What is a One-Time Password (OTP)?: Limitations and modern alternatives
A one-time password (OTP) is a string of characters or numbers that authenticates a user for a single login session or transaction. While OTPs represent a significant security improvement over static passwords alone, they share a critical vulnerability: they can be phished. Modern security frameworks now mandate phishing-resistant authentication for this reason.
Key Takeaways
- OTPs are vulnerable to phishing. OTPs are susceptible to real-time phishing and man-in-the-middle (MitM) attacks because they verify only the code, not the login context. Attackers can trick users into entering valid OTPs on fake sites, and then relay them in order to breach accounts.
- Software authenticator weakness. While better than SMS, apps like Google and Microsoft Authenticator remain vulnerable to the primary OTP threat: real-time phishing through MiTM attacks. Even when an OTP is generated on a device with a secure element, such as a hardware security key or a smartphone, an attacker can still intercept a valid code as the user enters it on a fraudulent site and immediately relays it to the legitimate service. Regardless of where the OTP is generated, this will always be a limitation of OTP as a protocol – the code itself has no awareness of who or which site is requesting it.
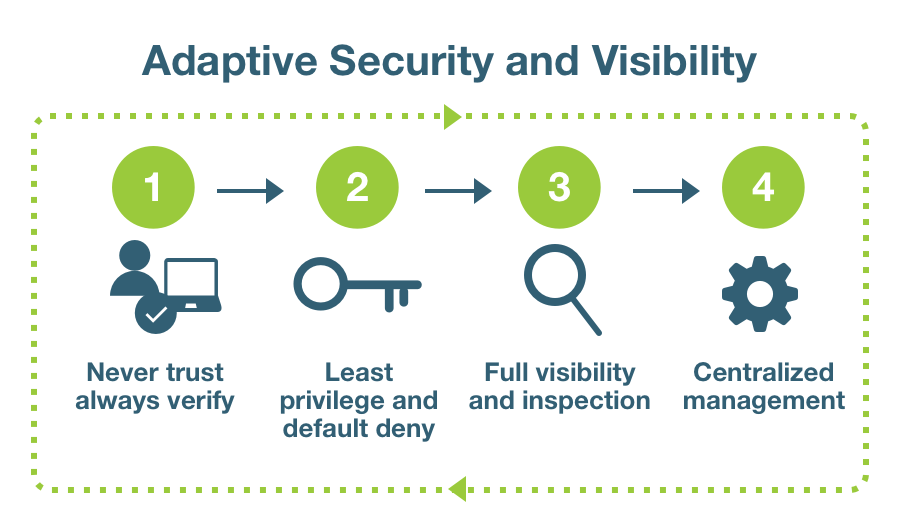
- Misaligned with Zero Trust. Zero Trust requires “never trust, always verify” with high assurance. OTPs provide some level of protection but because the codes can be stolen and used by attackers, they cannot be fully trusted, which is why modern frameworks mandate phishing-resistant MFA based on standards like FIDO.
- Hidden business costs. OTPs create IT helpdesk overhead from account lockouts and lost devices, and reduce productivity. Cyber insurance carriers are increasingly requiring MFA, and with the advancements in passkeys, more insurance policies are expected to demand phishing-resistant authentication in the very near future. Check with your cyber insurance company to understand their MFA requirements to ensure you are fully covered today and for the near future. Phishing-resistant MFA reduces financial risk and operational friction.
- OTP is better than no MFA. Any MFA will dramatically improve your risk posture over passwords alone. As you are working on your journey to phishing-resistant authentication, it is important to still deploy MFA as soon as possible to protect access.
Compromised credentials are a factor in the vast majority of data breaches, making the static password’s failure as a security mechanism well-documented. This weakness prompted a necessary evolution in access management, such as the adoption of the OTP as a second factor from around the mid-2000s, which even accelerated through the early 2010s. An OTP adds a crucial layer of security, but as attack methods have matured in the years since their proliferation, the limitations of this technology have become critically important for technical and security leaders to understand.
According to Yubico’s 2025 Global State of Authentication survey of 18,000 employed adults, 41% still place their trust in vulnerable SMS-based authentication, despite most cyber attacks being the direct result of stolen login credentials.
What is a One-Time Password?
A One-Time Password (OTP) is a string of automatically generated characters or numbers that authenticates a user for a single login session or transaction.
