 senior IT management and security staff in verticals such as technology, financial services, education, professional services, retail and government. The study focuses on how managers perceive authentication technologies, how they spent money on that technology, and how authentication adoption may have changed during the pandemic.