The YubiHSM 2 is available as a FIPS 140-2 validated, Level 3 solution, or as a non-FIPS solution, both with the same capabilities. Both solutions ensure uncompromised cryptographic hardware security for applications, servers and computing devices at a fraction of the cost and size of traditional HSMs.
Cryptographic Keys Stored in Software are Vulnerable to Threats
The 2024 average cost of a data breach is $4.88M. Software storage of cryptographic keys for servers is increasingly vulnerable as attacks become more sophisticated. For example, if a private key is compromised from a Certificate Authority(CA), an attacker can pretend to be your website.
The YubiHSM 2 and YubiHSM 2 FIPS Change the Game for Effective Key Security
Ensure secure hardware cryptographic key storage and operations for applications, servers and computing devices while eliminating the cost and complexity of traditional Hardware Security Modules (HSM)s. Yubico’s HSM solutions are tamper resistant and offer low cost, high security ROI in a portable ‘nano’ form-factor that allow flexible use across diverse devices and locations. With the YubiHSM 2 and YubiHSM 2 FIPS, organizations can prevent cryptographic keys from being copied by attackers, malware and malicious insiders. Enterprises can rapidly integrate with either HSM option using the open source SDK 2.0.
Secure Hardware Protection for Cryptographic Keys
Cryptographic keys stored in software can be copied, and are vulnerable to accidental distribution and remote theft. Without strict procedures, it is easy for admins or malicious insiders to backup keys to USB flash drives, FTP them, or share to others via a cloud storage service. Additionally, sophisticated attackers can gain admin access or deploy trojan malware that installs on servers, searches for cryptographic keys, and then copies them for sale on dark web sites like Alphabay.
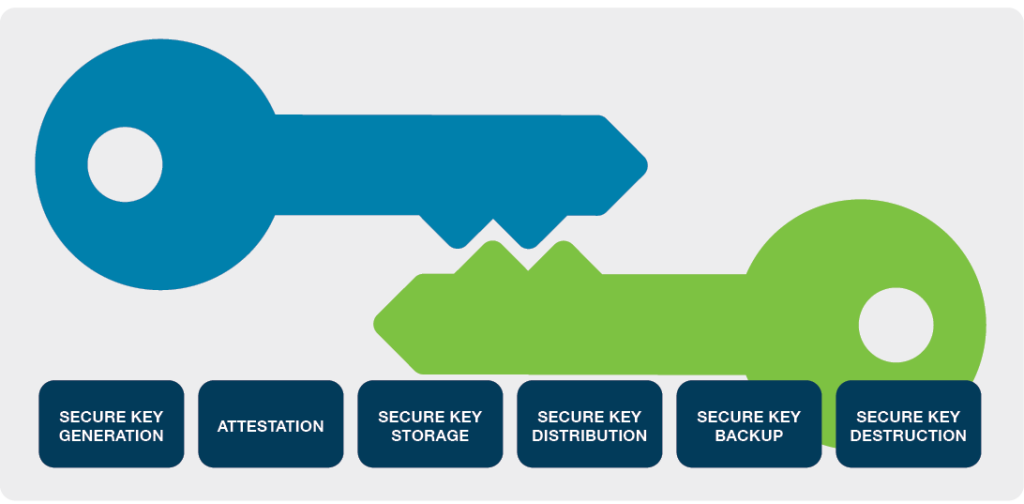
The hardware-based HSM solutions enable secure key storage and operations by preventing accidental copying and distribution of keys, and by preventing remote theft of keys stored.
- Secure key storage and operations on tamper-resistant hardware, with audit logging
- Extensive cryptographic capabilities including hashing, key wrapping, asymmetric signing, decryption, attestation and more.
Innovative Design for Flexible Use
Traditional rack mounted and card based HSMs are not practical for many organizations because of issues accommodating the HSM’s size and deployment complexity. Additionally, rack space at shared data centers often includes physical server enclosures with metal mesh doors to secure access restricting available space.
With Yubico’s HSM solutions organizations can easily secure servers, applications, databases, assembly lines, IoT devices, cryptocurrency exchanges and more with a portable ‘nano’ form factor that allows fast and flexible deployment across diverse environments.