Unlike a static password that can be reused, an OTP becomes invalid after its one and only use, or expires after a short period of time, a characteristic that makes it resistant to replay attacks. This means that if an attacker manages to capture a used OTP, it provides no value for future access attempts. It should also be noted that OTPs are only used as a secondary factor and are not meant as a password replacement to provide account access.This form of multi-factor authentication (MFA) works by combining something the user knows (i.e., their static password) with something they have (i.e., access to the device that receives or generates the OTP). The generation of these codes relies on cryptographic algorithms that create a shared secret between the user’s authenticator and the authentication server.
The primary OTP standards are:
- HOTP (HMAC-based One-Time Password): HOTP is an event-based algorithm. It uses a secret key and a counter that increments every time a new password is requested. The server and the user’s token or app keep their counters in sync to validate the code. An HOTP code remains valid until it is used.
- TOTP (Time-based One-Time Password): TOTP is the more common algorithm used by authenticator apps like Google Authenticator and Microsoft Authenticator. It uses the current time as a moving factor instead of a counter. The secret key is combined with a timestamp, typically creating a new code every 30 or 60 seconds. This short lifespan dramatically reduces the window of opportunity for an attacker to use a captured code.
YubiOTP (Yubico OTP): A simple yet strong authentication mechanism supported by YubiKeys out-of-the-box. Each YubiKey can generate a 44-character long alphanumeric string with a simple touch, and can be used as the second factor in a 2-factor authentication scheme that requires no client software It provides an alternative to HOTP and TOTP, which both require an app or mobile device to authenticate. Using YubiCloud for validation, Yubico OTP is easy to implement and eliminates telecommunications costs while providing better user experience than mobile-based alternatives.
YubiKeys support all three OTP standards, providing a secure hardware-based option for organizations that cannot immediately transition to passkeys. For enterprises still relying on OTP-based authentication, YubiKeys offer a bridge to modern phishing-resistant authentication, delivering OTP functionality today while supporting a seamless migration to FIDO2/WebAuthn when the organization is ready. For developers and technical teams interested in understanding how Yubico OTP works, see the Yubico OTP technical documentation.
Common OTP delivery methods and their risks
The security of an OTP system is fundamentally tied to the method used to deliver the code to the user. Each method presents a different balance of usability and vulnerability.
- SMS text message: Sending an OTP to a user’s registered phone number via SMS is a widespread practice due to its simplicity. However, it is widely considered the least secure delivery method. The system is vulnerable to SIM swapping attacks, where a malicious actor convinces a mobile carrier to transfer the victim’s phone number to a SIM card they control, allowing them to intercept the OTPs directly. Flaws in telecommunication protocols like SS7 can also be exploited to intercept text messages. SMS is also subject to telecommunication cost and international revenue share fraud where SMS MFA is exploited to generate fraudulent telephony charges.
- Authenticator app: Software applications on a mobile device generate TOTP codes locally. This approach is more secure than SMS because it is not susceptible to SIM swapping, however, it is not without risk. If the user’s smartphone is compromised by malware, an attacker could potentially steal the secret keys stored within the authenticator app, allowing them to generate the same codes as the user.
- Traditional hardware OTP tokens: Sometimes referred to as “fobs”, these are standalone, battery-powered devices commonly used for corporate or customer banking access. They feature a built-in LCD screen that displays the OTP directly on the device itself. Because they are completely air-gapped—meaning they do not physically connect to the computer or phone—they are immune to malware. However, the user experience requires manually reading the code from the tiny screen and typing it into the login prompt before it expires. A critical limitation is their reliance on a sealed internal battery; once depleted (usually after a few years), the device ceases to function and the entire physical token must be replaced.
Modern hardware security keys: Modern devices, such as the YubiKey, are purpose-built hardware security keys that connect directly to a computer or smartphone via USB or NFC. Unlike traditional hardware OTP tokens, they do not have screens or batteries. When used for OTPs, the hardware key securely stores the cryptographic secrets, but relies on a companion app (like the Yubico Authenticator) running on the host device to display the codes. Alternatively, in proprietary modes like YubiOTP, the key acts as a keyboard, seamlessly “typing” the long passcode into the field when touched, eliminating the need for manual entry entirely.
Not all OTPs are created equal
While all OTPs share the same critical vulnerability to phishing and MiTM attacks), there are meaningful differences in how securely OTPs are generated and stored.
