The YubiKey
The industry’s #1 security key, enabling strong two-factor, multi-factor and passwordless authentication.
Easy-to-use, strong authentication
All-in-one configurable security key
With a simple touch, the multi-protocol YubiKey protects access to computers, networks, and online services.
Easier and safer than authenticator apps
No more reaching for your smartphone, or re-typing passcodes. Just plug in your YubiKey, tap, and it does the rest for you.
Works with hundreds of services
The YubiKey works with Windows and Mac login, Gmail, Dropbox, Facebook, Salesforce, Duo, and many more services.
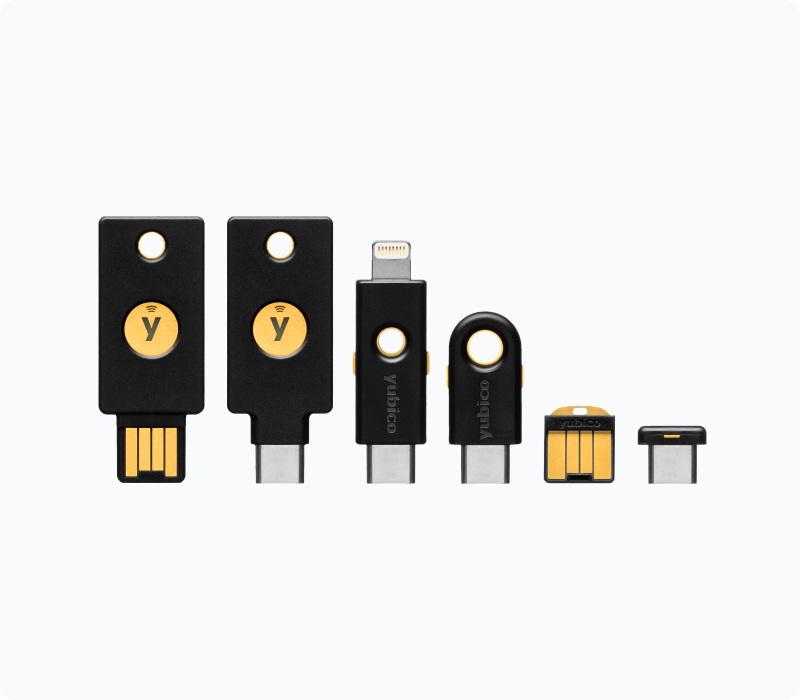
YubiKey 5 Series – The world’s #1 multi-protocol security key
The YubiKey 5 Series eliminates account takeovers by providing strong phishing defense using multi-protocol capabilities that can secure legacy and modern systems. The series provides a range of authentication choices including strong two-factor, multi-factor and passwordless authentication, and seamless touch-to-sign.
- Stops account takeovers
- Multi-protocol support; FIDO2/WebAuthn, U2F, Smart card, OpenPGP, OTP
- USB-A, USB-C, Lightning, NFC
- Now available YubiKey 5C NFC with USB-C and NFC all-in-one to secure online accounts on mobile and desktops
Learn more about the YubiKey 5 Series >

