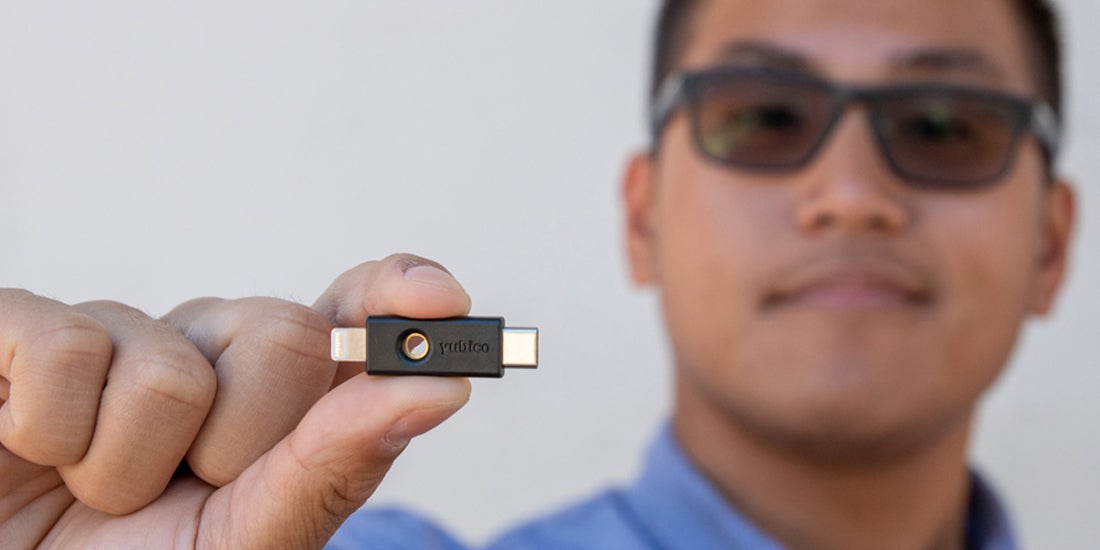
When we launched the YubiKey 5Ci on August 20, we also introduced a new firmware to the YubiKey 5 Series: version 5.2.3. Currently, this firmware is only being shipped in the YubiKey 5Ci, however, we expect to roll out this version to all YubiKey 5 Series devices over the next month. While it is a minor update, 5.2.3 firmware has a number of features and improvements as it relates to the FIDO and OpenPGP protocol stacks.
FIDO
For FIDO2, the new firmware adds an enhanced privacy mode. This enables sites to require a PIN when a YubiKey is registered with their service. The FIDO PIN of the YubiKey must be used in order to reveal what sites the authenticator was registered to. This feature is intended for services that want to protect the privacy of what sites their users have visited for a variety of reasons. For example, assume a user registers the YubiKey with “some-website.com” and at a later point, they travel to a country where the content on “some-website.com” is discriminated against. From this person’s YubiKey, it would not be possible to tell that the key was registered to “some-website.com” without using the PIN.
The FIDO protocol has also seen a number of technical improvements, which are supported in YubiKey firmware 5.2.3:
- Removal of RSA, as we didn’t see any use of it in practice
- Addition of Ed25519 signature support, a modern ECC curve
- Addition of credential management to allow the deletion of FIDO resident keys
- Addition of PIN and no PIN support to the FIDO HMAC-secret extension for offline operations
- Implementation of signature counters with even more privacy features including keeping per-credential offsets and randomly increasing counter values
OpenPGP
YubiKey Firmware 5.2.3 also has a number of enhancements to the OpenPGP implementation on the YubiKey. Most of them are related to a number of the features from the OpenPGP Smart Card Specification version 3.0 and above.
ECC Support
OpenPGP 3.0 introduced support for Elliptic Curve Cryptography in addition to RSA. ECC today is by many considered a better choice for many applications and has a number of advantages including faster cryptographic operations and smaller key sizes.
YubiKey Firmware version 5.2.3 and above specifically supports signatures (ECDSA) and key exchange (ECDH) from the OpenPGP 3.4 spec for the following curves.
From ANSI X9.62/FIPS-186-3:
- ansix9p256r1
- ansix9p384r1
- ansix9p521r1
From RFC5639:
- brainpoolP256r1
- brainpoolP384r1
- brainpoolP512r1
In addition to the PGP 3.X spec, the YubiKey now also supports:
- Secp256k1, the curve used in BitCoin
- Curve25519, the default curve used in ssh (EdDSA and Diffie-Hellman)
Attestation
Firmware 5.2.3 also adds attestation for keys generated on device ( this capability has already been available in our PIV application stack since we launched the YubiKey 5 Series). Specifically, a YubiKey can attest that an asymmetric key was generated on, and never left, the YubiKey. For example, a company could require that all developers sign their commits with a company-provided YubiKey that had the private key generated on device. Using the attestation keys, the system will reject any keys that were generated outside of the YubiKey and imported. Attestation was added as a Yubico-specific extension in version 3.4 of the OpenPGP Smart Card Specification. Documentation for how this feature can be used is found here on the Yubico developer site.
Multiple Operations per Touch
YubiKeys can now be configured to allow multiple operations over a short period of time with a single touch to the key, a capability that was previously available in the PIV application of the YubiKey 5 Series. This can be helpful for batch signing/encryption or operations that are composed out of multiple cryptographic primitives. The behavior can be enabled or disabled by the user.
Yubico is always working to advance the functionality and security of our YubiKeys, and we thank our users for their product feedback and support to drive technical improvements like the ones listed above.
To determine which firmware your YubiKey 5 Series device has, please use the YubiKey Manager.