Since I started my journey as a hardware authentication innovator, I have heard people say that the future of authentication is software. Or TPMs. Or biometrics. Or invisible data intelligence that will silently protect us all. Today, it is fair to say that all these predictions were right – when they are combined into a comprehensive strategy.
But in order for secure online identities to scale to all services and users, open standards “plumbing“ is necessary. And it includes open authentication and identity standards that are natively supported in leading platforms and browsers, enabling strong crypto between a range of authenticators and the services they protect.
In 2013, when Wired published the first article on U2F, Yubico received many valid questions on this new authentication protocol. We shared our response in a Future of Authentication FAQ blog. The content is still valid, so if you did not read it then, we welcome you to do so now.
A couple of months ago, Yubico was invited to a panel discussion at the European Identity & Cloud Conference with the topic, “The Future of Authentication – Killing the Password.” Identity experts from Microsoft, Salesforce.com and NRI all agreed that the “plumbing” must be open standards, and that there is no silver bullet for the multi-factor options we add as an extra layer of user verification. The YubiKey did, however, get high marks – Salesforce mentioned that it took only two days to deploy YubiKeys for 17,000 employees, and Microsoft disclosed that Windows Hello will eventually accept external hardware authenticators. Until biometrics have proven to be more robust, passwords are actually not that bad. Or to quote the warning message that the latest Nexus phone presents when setting up a biometric login: “Using your fingerprint to unlock your device may be less secure than a strong password, PIN, or pattern.” (Watch the EIC panel presentation.)
Those same identity experts agreed on one more important trend: authentication and identity will be separated. FIDO U2F is one of the open standards protocols that makes that separation possible. It lets you have assorted identities, including a real identity tied to your driver’s license, a temporary identity for your work, and an identity that allows you to be “secure, yet anonymous”. This can be life critical for dissidents and journalists, and will help safeguard internet privacy for the rest of us.
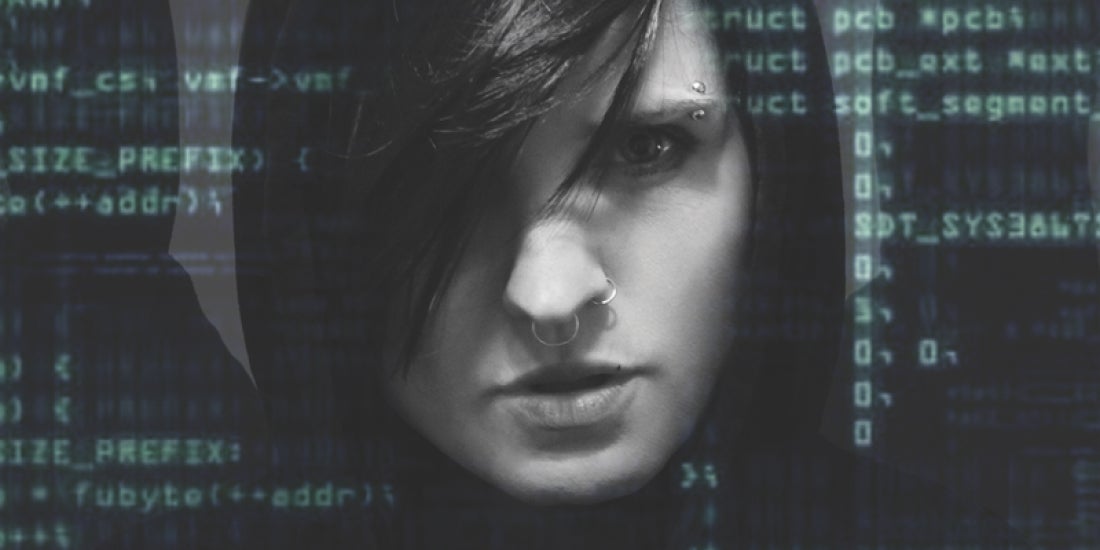
P.S. The picture above is an example of the latter. I once showed up at the office disguised as the famous fictional hacker Lisbeth Salander, and no one recognized me.