The urgency to harden cybersecurity defenses in manufacturing
The manufacturing industry is vital to everyday life and it impacts an array of sectors critical to daily operations.
Industries, such as manufacturing, that are part of critical infrastructure are often prime targets for cyberattacks. The rise of AI also enables malicious actors to craft convincing attacks at scale amplifying the attack surface. Stolen credentials gained through phishing or weak, legacy authentication processes pose as an entry point. Also the rise of software-defined power and agentic AI—specialized agents that optimize production and manage supply chains autonomously—introduces layers of risk that require every potential entry point to be hardened against unauthorized access.
Despite barriers to change, including legacy infrastructure, complex industrial and restrictive production floor environments, and the high cost of operational disruption, manufacturers face an imperative to move beyond passwords and are now considering modern authentication solutions to secure identities and modern cryptographic protection to secure servers, applications and computing devices.
Not all MFA is created equal
Multi-factor authentication (MFA) should be a first-line defense of any cybersecurity strategy to protect critical data, information technology (IT), and operational technology (OT) environments. And while any MFA is better than passwords, not all forms of MFA offer the same level of security or frictionless user experience. Legacy MFA—usernames, passwords, and mobile authenticators—is no match for AI-driven phishing. While shared workstations and legacy constraints create gaps where traditional MFA fails, leaders must juggle OT requirements with modern IT needs.
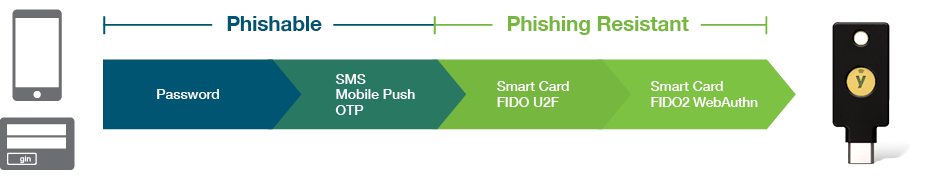
Stay ahead of evolving cyber threats and regulatory requirements with a proven solution which cannot be bypassed by malicious actors, unlike basic forms of MFA such as SMS, one-time passcodes and mobile authentication. Protect your critical infrastructure, stop phishing attacks and account takeovers before they start with modern, phishing-resistant MFA.
What is phishing-resistant MFA?
Phishing-resistant MFA processes rely on cryptographic verification directly between devices or between the device and a domain, making them highly secured against attempts to compromise or subvert the authentication process. A minimum standard met only by PIV/Smart Card and MFA based upon the FIDO2/WebAuthn standard.
Safeguard your IT and OT ecosystem with Yubico
Yubico solutions meet you where you are on your cybersecurity journey, while paving the way to a modern authentication infrastructure, and jumpstarting your plans to implement a zero trust framework. With Yubico solutions, you can be confident that your data and intellectual property are secured, and product integrity is always ensured.

The YubiKey
Secure human-to-machine communication
A pioneer in modern, hardware-based authentication and Yubico’s flagship product, the YubiKey is designed to meet you where you are on your authentication journey by supporting a broad range of authentication protocols, including FIDO U2F, WebAuthn/FIDO2 (passkeys), OTP/TOTP, OpenPGP and Smart Card/PIV. The YubiKey is IP68-certified and battery-free.

Yubico Hardware Security Module (HSM)
Secure machine-to-machine communication
The world’s smallest HSM, YubiHSM 2, packs a lot of power, and offers game changing cryptographic protection for servers, applications and computing devices. Secure your public key infrastructure (PKI) environments, encrypt your files and databases and securely sign code or any digital artifact to raise the bar for security for your IT and OT systems.

