Tag: developers
-

YubiKey 4(096): You Asked, We Delivered In a previous blog post I talked about RSA key length and argued why a 2048-bit key is still a viable choice today. However, here at Yubico we do not like to remain idle, twiddling our thumbs. We are constantly improving our products. As a result of these efforts, earlier this month, we launched the […] Read more -
With a Touch, Yubico, Docker Revolutionize Code Signing Today we released the YubiKey 4. Our next generation product that includes a new function called touch-to-sign, a unique and simple method for code signing that we have brought to life together with Docker, an open platform for distributed applications. At DockerCon Europe 2015 in Barcelona, Docker and Yubico together unveiled the world’s first touch-to-sign code […] Read more -

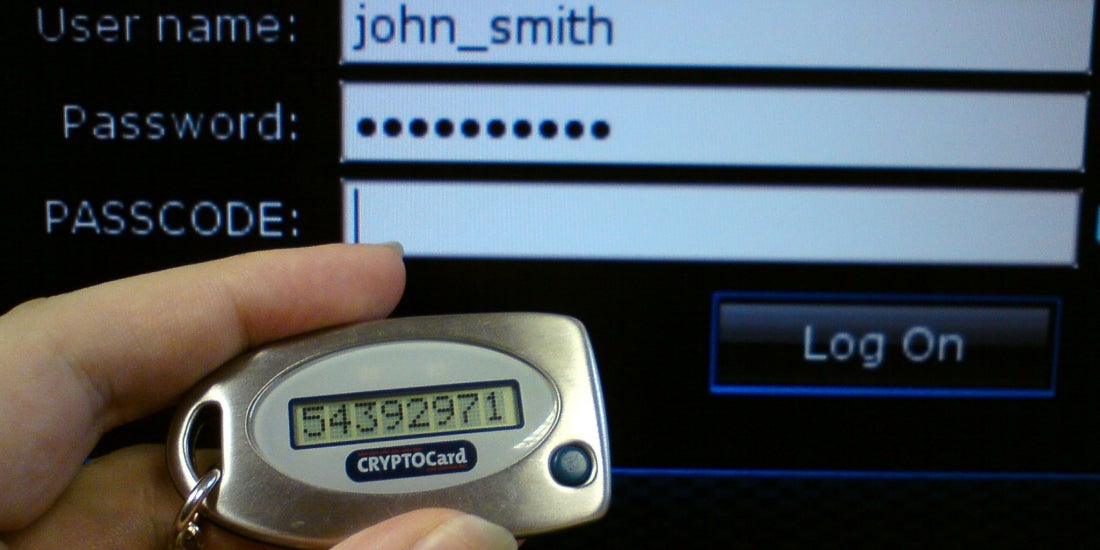
YubiKey Static Password Offers Up Options One of the original functions on the YubiKey is a static password for use in the password field of any application. Such an option seems to challenge common misgivings about reusing passwords. And we would agree. But if you look a little deeper, the static password, which has attracted more users than we thought it might, […] Read more -
A Crash Course in Cryptography To better understand asymmetric cryptography, you need knowledge of some basic concepts. For those that are not familiar with public-key cryptography, I will provide here a brief, stripped-down introduction to the topic. In asymmetric or public-key encryption there are two main players: the encryption algorithm itself (RSA, ECC, ElGamal, …) and a cryptographic key pair (there […] Read more -

Expanding YubiKey Keyboard Support Hi. We’ve had a few queries about using the YubiKey with various keyboard layouts, so we thought we’ll spend some time describing the different methods available to do that. Like a USB keyboard, YubiKeys work via inputting scan codes as opposed to actual characters. This means that when you type, the keyboard only sends the […] Read more -

BrowserID and YubiKey To to learn how you use the YubiKey with BrowserID, a new open identity initiative, please check out this video from a BrowserID developer: https://vimeo.com/64514090 BrowserID was introduced in mid 2011 by the Mozilla Project. It addresses the same problem as OpenID and SAML, as well as the common OAuth or OpenID-based login-with-an external-account (such […] Read more -

YubiKey NEO Composite Device The YubiKey NEO differs from the standard YubiKey as it can become a composite USB device – presenting both a HID (Keyboard) and CCID (SmartCard) device to the host. This allows us to support all the great features of the standard YubiKey and add new support for SmartCard functions. Our last NEO post described the […] Read more