YubiKey 5 FIPS Series
The YubiKey 5 FIPS certified security keys meet the highest level of assurance (AAL3) of the new NIST SP800-63B guidelines.
- Suitable for government and regulated industries
- Multi-protocol support; smart card, OTP, OpenPGP, FIDO U2F, FIDO2/WebAuthn
- USB-A, USB-C, Lightning, NFC
Learn more about the YubiKey 5 FIPS Series >
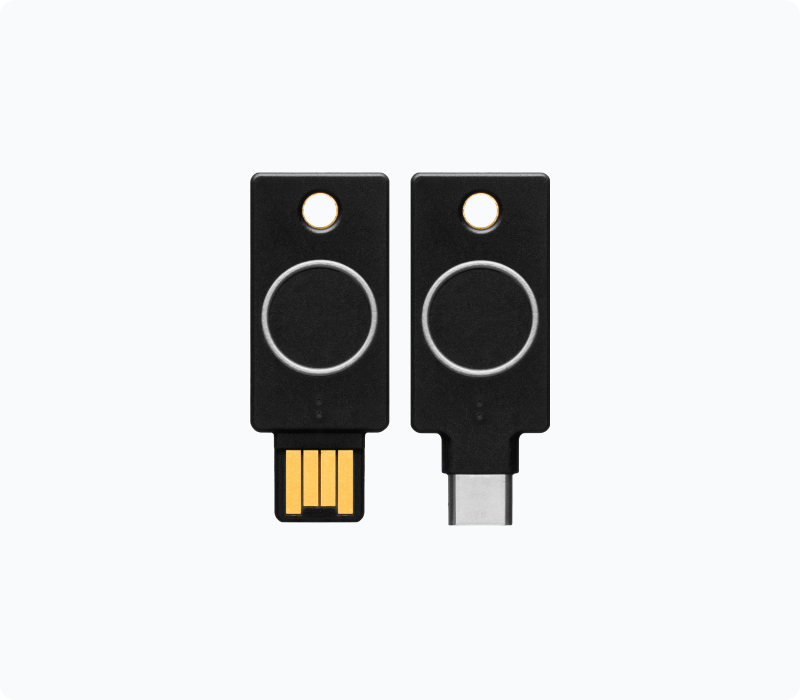
YubiKey Bio Series
YubiKey Bio Series supports biometric authentication using fingerprint recognition for secure and seamless passwordless logins. Built primarily for desktop and designed to offer strong biometric authentication options, the YubiKey Bio Series offers the hallmark hardware security of Yubico, combined with a new user experience.
- Meets the most stringent hardware security requirements with fingerprint templates stored in the secure element on the key
- Works out-of-the-box with operating systems and browsers including Windows, macOS, Chrome OS, Linux, Chrome, and Edge
- Supports FIDO2/WebAuthn, FIDO U2F
- Available in both USB-A and USB-C form factors with biometric support
Learn more about the YubiKey Bio Series >

Security Key Series
The Security Key Series by Yubico delivers FIDO-only security keys for both consumers and enterprises. These keys combine hardware-based authentication, public key cryptography, and modern authentication protocols to eliminate account takeovers.
- Secures Google Workspace, Microsoft 365, top IAM platforms, password managers, social media applications and hundreds of other services
- Supports FIDO2/WebAuthn and FIDO U2F
- Works across desktop and mobile with tap-and-go authentication for mobile phones
- Highly durable with water- and crush-resistance
- USB-A/NFC and USB-C/NFC dual connector keys
- Enterprise edition keys offer serial numbering; available with YubiKey as a Service only
Learn more about the Security Key Series >

YubiHSM 2 and YubiHSM 2 FIPS
Game changing cryptographic protection for servers, applications and computing devices.
- Enhanced protection for cryptographic keys
- Rapid integration with hardware-backed security
- Simplified deployment for organizations of all sizes
- Available in FIPS and non-FIPS versions with same feature set
Learn more about the YubiHSM 2 and YubiHSM 2 FIPS >
Services
Enterprises can easily procure and distribute YubiKey authentication solutions for employees at scale and get expert support and consulting services to help ensure success.

YubiKey as a Service
YubiKey as a Service offers flexible purchasing options to easily buy and upgrade to the latest YubiKeys as your business evolves.

YubiEnterprise Delivery
YubiEnterprise Delivery provides teams with capabilities to manage the delivery of hardware security keys to users globally and accelerates the adoption of strong authentication.
Software
Download free software and tools for rapid integration and configuration of the YubiKey two-factor authentication with applications and services.

Yubico Authenticator
The Yubico Authenticator app allows you to store your credentials on a YubiKey and not on your mobile phone, so that your secrets cannot be compromised.
Computer login tools
A range of computer login choices for organizations and individuals. Secure Windows or Macs with strong authentication.
Get Started

Find the right YubiKey
Take the quick Product Finder Quiz to find the right key for you or your business.

