What is a Cyber Attack?
A cyber attack is an online attack targeting an enterprise or individual for the purpose of disrupting, disabling, destroying, or maliciously controlling their computing infrastructure; destroying the integrity of their data; or stealing controlled information.
Cyber Attack Definition
A cyber attack is a malicious assault cybercriminals launch against a single or multiple computers or networks using one or more computers. A cyber attack can steal data, disable computers, or launch other attacks from a breached computer. Cybercriminals use a range of techniques to deploy cyber attacks, including denial of service, phishing, malware, ransomware, and other methods. Cybersecurity firms exist to attempt to prevent cyber attacks and protect clients from their effects.
In most cases, cyber attackers are criminals looking to exploit the attack for financial gain. In other cases, the aim is to disrupt operations by disabling access to IT systems, or in some cases directly damaging physical equipment. The latter type of cyber attack is commonly politically-motivated and may be state-backed and carried out by state actors, or cybercriminals in their employ.
How Do Cyber Attacks Work?
Cybercriminals launch a range of attacks against entities and individual victims that can include extorting payment; accessing, changing or deleting sensitive data; or interfering with business processes.
A cyber attack can be active or passive. An active cyber attack attempts to affect or alter system resources or their operation. A passive cyber attack aims to access or use system information without affecting system resources.
Physical cyber attacks damage or cause the loss or theft of computers and equipment. Other cyber attacks take the form of attempts to achieve results unforeseen by the original designer but useful for the attacker by forcing changes in the logic the computers or network protocols use. These logical cyber attacks are typically carried out using malware.
A cyber attack can be perpetrated by an outsider or an insider relative to the organization. An authorized user from inside the security perimeter initiates an inside attack by accessing system resources in unapproved ways.
Anyone from hostile governments and international terrorists to organized criminals at all levels and even amateur pranksters may launch an outside cyber attack. As an outsider or an unauthorized or illegitimate user of the system, this attacker merely initiates the attack from outside the perimeter.
Logical and physical resources, called assets, can have vulnerabilities that attackers target. Active cyber attacks compromise system resource availability or integrity by altering system resources or affecting how they operate. Passive cyber attacks compromise confidentiality as information from the system but no system resources are accessed and abused.
Cyber attacks on availability aim to prevent users from accessing their own data unless they pay a ransom or fee. Organizations sometimes pay and repair the vulnerability later to avoid stopping business.
Cyber attacks on integrity consist of enterprise or personal sabotage, or leaks. The goal is to influence public opinion so this cybercriminal accesses and releases sensitive data merely to expose it, or steals credentials in order to spread misinformation while making it appear legitimate.
Cyber attacks on confidentiality are often designed to steal your personal identifying information (PII) such as credit card details or bank account information which can be sold for use.
Here is an example of each type of cyber attack:
- Malware is a cyber attack on availability. Relevant types of malware include ransomware, worms, and true viruses. Ransomware locks and encrypts stolen victim data, demanding payment to make it available again.
- Advanced persistent threats (APTs) are a type of cyber attack on integrity. In this cyber attack, an unauthorized user infiltrates a network undetected expressly to steal data and remain in the network for a long time without harming it. APTs often occur in high-value information sectors, such as tech, national defense, and finance.
- Social engineering is an attack on a person with the goal of compromising the confidentiality of their information. Phishing attacks are the most common form of social engineering. Social engineering attacks psychologically manipulate victims into giving away information or performing actions, often via a deceptive email or text.
What is a Cyber Attack Map?
A cyber attack map, also called a cyber threat map, is a real-time map of global cyber attacks. Typically attack paths on a live cyber attack map resemble differently colored beams of light, showing where attacks originate and land.
Cyberthreat by Kaspersky Lab identifies vulnerabilities, trends in botnet activities, the prevalence of spam and infected mail, and most widespread threats including cyber terrorism attacks by country and worldwide. Fortiguard by Fortinet is also a useful real time cyber attack map tool.
