Tag: government
-

Straxis and Yubico launch secure mobile web app to access essential U.S. military email, pay and travel services SANTA CLARA, CA, STOCKHOLM, SWEDEN and TULSA, OK – July 15th 2024 – Yubico, the leading provider of hardware authentication security keys and Straxis, a mobile application provider, today announced the availability of a new Secure Web browsing application called MilSecure Mobile. This application can be adopted by any Defense Department (DOD) organization to enable […] Read more -

Enhancing Federal Security: Issuing PIV-Compatible Credentials with Axiad Cloud (FedRAMP) and Yubico Join this webinar to gain a comprehensive understanding of how you can streamline the credentialing process and ensure compliance with federal standards while enhancing security and efficiency. Read more -

New NIST guidance on passkeys: Key takeaways for enterprises NIST recently released an update to SP800-63B to provide guidance on syncable authenticators. As FIDO passkeys continue becoming more adopted and available at a large scale, NIST guidance helps organizations properly position and plan so they can successfully implement synced passkeys both internally and externally. Within the guidance, it’s important to understand the nuance of […] Read more -
Modern authentication for the Department of the Air Force Download the free brochure to learn how the YubiKey solves U.S. Air and Space Force modernization uses cases. Read more -

Securing Department of Corrections with modern, phishing-resistant MFA Learn how the YubiKey stops modern cyber threats such as phishing attacks and account takeovers across the Department of Corrections, with CJIS compliant phishing-resistant multi-factor and passwordless authentication. Read more -

Australian government leads efforts toward phishing-resistance Over the last few weeks, the Australian government has made big strides in further bolstering its digital security posture by enacting major cybersecurity measures. Australia has a goal to be a global leader in cybersecurity by 2030, and these recent measures are making impactful steps toward reaching this mission. First, the government announced that myGov […] Read more -
Modernizing authentication across the Department of Defense with phishing-resistant MFA Learn how the DOD-approved and FIPS 140-2 validated YubiKey is helping the federal government with phishing-resistant multi-factor authentication (MFA) for modern use cases not supported by the PIV and CAC Read more -

FIDO Alliance releases U.S. government adoption guidance on FIDO authentication Many federal agencies have been using FIDO authenticators to enable secure access to systems for a variety of use cases. However, they have been deployed in varied configurations and there was a lack of guidance on how to implement the credentials. With the release of a new whitepaper, FIDO Alliance Guidance for U.S. Government Agency […] Read more -

What CISA and NSA’s ESF guidance means for critical infrastructure cybersecurity The Cybersecurity Infrastructure Security Agency (CISA) and the National Security Agency (NSA) recently collaborated to produce an important new document, “Identity and Access Management: Recommended Best Practices for Administrators.” Part of the Enduring Security Framework (ESF), it presents a distillation of identity access management (IAM) and cybersecurity guidance put forth by CISA to date, based […] Read more -
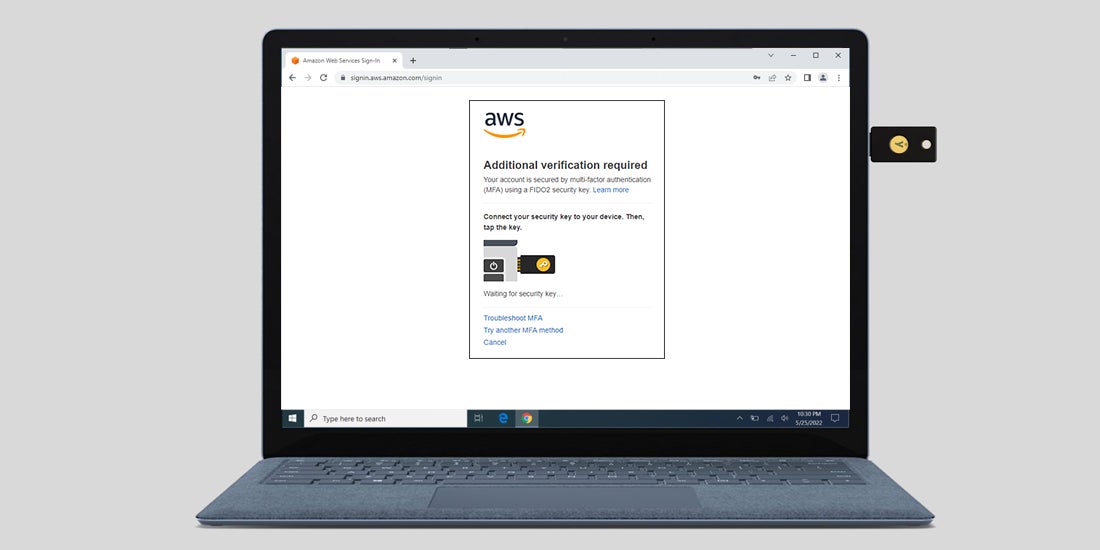
Amazon Web Services announces support for FIDO2 security keys Amazon recently announced improved support for using FIDO2 security keys as an MFA device to log on to the Amazon Web Services (AWS) console. As a result, FIDO2 security keys like the YubiKey are now supported on AWS GovCloud (US region) – providing phishing-resistant MFA for all users. Additionally, AWS has improved their support for […] Read more