Secure Manufacturing
Because security is never stronger than its weakest link, we have considered the full lifecycle of our products, from component sourcing, through manufacturing, to integration within a customer system, to ensure the highest levels of security.
Made in Sweden & USA
Yubico is a Swedish company that owns subsidiaries in the USA, UK and Germany. We strongly believe there are security and privacy benefits for our customers by manufacturing and programming our products in Sweden and the USA.
To ensure that we are very close to all aspects of manufacturing, we have set up production where we are geographically based. That means we manufacture and finish our parts close to our two main offices in Sweden and the USA, where we can make continuous improvements while keeping a tight control over what’s made.
Secrets Protected with Secure Elements
Yubico products are built on state-of-the-art secure elements, used for the majority of smart card payment cards and passports, providing a high degree of resilience for secret information. The design of the YubiKey minimizes the attack surface, by moving storage of cryptographic keys and secure processing away from the computer and into an external dedicated hardware authentication device. In today’s highly complex systems, this is becoming increasingly important.
Device Protections
By using secure elements within the YubiKey, both the Yubico software and hardware is protected in a way that makes it very difficult to tamper with.
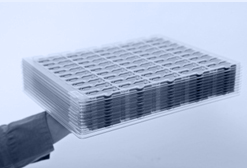
We have invented a new and efficient way to manufacture the USB YubiKeys — in one solid and robust piece of plastic. We use a high degree of automation for electronics assembly to molding, testing, laser marking and packing of our products. Yubico products are available in tamper-evident blister packaging for YubiKey sales on Yubico store and Amazon.com.
Yubico offers an online portal for users to test the authenticity of your YubiKey.


Customer Controlled Secrets
YubiKeys are delivered to our logistics centers as “stem cells”, with the means to prevent any modifications during transit and storage. The authentication and encryption features are programmed at the time of shipment to customers. Customer cryptographic secrets are not stored by Yubico, and customers may choose to use their own computers and equipment for programming.
All YubiKeys sold on our web store can be programmed by customers using our free programming tools. Cryptographic keys cannot be read out from the device.
Yubico OTP Security
For high-security applications, we recommend the use of our public key offerings, including FIDO2/WebAuthn, FIDO U2F, GPG, and PIV.
For one-time password (OTP) applications, the Yubico OTP supported in the YubiKey offers enhanced security compared to traditional OTP tokens. Because the YubiKey automatically enters the passcode for you, we have chosen the full 128-bit key strength, represented by a 32 ModHex character passcode, offering a level of security several magnitudes higher than the common 6 or 8 digits. To further enhance security, the Yubico OTP is offered with an optional time variant code. The YubiKey has no battery but features a built-in clock that uses the power from the USB port or NFC (in supported models). This clock can be used to measure the time between two OTPs, verifying user presence so that pre-recorded OTPs cannot be used.
Communications Security
While Yubico previously initiated development of a BLE security key and contributed to the BLE U2F standards work, we decided not to launch the product as it does not meet our standards for security, usability and durability. BLE does not provide the security assurance levels of NFC and USB as it can be intercepted within 20 meters, and is a more complex protocol with a larger attack surface. Also, it requires batteries and pairing that offer a poor user experience.
Yubico is a believer in NFC, and the YubiKey design has proven at scale to deliver a superior contactless user experience.
FIDO Ecosystem Security
YubiKeys need websites, browsers, and operating systems to work in harmony to protect people. Therefore, to achieve a trusted Ecosystem, the security of browsers and devices are critical.
Attestation
Attestation is built-in to the FIDO and WebAuthn protocols, which enables each service provider to choose which security keys to trust, or to be more skeptical of, based on their individual needs and concerns. Each vendor can provide root attestation certificates which can be used to verify the authenticity of any security key they produce. The root certificate that issues all YubiKey attestation certificates is available at: https://developers.yubico.com/U2F/yubico-u2f-ca-certs.txt. This covers both U2F and FIDO2 devices.
More information for developers and administrators, including our recommendations on how to use attestation in a scalable way, can be found here.
Securing Secrets on Servers
We use our own cost-efficient and convenient YubiHSM hardware server module to protect access to all Yubico servers and systems, including for OTP secrets for YubiCloud, Yubico’s hosted validation service.
Technical Transparency
We are a strong believer in transparency and do whatever we can to provide documentation and open source software and libraries. We are also committed to ongoing work with third parties for certifications, security reviews and scrutiny.
The Yubico team, investors and advisors, have a long proven track record and are well respected in the security industry and open standards communities. Our goal has always been to be transparent and take responsibility for the quality and integrity of our products.
Since 2014 and the launch of FIDO U2F in Gmail, Yubico has donated and discounted YubiKeys to journalists, dissidents and non-profit organizations working for civil rights. Learn more about the program here.
Certifications
Yubico’s products are certified against FIPS, FIDO, and CSPN to meet the compliance needs of some of our customers. However, as mentioned throughout, our investment in the safety and security of our products goes far beyond what these require. We do this in order to provide the safest products we can, and because most certifications focus on interoperability, few review cryptographic code, and none cover total system architecture, implementation, and supply chain security. You can read more about what FIDO certifications cover on their website, and what NIST’s FIPS certification covers on the NIST website.