SMS-based OTPs are the most common but least secure method. Relying on mobile carrier networks introduces unique attack vectors, most notably SIM swapping, where attackers socially engineer a carrier to transfer the victim’s phone number to a new SIM card. Additionally, the underlying signaling protocol (SS7) used by global cellular networks has known vulnerabilities that allow sophisticated attackers to intercept messages in transit.
Authenticator apps represent a significant security upgrade to SMS. A code generated by an app is more secure because it remains local to the device, making it immune to SIM swapping and cellular network intercepts. Furthermore, modern smartphones leverage secure enclaves or virtualized security modules to encrypt the OTP seeds, protecting them from extraction even if the phone is infected with malware.
Traditional hardware OTP tokens offer moderate protection for high-value targets. These standalone devices are completely air-gapped, meaning they have no data connection to the outside world, rendering remote key extraction impossible. However, they rely on internal batteries that eventually die, requiring full device replacement, and they still rely on the user manually reading and typing the code, leaving the workflow vulnerable to human error.Modern Hardware Security Keys represent the gold standard for OTP generation. These distinct, battery-free devices generate codes using hardware-isolated cryptographic secrets within a purpose-built secure element. Unlike software authenticators, they are isolated from the general-purpose computing environment of a laptop or smartphone. While they can display codes via a companion app, they can also utilize proprietary schemes (like YubiOTP) to input the long passcode directly into a text field, combining high security with user convenience. Most importantly, they offer a practical migration path from OTP-based authentication to phishing-resistant methods like FIDO2 that eliminate the MiTM vulnerability entirely, making them the ideal choice for organizations committed to long-term security.
The environmental blind spot: When OTP authentication fails in the real world
An authentication method’s security cannot be evaluated in a vacuum; its effectiveness is ultimately determined by its practicality in real-world operational environments. Mobile-reliant OTP delivery methods, including SMS, authenticator apps, and push notifications, frequently fail not because of a digital vulnerability, but because the physical or operational context makes them impractical, insecure, or simply impossible to use. This environmental blind spot represents a significant risk to both security and business continuity.
Many high-security environments explicitly forbid the use of personal mobile devices. In secure government facilities, sensitive research labs, and on controlled manufacturing floors, a “no phone” policy is standard practice. When a user’s primary authentication method is tied to a potentially prohibited device, they may be locked out of critical systems, halting productivity, resulting in organizations being forced to create insecure workarounds to grant access.
This operational friction is magnified in high-turnover, shared-workstation environments. Consider a hospital’s nursing station, a retail point-of-sale terminal, or a busy call center. Assigning a personal mobile device as the authenticator for every user presents significant challenges, even with role-based access control systems.
Security gaps are created if employees share login details to bypass OTP friction, and it complicates the process of provisioning and de-provisioning access for shift workers or temporary staff. A more robust authentication solution must be tied to the user’s digital identity, not to a personal, transient mobile device. Moreover, for field operations in sectors like energy, logistics, or emergency services, reliable cellular or internet connectivity is not guaranteed. In these scenarios, OTPs that rely on receiving a text message or syncing with a cloud-based authentication server can become problematic, though some solutions now offer offline authentication capabilities.

The critical vulnerability: OTPs can be phished
The most significant OTP vulnerability is that it does not protect the user from being tricked. OTPs, regardless of the delivery method, are vulnerable to real-time phishing and MitM attacks. This is because the system is designed to verify a static code, not the context in which that code was entered.
Here’s how a typical MitM attack defeats OTP-based MFA:
- The lure: An attacker sends a phishing email or text message that directs a user to a fraudulent but identical-looking clone of a legitimate login page (e.g., a fake Microsoft 365 portal).
- The intercept: The user, believing the site is real, enters their username and static password. The attacker’s server captures these credentials and passes them to the real website in real-time.
- The relay: The legitimate service, having received valid credentials, proceeds to the next step and sends an OTP to the user’s phone or authenticator app.
- The deception: The user enters the received OTP into the fraudulent website. The attacker captures this code and immediately uses it to complete the login process on the legitimate site.
