Tag: Hardware Security Module
-

Yubico Expands FIPS 140-2 Certification to YubiKey 5 Series and YubiHSM2 Today, we are happy to share that the YubiKey 5 Series firmware has completed testing by our NIST accredited testing lab, and has been submitted to the Cryptographic Module Validation Program (CMVP) for FIPS 140-2 certification, Overall Level 2, Physical Security Level 3. Soon, the YubiKey 5 Series firmware will also be submitted for FIPS […] Read more -

YubiHSM 2 Now Compatible with EJBCA from PrimeKey The YubiHSM 2, the world’s smallest hardware security module from Yubico, is now compatible with EJBCA software for a range of public key infrastructure (PKI) use cases. Available for all YubiHSM 2.1 and newer devices, Yubico’s updated Setup Tool, which adds support for PrimeKey EJBCA, is accessible in our latest YubiHSM 2 open source software […] Read more -

YubiHSM 2 Now Qualified for AWS IoT Greengrass Hardware Security Integration We are excited to announce that Amazon Web Service (AWS) Internet of Things (IoT) Greengrass users can now use Yubico’s hardware security module, the YubiHSM 2, Yubico’s ultra-portable hardware security module, for secure key storage. AWS IoT Greengrass software provides local compute, messaging, and data caching for the IoT devices, enabling users to run IoT […] Read more -

YubiHSM 2 is here: Providing root of trust for servers and computing devices If you were to ask someone who Yubico is or what we do, you’ll likely get the answer, ‘YubiKeys’, and rightfully so. YubiKeys are our foundation, and at the core of our mission to provide tried-and-true multi-factor authentication since 2008. They are used and loved by some of the world’s largest companies and by millions […] Read more -

Yubico Launches YubiHSM 2: The World’s Smallest and Best Price/Performance Hardware Security Module, Providing Root of Trust for Servers and Computing Devices PALO ALTO, CA – October 31, 2017 – Yubico, the leading provider of authentication and encryption hardware devices for the modern web, today launched the YubiHSM 2, a new, cost-effective Hardware Security Module (HSM) for servers and IoT gateways. The product delivers the highest levels of security for cryptographic digital key generation, storage, and management, […] Read more -
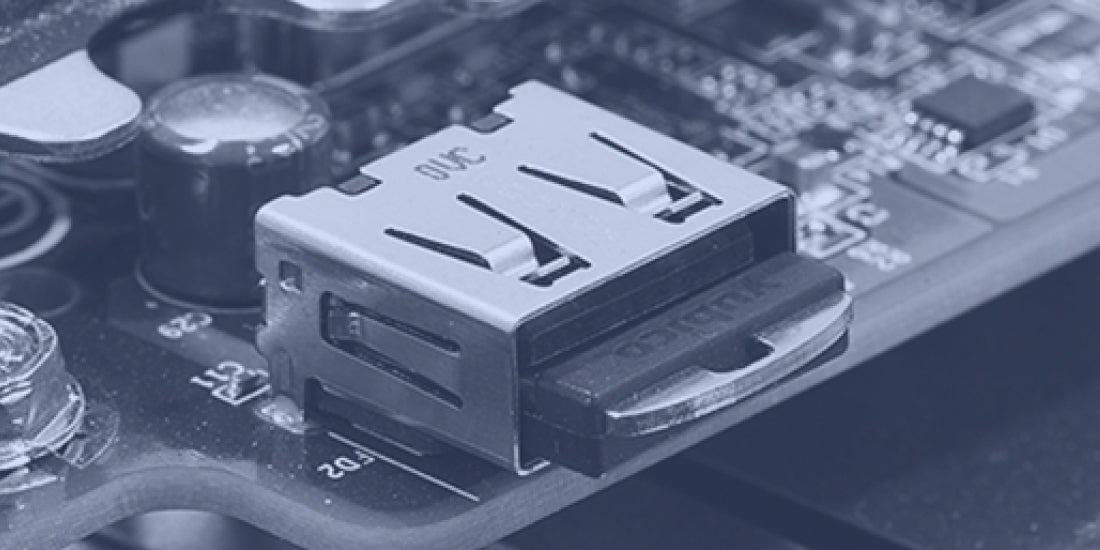
YubiHSM 2 open beta launched! With IT security breaches becoming a staple in daily news reports, organizations big and small alike need to ramp up their defense. More than 95% of all IT breaches happen when a user credential or server gets hacked. While the YubiKey protects user accounts from remote hijacking, millions of servers storing sensitive data still lack […] Read more