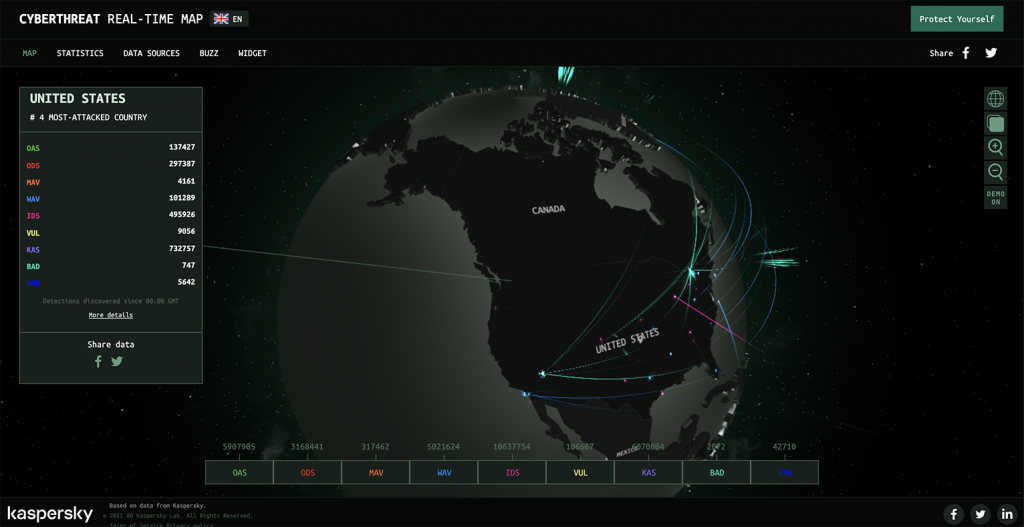
Screenshot of Cyberthreat Real-Time Map, https://cybermap.kaspersky.com/. Accessed 02 August. 2021
Types of Cyber Attacks
As discussed above, there are several important categories of cyber security attacks. Some types of attacks can be classified in more than one way, depending on the facts. First, it’s helpful to classify cyber attacks as active or passive.
Passive Cyber Threats
- Computer surveillance. This is any monitoring of data and computer activity.
- Network surveillance. This is the monitoring of data and activity being transferred over computer networks.
- Keystroke logging or keylogging. This is the act of monitoring victim actions by recording the keys they type on a keyboard.
- Wiretapping. Monitoring online and telephone conversations by a third party, usually secretly.
- Fiber tapping. Extracts signal from an optical fiber with a network tap method without breaking the connection.
- Idle scanning. Idle scanning is a method for TCP port scanning that includes finding out what services are available by sending spoofed packets to a computer.
- Backdoor. A covert means of bypassing normal encryption or authentication in a product, embedded device, computer, or its embodiment.
- Eavesdropping. Secretly listening to the private communications of others without their consent.
- Typosquatting. A form of cybersquatting in which a “squatter” sits on domain names similar to those owned by a copyright or brand, targeting internet users who type in a website address incorrectly rather than using a search engine.
- Vulnerabilities. Hackers can exploit these weaknesses to perform unauthorized actions or gain unauthorized access to computer systems.
Active Cyber Attacks
- Brute force attacks. In these cyber security attacks, hackers gain unauthorized access to sensitive data or a system by guessing usernames and passwords.
- Malicious code/Malware. Any software, file, or program that is harmful to a computer user such as worms, Trojan horses, computer viruses, spyware, adware, and ransomware, are all malware.
- Denial of service attacks (DoS). DoS attacks, including distributed denial of service attacks (DDoS attacks) occur when the actions of a malicious cyber threat actor prevent legitimate users from accessing devices, information systems, or other network resources.
- Data scraping. Computer programs use this technique to extract data from human-readable output as it comes from other programs.
- Port scanning. Identifies open and available services and ports on a network host.
- Email spoofing. Hackers can create spoof emails with forged sender addresses to mislead the recipients about who is sending them. Spam emails and phishing attacks can spoof the email header because core email protocols lack authentication.
- Exploit. An exploit is a piece of data, software, or sequence of commands that “exploits” a vulnerability to gain unauthorized access to sensitive data or cause unintended behavior.
- Phishing. This widespread practice is the use of legitimate-looking yet bogus websites to collect sensitive information such as credit card numbers, login credentials, bank account details, and other financial information.
- Whaling attack. A targeted phishing attack aimed at a high-level, C-suite executive, designed to steal sensitive information from the organization.
- Man-in-the-middle (MitM). In these attacks, an eavesdropping attacker relays and could even alter the communication between two parties who think they are directly and privately communicating.
- Man-in-the-browser. This technique allows an attacker to exploit vulnerabilities in a web browser to infect it by modifying transaction content and web pages, or secretly inserting new content.
- Smurf attack. A DDoS attack which broadcasts large numbers of Internet Control Message Protocol (ICMP) packets using an IP broadcast address with the intended victim’s spoofed source IP.
- Ping flooding. A simple DDoS attack that uses ICMP “echo request” or ping packets to overwhelm the victim. This is not the same as a Ping of death attack, which involves sending a malicious ping to a computer.
- Direct access attacks. These cyber attacks enable the hacker to gain direct access to a computer and directly download its data.
- Social engineering. Social engineering describes any vector for cyber attack that exploits human susceptibility to manipulation and psychology. Social engineering attackers trick victims into divulging sensitive data and confidential information or performing an action contra to typical security standards.
- Tampering. This cyber attack is the modification of a service or product intended to harm the end user.
- Privilege escalation. Privilege escalation refers to gaining unauthorized access to resources that are typically restricted from the user or application exploiting a programming error, design flaw, access control, vulnerability, or configuration oversight in an application or operating system.