In this scenario, every component of the security system worked as designed. The password was correct, and the OTP was valid. The failure occurred because the human user was deceived into acting as a bridge between the legitimate service and the attacker. The system successfully verified the user’s identity but failed to verify that the user was interacting with the intended service.The vulnerability of OTPs to phishing is not theoretical. Yubico’s 2025 Global State of Authentication survey found that password compromise rates remain alarmingly high, with respondents reporting compromised passwords across social media, online retailers, and banking apps—attacks that OTP-based MFA failed to prevent.
Beyond verification: Why OTPs fall short in a Zero Trust world
Phishable authentication methods like the OTP are fundamentally misaligned with modern Zero Trust security architectures. The core principle of Zero Trust is generally expressed as “never trust, always verify,” which demands that every access request is authenticated with a high degree of assurance before being granted. An OTP, however, provides a low-assurance signal. Because the authentication code can be phished and replayed by a hacker in real-time, an organization can never truly trust that a successful OTP validation confirms the legitimate user’s presence.
This deficiency is not just a theoretical weakness, it is a critical gap recognized by leading cybersecurity frameworks and government mandates. The U.S. government’s executive order on cybersecurity, and the corresponding OMB M-22-09 memorandum, explicitly require federal agencies to adopt phishing-resistant MFA as a cornerstone of their Zero Trust strategies.
These mandates acknowledge that any authentication method vulnerable to social engineering fails to provide the strong verification needed to protect sensitive data and critical infrastructure. Relying on a phishable OTP for access management is like building a fortress and leaving the key under the doormat – it undermines the entire security posture.
The contrast with modern solutions like passwordless authentication is stark. Phishing-resistant authenticators, based on standards like FIDO, do not simply verify a code; they create a cryptographic binding between the user, their device, and the specific service they are accessing. As such, the process also validates the origin of the service, ensuring the user is not on a fraudulent site. This provides the high-assurance, tamper-proof signal required for a true Zero Trust model, confirming not just the user’s identity but also the integrity of the entire login ceremony.
The hidden costs of OTP systems
The perceived affordability of legacy OTP systems masks significant and escalating business costs that are often overlooked. The true total cost of ownership (TCO) for implementing OTP as an authentication scheme extends far beyond deployment costs, manifesting in drained IT resources, and lost user productivity. Continuing to rely on phishable MFA is no longer just a security risk, it is a direct threat to the organization’s bottom line.
OTP systems generate immense operational friction, telecommunication carrier costs and hidden IT overhead. A significant portion of helpdesk tickets are statistically related to MFA issues: users who have lost or replaced their mobile device and need OTP reconfiguration, SMS delivery failures, authenticator app synchronization problems, or account lockouts from expired or failed OTP codes. Each ticket consumes valuable IT staff time that could be dedicated to strategic initiatives. This constant support burden, coupled with the productivity lost by employees unable to access their accounts, represents a substantial and ongoing operational expense.
Moving beyond OTPs to phishing-resistant MFA
The inherent vulnerability of OTPs to phishing has led the cybersecurity industry and government bodies to advocate for a shift toward phishing-resistant MFA. These advanced authentication solutions are designed to be immune to the kinds of social engineering and MitM attacks that defeat OTPs.
The key difference is that phishing-resistant methods create a cryptographic binding between the user, their device, and the origin (i.e., the website or service, also referred to as the relying party) they are trying to access. Standards likeFIDO2 and WebAuthn are at the forefront of this evolution, commonly known as passkeys. When a user registers with a relying party, a unique public-private key pair is created. The private key is stored securely on the user’s device, such as aYubiKey, and never leaves it, while only the public key is transmitted.
During login, the relying party sends a randomly generated challenge, which the device signs using the private key. This digital signature is unique to that specific session and relying party. If a user were hypothetically tricked into visiting a fake site, the browser would recognize that the domain does not match the origin associated with the key, and the authentication would instantly fail. Additionally, an attacker cannot intercept the digital signature and replay it elsewhere because the cryptographic signature would then not correspond to any randomly generated challenges generated during future sessions.
Beyond security: Business benefits of phishing-resistant MFA
Phishing-resistant authentication addresses not only the technical vulnerabilities of OTPs but also critical business requirements:
Cyber insurance positioning: Cyber insurance carriers are increasingly requiring MFA, and with the advancements in passkeys, more insurance policies are expected to demand phishing-resistant authentication. Organizations should check with their cyber insurance company to understand their MFA and security posture requirements to ensure full coverage today and for the near future, since the adoption of phishing-resistant MFA is becoming a critical factor in financial risk management.
