YubiKey – Countless integrations
Showcase your integration and promote your solution by joining our extensive catalog of business and personal applications, devices, and services that support authentication with YubiKey.
The Works with YubiKey program
One place to showcase your product’s integrations and find all the ways you, your customers, or employees can stay secure with a YubiKey

Showcase your commitment to security
We welcome all product and solution owners that integrate with the YubiKey to join the hundreds of companies already dedicated to showcasing how they protect their users’ identities, accounts, and data with a FREE listing on the Works with YubiKey catalog.

Find all the ways you can stay secure with a YubiKey
Own a YubiKey? Whether it is for work or personal use, or both, leverage the Works with YubiKey program to find all the dynamic ways you can stay secure online, at work, or on your favorite device with helpful tips and how-to guides.

Reach new customers and grow your business
Increase your integrated solutions’ visibility with a new revenue stream by keeping your Works with YubiKey listing up-to-date with the latest product alignment, reference material, and special offers unique to YubiKey users and turn page visitors into new customers.
Together, let’s create Zero Trust for all
Yubico & our partners are making the internet more secure for everyone through great partnerships that fuel innovation, accelerate growth, and build best-of-breed services to stop account takeovers at scale
Partners are at the heart of everything we do and through our Partner Spotlight video series, we’ll highlight our key partners and the work we’re doing together to deliver passwordless and Zero Trust for our customers.
Ready to create your own self-verified listing in the Works with YubiKey catalog? Watch this video before getting started, download the checklists below to prepare your integration review and catalog listing, then continue scrolling down this page to click on the “Start your self-verified listing today” button.
Integration checklist (PDF)
Join the Works with YubiKey program
Whether you have a passive product integration, or an interest in pursuing a business partnership with Yubico, the Works with YubiKey program offers a choice of two membership tracks to select the level of engagement that makes the most out of your integration with the YubiKey.

Self-verified integration
Designed for companies building support for the YubiKey but not looking to commit time towards any joint go-to-market commitments. The self-verified integration allows companies to verify their YubiKey integrations using our checklist, and showcase your product with a FREE listing on our user-trusted Works with YubiKey catalog.

Yubico-verified integration
This track puts our business development and partner marketing engines to work to jointly solve customer needs and win business. Tell us about your YubiKey integration, your strategic business goals, and how we can work together as partners.
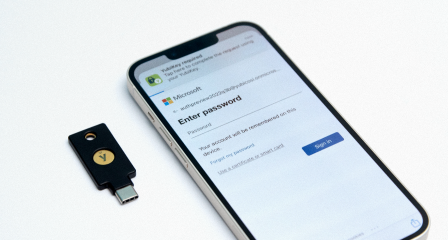
Your YubiKey can be used with hundreds of apps, services, and devices with more being added every week.
Click a category below to narrow your search and find more integrations you can utilize with your YubiKey.
Learn about our additional partner programs

Channel Partner Program
Engage with Yubico to provide industry leading phishing-resistant MFA solutions to help secure employees and supply chains and meet new industry and government compliance requirements. Whether you provide solutions, deliver services, resell or distribute technology products, our channel partner program ensures you can serve your customers, differentiate, and grow your business.

Developer Program
Join our developer program if you or your organization is interested in learning more about the protocols the YubiKey supports or want to get started with available open source libraries and software projects.
Visit developers.yubico.com to get started today
Get started
Explore our library of solution briefs, videos and more