- Viruses. These computer programs replicate by inserting their own code to modify other programs once executed.
- Worms. This kind of self-replicating malware stays active on the infected system even as it infects other computers.
- Trojan horses. These are malware programs that conceal their true intent from users.
Vulnerabilities that often lead to Remote Command Execution
- Buffer overflow attacks. These cyber attackers overwrite the memory of an application to exploit buffer overflow issues. This triggers a response that exposes private information or damages files by changing the program’s execution path.
- Heap overflow. When a portion of memory has data written to it and is allocated to the heap without doing any bound checking on the data, it can trigger this form of buffer overflow.
- Stack overflow. The program in this situation writes more data to the stack’s buffer than it has allocated for it, causing the program to write more data to the buffer on the stack, corrupting data around it, and causing improper function and, eventually, a crash.
- SQL injection. SQL injection is a technique for injecting malicious SQL code statements, used to attack data-driven applications, into an entry field to be executed.
- Format string attacks. These cyber attacks occur when applications evaluate submitted data from input strings as commands. This allows the attacker to read the stack, execute code, or cause a segmentation fault in the running application.
- Cross-site scripting (XSS). XSS security vulnerabilities are generally found in web applications. XSS vulnerabilities may be used to bypass access control, such as the same-origin policy, because they enable user-attackers to inject scripts into web pages other users see on the client-side.
- Format string attacks. These cyber attacks occur when applications evaluate submitted data from input strings as commands. This allows the attacker to read the stack, execute code, or cause a segmentation fault in the running application.
- Cross-site scripting (XSS). XSS security vulnerabilities are generally found in web applications. XSS vulnerabilities may be used to bypass access control, such as the same-origin policy, because they enable user-attackers to inject scripts into web pages other users see on the client-side.
Beyond this, cyber security attacks can be classified based on approach, goal, tactics, and other factors:
Cyber Fraud / Social Engineering Attacks
Cyber fraud/social engineering attacks include phishing attacks and all their variants, such as spear phishing, whaling, smishing, vishing, catphishing, and catfishing. Among the more common and insidious types of attacks in cyber security, classic phishing attacks disguise links to bogus websites in emails or texts designed to seem like authentic messages from trusted organizations, brands, or individuals so that the victims respond to the dangerous request for information. Phishing links typically take victims to spoof websites and harvest their details. Spear phishing/whaling is a highly complex, targeted variant of phishing that tends to see attackers impersonate high-level users and trick victims into sending more sensitive data by building added authenticity.

Malware Attacks and Infections
Malware, malicious software developed to infect IT systems with the goal of compromising data and/or causing damage, comes in many forms. Some examples of malware attacks are ransomware, adware, spyware, viruses, worms, trojans or trojan horses, botnets, rootkits, exploits, time bombs and logic bombs, crypto-jacking, drive-by-downloads, and more.
Technical Attacks
Technical attacks generally target cyber-infrastructure such as DNS, databases, and outdated software. Some examples are advanced persistent threats (APTs), breach attacks, card skimming, DNS attacks, flooding which is typically used in DoS and DDoS attacks, malvertising, man-in-the-middle (MITM) attacks, pharming, various passive cyber attacks, spoofing attacks, SQL injections, URL injection, website defacement, and internet sabotage.
Vulnerability Exploitation
Even the best systems and software demand patches and can remain vulnerable to cyber attacks. Some examples of cyber attacks that exploit vulnerabilities include brute force attacks when passwords are vulnerable, also called password cracking; buffer overflow attacks; zero-day exploits; code injection and cross-site scripting (XSS); browser hijacking; supply chain attacks; and privilege escalation.
Most Common Cyber Attacks
Although any type of cyber attack is potentially a risk, there are certain different types of cyber attacks that are more commonly seen and general cyber attack trends.
Ransomware
Ransomware will remain a serious cybersecurity threat, with cybercriminals taking more targeted approaches to fool and infect victims.
Software supply chain attacks
An attacker typically takes on a legitimate software supply chain by modifying and infecting the software’s building blocks to install malicious code. The first type of software supply chain attack includes targeted assaults against well-defined target utilities, looking for weak spots. The second type of software supply chain attack locates a weak link with a large distribution radius to compromise as many victims as possible.
Business email compromise (BEC)
In BEC scams, hackers impersonate outside vendors or trusted executives and send fraudulent emails motivating employees with access to company funds to wire money to supposedly legitimate bank accounts for “company business.”
Internal attacks
Internal attacks from employees continue to be a serious cybersecurity threat, and insiders may compromise their accounts and harm an organization either deliberately or accidentally.
Sophisticated phishing cyber attacks
Phishing remains among the biggest threats to cyber security. According to Cybint, more than 60 percent of businesses experienced phishing in 2018, and the number was rising. Verizon reports that 32 to 33 percent of all cyber attacks are phishing attacks, and current phishing attacks are becoming more difficult to detect all the time.