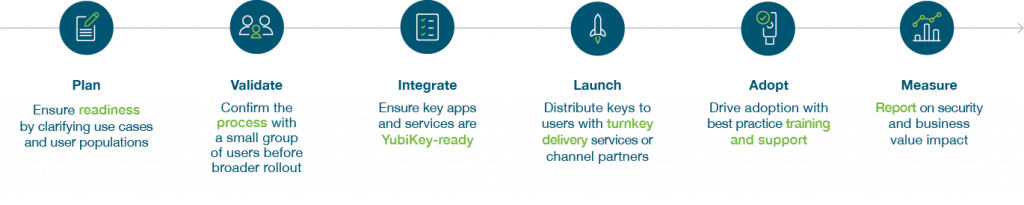
YubiKey as a Service
An industry-first cybersecurity service that fast tracks organizations to strong phishing resistance and passwordless at scale. Receive exclusive access to turnkey Enrollment and Delivery services that help IT get users quickly onboarded with YubiKeys. YubiKey as a Service offers a choice of form factors, replacement stock, and priority customer support.
Schneider Electric enhances global supply chain security with Yubico
As leaders in the digital transformation of energy management and the manufacturing of electric products, Schneider Electric worked closely with Yubico to deploy phishing-resistant YubiKeys to increase security with MFA in its power operation Supervisory Control and Data Acquisition (SCADA) system, a system common in manufacturing.
“As part of our IEC SL2 certification, we included MFA in our power operation system, well positioning us to meet SL3 requirements in the future. This is a point of differentiation for Schneider Electric.” – Chad Lloyd, Director of Cybersecurity Architecture for Energy Management, Schneider Electric
Lloyd was tasked with a challenge to integrate multi-factor authentication (MFA) on an isolated system—without the use of the Internet or traditional methods such as SMS. With the YubiKey, Schneider Electric is able to meet its requirement for MFA and to ensure only authenticated users can gain access to operate the SCADA system. Further, the YubiKey has helped reduce system interruptions during shift changes or when step-up authentication is needed for certain operations.
After positive results from the initial deployment of YubiKeys, Schneider Electric then expanded to solve additional use cases in managing its supply chain. Schneider Electric deployed the YubiHSM 2 with key vendors to proactively increase security within their supply chain. Creating a dual encryption process allows both the vendor and Schneider Electric to have confidence that products with the Schneider Electric brand are indeed authentic based on encrypted keys that are embedded by both companies during manufacturing.
Fluidra enhances its global workforce security with YubiKeys
The Fluidra Group is a multinational conglomerate of companies that develops, manufactures and distributes products for the pool market, operating in more than 45 countries with over 7,000 employees. Fluidra decided to deploy phishing-resistant YubiKeys to privileged users, namely those with elevated access to back-end systems or infrastructure. The YubiKey integrated seamlessly with existing infrastructure, supported by onboarding materials to streamline adoption.
As is the case for most organizations, Fluidra Group needed an authentication solution that would satisfy multiple use cases and extend beyond the core group of privileged users. After measuring the success of its first launch, Fluidra expanded deployment of YubiKeys to all employees for use at work and at home to support secure, anywhere access to cloud-based services including Google Workspace and the many other products, services and applications supported by the YubiKey.
Mitsubishi Electric strengthens global cybersecurity with the YubiKey
Mitsubishi Electric is a global leader in product innovation and the manufacturer of electrical and electronic products and systems, for consumers, businesses and a wide range of critical infrastructure including energy, transportation and information and communication systems. Established in 1921, Mitsubishi Electric is headquartered in Tokyo, Japan and globally active in over 120 countries.
As a key supplier of electrical and electronics products and solutions to critical infrastructure sectors worldwide, and a major supplier of Japan’s defense systems, it is paramount for Mitsubishi Electric to guard against persistent cyber attacks.
In order to guarantee that their investment in MFA was well suited, Mitsubishi Electric wanted to ensure that the solution met the standards set by the National Institute of Standards and Technology (NIST) Digital Identity Guidelines and the Authenticator Assurance Level (AAL), which are recognized worldwide as equitable standards for identity management. While implementing MFA at various divisions and affiliates, Mitsubishi Electric faced a variety of challenges including, frequently, mobile-restricted scenarios, as most production facilities limit the usage of any mobile devices.