Reduced operational costs: Hardware security keys eliminate the mobile device dependency that drives helpdesk tickets, working across different devices without reconfiguration. This reduces IT support burden and improves user productivity.
Investing in modern, phishing-resistant authentication solutions is not merely a security expenditure; it is a strategic decision that reduces IT support overhead and prevents the multi-million dollar financial fallout of a successful breach.
Strategic considerations for security leaders
Understanding the limitations of OTPs is essential for senior managers, engineers, and especially IT decision-makers building a robust cybersecurity posture. While OTPs are a valuable step up from static passwords, they should not be considered the final destination for access management.
Organizations should prioritize phishing-resistant MFA wherever possible. For applications that cannot yet support phishing-resistant solutions, OTPs provide an acceptable interim security layer. However, for privileged users, administrators, and anyone with access to sensitive data or critical infrastructure, deploying phishing-resistant MFA is essential. This strategy not only mitigates the risk of account takeovers but also provides a path toward a fullypasswordless environment, which can reduce IT support costs and improve the user experience.
The focus of modern authentication has shifted. It is no longer enough to verify a user has the correct code; a secure system must also verify the authentication context, ensuring the entire authentication process is bound to the intended service and immune to deception.
Awareness remains a barrier. Globally, 45% of those who have never used a passkey said it was because they had never heard of them, highlighting that the challenge is not technological complexity, but education and awareness.
Yubico products and solutions: Securing beyond OTP with phishing-resistant authentication

Yubico offers a comprehensive suite of hardware security keys and enterprise services that provide a more secure alternative to vulnerable one-time passwords, addressing the key limitations discussed throughout this article.
- The YubiKey 5 Series provides multi-protocol support, including FIDO2/WebAuthn, Smart Card (PIV), and other authentication methods, making it ideal for organizations transitioning from legacy OTP solutions to phishing-resistant authentication across diverse environments.
- The YubiKey Bio Series combines hardware security with biometric verification, offering a convenient fingerprint-based login with PIN fallback, perfect for shared workstation environments that support phishing-resistant MFA.
- The YubiKey 5 FIPS Series delivers FIPS 140-2 validated authentication meeting the highest assurance requirements (AAL3), essential for government agencies and regulated industries. The YubiKey 5 FIPS Series supports both OTP and FIDO2/WebAuthn protocols, enabling organizations to transition from legacy OTP solutions to phishing-resistant authentication..
- The Security Key Series offers a simplified, FIDO-only authentication solution, providing a cost-effective option for organizations that need essential phishing-resistant protection without the multi-protocol capabilities of other YubiKey models.
Enterprise services
YubiKey as a Service provides subscription-based access to YubiKeys with flexible upgrade options, which allows organizations to implement phishing-resistant MFA across their workforce at a predictable cost that’s “less than a cup of coffee per user per month,” addressing the TCO concerns raised in the article.
Bridge solutions for legacy systems
OTP-based authentication remains widely deployed and provides significantly better protection than passwords alone. For organizations that cannot yet implement phishing-resistant MFA due to technical limitations, YubiKeys offer hardware-based OTP with distinct operational advantages over mobile authenticators.
YubiKeys work across different platforms and vendors without reconfiguration, eliminating the mobile device dependency that drives helpdesk tickets. Users can either tap the key to automatically enter a YubiOTP code or use the Yubico Authenticator app to view and enter a TOTP code. The app can be installed on multiple devices, allowing one YubiKey to work across all of them without relying on cloud synchronization. For organizations that must continue using OTP-based authentication, Yubico’s OTP options provide a more secure and operationally efficient path forward.
Key advantages of YubiKey OTP:
- Cross-device compatibility: Works on mobile and desktop without reconfiguration
- Reduced helpdesk burden: No lost device issues, no SMS delivery failures
- No telecommunication costs: Eliminates SMS fees and IRSF vulnerabilities
- Hardware isolation: OTP secrets stored in tamper-resistant hardware
- Investment protection: Same hardware supports phishing-resistant FIDO2/WebAuthn
YubiKeys support OTP standards on the same hardware that enables phishing-resistant FIDO2/WebAuthn authentication, allowing organizations to improve security and reduce operational friction today while building a clear path to their long-term security goals.