Password-based attacks
Password-based cyber attacks pose a threat to both businesses and individuals because users tend to adopt similar or identical passwords across multiple services and sites. A single security breach can compromise many accounts on other sites.
AI-based attacks
Attackers can now use malware that gathers data on why their cyber attacks fail; this allows them to harness the power of AI to make their attacks more successful.
Public cloud environments
More cyber attacks target sensitive data and resources residing within these environments, but poor management and misconfiguration of cloud resources leave these platforms vulnerable to a wide array of attacks.
Mobile device attacks
The same methods and techniques malicious actors deploy on the general threat landscape also apply in the mobile world.
IoT attacks
As more devices both at work and at home go online, IoT attacks have increased. IoT devices are vulnerable to unauthorized access and infection because they typically use default credentials.
Cyber Attack Examples
Cyber security attacks can target specific individuals or organizations, or they may be less directed and more broadcast, affecting multiple organizations across regions or around the world. Targeted cyber attacks often spiral into more general problems that impact users far beyond their original intended victims. Here are several recent cyber attacks with high profile:
WannaCry
WannaCry was a ransomware attack in May of 2017 that spread rapidly thanks to a vulnerability in Microsoft Windows. Using a stolen code called EternalBlue that had been secretly developed by the United States National Security Agency, the ransomware exploited a relatively fresh vulnerability in Windows that was still unpatched in many systems. Worse—the NSA found the hole and created the weapon for cyber warfare, rather than telling Microsoft. WannaCry infected computers, encrypted their hard drives and whatever was on them, and demanded payment in Bitcoin to release the contents.
NotPetya
Petya was a 2016 ransomware that infected and encrypted the master boot record of machines via phishing spam, making accessing files tremendously difficult. In June 2017, a more virulent yet different enough version called NotPetya started to spread via the EternalBlue exploit. Although Russia denies it, NotPetya is generally thought to be a cyber terrorism attack by Russia against Ukraine. However, this cyber attack had worldwide consequences costing billions of dollars.
Capital One breach
Capital One realized it had experienced a data breach from hacking in July 2019, resulting in the loss of data from hundreds of thousands of credit card applications. This meant the exposure of personally identifying information such as Social Security numbers and birthdates, and was massive in scale. This cyber attack was perpetrated by Paige Thompson, aka Erratic, an American who had worked for Amazon in the past.
Thompson never attempted to profit from her work, made little attempt to conceal her hacking, and was apprehended because she publicly posted a list of breached directories without data—making one of the biggest cyber attacks in history rather mysterious. Whatever the motives, the victims were exposed.
Cyber Attack vs Virus
A cyber attack and a virus are not exactly the same. Although all computer viruses are a type of cyber attack, not all cyber attacks are viruses. Computer viruses are pieces of malicious code that spread across computers and networks like a contagious disease might. They are a type of active cyber attack.
Cyber Attack vs Spyware
Spyware is also a type of cyber attack. Spyware is software that takes a specific aim at a users’ hard drive in order to transmit its data without the user knowing. Spyware provides a 3rd party user access to information about another user’s computer activities
Does Yubico Offer Cyber Attack Protection?
Yubico helps organizations of all sizes and individuals minimize their risk of cyber attack with the YubiKey. YubiKeys offer strong MFA access to business applications across employee and personal devices. YubiKeys deliver the best user experience and the highest assurance security, protecting staff against account takeovers and phishing attacks.
Yubico helps organizations reduce their risk of cyber attacks, successfully addressing compliance requirements and protecting sensitive customer and financial data with the YubiKey’s strong hardware-backed security. With YubiKey, organizations effectively verify all customer and employee identities before providing access to critical information—yet user experience is never sacrificed.
The YubiKey’s physical security element requires explicit user consent, but it’s easy to use—the consent comes with a tap or touch of the YubiKey itself. This active role for the user improves the secure login process, and protects the user from even very persuasive, complex cyber attacks as it binds the user login to the original website’s URL and cannot be fooled into revealing user credentials.
No matter how many times hackers steal username and password or other sensitive data through data breaches, they cannot impersonate you and login without the YubiKey in their physical possession. YubiKey can help prevent cyber attacks on healthcare industry organizations, spoofing cyber attacks, election cyber attacks, cyber attacks on government agencies, and cyber attacks through ransomware.
Obviously, cyber attack prevention is critical. It’s important to know how to prepare for a cyber attack, but there’s no substitute for preventing attacks in the first place.
Learn more about how to prevent cyber attacks with the YubiKey’s hardware-based authentication, designed to foil even the most determined cybercriminals, here.
Get Started

Find the right YubiKey
Take the quick Product Finder Quiz to find the right key for you or your business.