The YubiKey emerged as an optimal solution for both IT and Operational Technology (OT), including access to industrial control systems (ICS), requiring no additional hardware, software, external power, batteries or network connections. Embracing Yubico solutions, such as the YubiKey, significantly raises the bar for security and establishes a robust foundation for Mitsubishi Electric to facilitate and safeguard its digital transformation by paving a path to secure authentication that does not require passwords.
Genetec eliminates passwords with the YubiKey
Genetec is an innovative technology company with a broad portfolio developing physical security hardware and software solutions. As a manufacturer of security products, and working with an extensive network of resellers, integrators, partners and consultants, Genetec wanted to create a security program that was based on identity strength. After smart cards proved challenging due to high costs and complex infrastructure requirements, Yubico worked with Genetec to pilot the lower cost YubiKey with embedded PIV/smart card features.
After a successful pilot, all 1200+ employees now use YubiKeys in their daily activities. To expand upon its security goals, Genetec then began distributing YubiKeys in much larger quantities to its partner ecosystem and to customers to log into and authenticate to various portals.
EasyMile is safeguarding their software supply chain
EasyMile develops software solutions for autonomous vehicles, mainly for vehicles used to transport people and goods. Founded in 2014, EasyMile is headquartered in Toulouse, France, and has an international presence, principally in the USA, Japan, and Australia.
To protect its fleet of autonomous vehicles, developed with the assistance of suppliers and other original equipment manufacturers (OEMs), EasyMile uses a Public Key Infrastructure (PKI) based on X.509 certificates to authenticate different assets and components to ensure the integrity of the software deployed. Practices focus on the authentication of differing assets and components, the integrity of the software deployed, and more.
Already users of YubiKeys for privileged accounts, EasyMile embarked on a project to harden its PKI infrastructure with the YubiHSM 2, which offers enhanced protection to safeguard cryptographic keys and certificates. With rapid returns on investment in both the YubiKey and YubiHSM 2, EasyMile continues to work with Yubico Professional Services to explore expanded use cases, focusing on both internal and external uses.
Securing critical infrastructure at an Asia-Pacific energy company
Energy systems, like manufacturing, are a growing target for cyber criminals. For this leader in electricity distribution in Asia-Pacific, serving millions of customers, much of the responsibility for protecting operations from cyberattacks falls to the OT Security Specialist, a job which sits at the border between IT and OT.
During the procurement process of an authentication solution, the Anonymous Energy Company had to balance multiple requirements. It was important that the product would also integrate easily with existing infrastructure, without requiring additional software. This ruled out one possible solution—smartcards—which require specific drivers and smartcard readers to function. The OT Security Specialist was also keen to find a solution that was user-friendly.
The OT Security Specialist was most attracted by how YubiKeys balanced security and usability: “if you’ve got to physically touch the button, you know a user is physically there using it. We could set up one YubiKey as MFA for all a user’s accounts, so they don’t need six different TOTPs.”
To protect the hardware and live equipment upon which distribution lies, the organization chose the YubiKey to secure all users who access the operational environment—offering a balance of security and usability and the ability to deploy it without additional software. Further, the flexibility of YubiEnterprise Subscription helps guarantee the highest level of protection into the future.
The path forward to phishing-resistant MFA at scale
No matter where you are on your MFA journey, we’ll meet you there. You can accelerate your zero trust approach and gain a bridge to a passwordless future. With a tried and true process that many organizations have followed already—and with services to help deploy phishing-resistant and passwordless at scale—it’s not a matter of if you’ll be successful but when you’ll be successful in raising your bar for security with modern, hardware-backed passkeys such as the YubiKey
A worthwhile investment that not only shows that you care about the safety of employee authentication experiences, and cybersecurity across your supply chain, but will drive competitive differentiation and bolster you as a thought leader.