The YubiHSM 2 or YubiHSM 2 FIPS fits easily into a USB slot and lies almost flush to accommodate physical security enclosures.
- ‘Nano’ form-factor enables flexible deployment and use across devices and locations
- Fully concealed USB-A port deployment
- Network shareable for use by applications on other servers
Low-cost, High Security ROI
Cryptographic keys stored in software are susceptible to hackers and malware attacks. Alternately, traditional HSMs can be costly to deploy.
With Yubico’s HSM solutions organizations get enterprisegrade high cryptographic security and operations without the traditional HSM price tag.
- Significant Capex reduction: up to 90% cheaper than traditional HSMs
- Low-power usage device reduces business energy consumption
Rapid Integration, Easy Management
With the YubiHSM 2 SDK, developers can rapidly integrate support for either the FIPS or non-FIPS version of the HSM into business products and applications with capabilities like generating and importing keys, signing and verification, and data encryption and decryption. Developers can also make these features accessible through industry standard PKCS#11.
- Custom application support using open source libraries. Interfaces via YubiHSM KSP, PKCS#11, and native libraries
- Remote management reduces management complexity and costs
Address Existing and Emerging Use Cases
Secure Cryptocurrency Exchanges: The cryptocurrency market is growing rapidly, with a high volume of assets needing protection against emerging security risks. Several exchanges have been breached, all of which may have been prevented with a best practices security approach involving a hardware security module. With the YubiHSM 2 SDK, developers building solutions for cryptocurrency exchanges can rapidly integrate the HSM to protect cryptographic keys and keep sensitive financial information safe.
Secure Internet of Things (IoT) Environments: The Internetof-Things (IoT) is a rapidly emerging area where systems often operate in hostile environments.2 Cryptographic keys are used in numerous IoT applications, with insufficient security in place. This is partly because protecting cryptographic keys and enrolling certificates on IoT gateways or proxies has been complicated, and traditional HSMs are too large and unwieldy for certain IoT environments, such as connected cars. With the open source SDK, developers building IoT applications can rapidly integrate with the ultra portable YubiHSM 2 or YubiHSM 2 FIPS to protect cryptographic keys and keep critical IoT environments from falling victim to hostile takeovers.
Secure Cloud Services: Strong security for cloud environments is critical as organizations need to ensure that their data will be kept safe in the cloud. The HSM can be deployed in a data center and run as a component of a cloud infrastructure. Organizations can gain peace of mind knowing that the cloud hosting service of their choice is running the YubiHSM 2 or YubiHSM 2 FIPS as part of their offering.
To enable organizations to own and manage their own encryption keys in multi-cloud environments, YubiHSM 2 now has support for ‘Bring Your Own Key’ (BYOK). This enables organizations to securely and cost-effectively store and transfer data in a multi-cloud environment using an on-premises HSM for secure management of cryptographic credentials—enabling regulatory compliance and enhancing data security in a multi-cloud environment with better control, portability and flexibility, at a fraction of cost of traditional on-premises HSMs.
Secure Microsoft Active Directory Certificate Services: The HSM solution can provide hardware backed keys for an organization’s Microsoft-based PKI implementation. Deploying the HSM to the Microsoft Active Directory Certificate services not only protects the Certificate Authority private keys but also protects all signing and verification services using the private key.
Secure backups for HSM data: Backing up sensitive data from an HSM is an extremely security sensitive operation that generally requires an air-gapped security environment when symmetric cryptography is used for this operation. YubiHSM 2 offers the ability to wrap sensitive data for backup using asymmetric cryptography, ensuring that no secrets are exposed even if wrapped data is sent over the internet to another location.
Summary
The YubiHSM 2 and YubiHSM 2 FIPS enable organizations of all sizes to enhance cryptographic key security throughout the entire lifecycle, reduce risk and ensure adherence with compliance regulations. With the YubiHSM SDK 2.0 available as open source, organizations can easily and rapidly integrate support for the secure HSM into a wide range of platforms and systems for existing and emerging use cases where strong security is more critical than ever before.
