Tag: government
-

Portable root of trust for government The YubiKey is a portable root for remote workers, non PIV/CAC eligible workers, mobile/BYOD, and shared devices/workstations. Read more -

Why 3 government agencies are relying on hardware-based MFA with YubiKeys America’s government is under attack. To put it more accurately, its governments are under attack, all the time, at every level — federal, state, and local — from opportunistic scammers, sophisticated cybercriminals, and even state actors. We’ve all seen the stories about intelligence services stealing political emails, snooping into election systems, and even penetrating the US power grid. But those are just […] Read more -

YubiKey for elections and political campaigns The YubiKey: Modern security and exceptional UX Relying on username and passwords or legacy mobile-based authenticators such as SMS, OTP and push notification apps for user authentication is common, but usernames and passwords are easily hacked, and not all multi-factor authentication (MFA) is created equal. Mobile-based authenticators are highly susceptible to modern cyber threats such […] Read more -

Preserving democratic integrity and election security is a job for all of us As we enter the final month of the 2020 U.S. presidential race, election security and fraud is top of mind for many. With the memory of the 2016 Podesta breach still fresh, we are a nation braced for cyber-attack impact. Experts agree that, while countless security improvements have been made since 2016, we should expect more vigorous phishing attacks, data theft, […] Read more -

How NIST and eIDAS revisions are shaping the future of e-identification This blog is co-authored by John Fontana, Standards Analyst at Yubico. On both sides of the Atlantic, standards and regulations on electronic identification are being revised more or less simultaneously. In the United States, the National Institute of Standards and Technology (NIST) accepted public comments on its SP 800-63-3 Digital Identity Guidelines last month, which is on […] Read more -
YubiKey for mobile for public sector solution brief Securing mobile, tablet and notebook users with high-assurance multi-factor authentication. Read more -

5 reasons why the government and other public sector agencies should care about WebAuthn Federal, state and local governments and other public sector agencies have important responsibilities that support a functioning community – everything from national security to public transit, public education, public safety, state parks, financial services, energy and power grids, and many more services are all tax funded and managed by the public sector. While these are […] Read more -

Acing election security in 2020: A conversation with Defending Digital Campaigns 2020 is a big year for the US electoral system, and with society moving to a remote structure amidst the current climate, elections may very well be the next big sector to feel an impact. US citizens could find themselves voting entirely remote — possibly through mobile phones or otherwise — changing the election security […] Read more -

YubiKey secures remote workers during COVID-19 as government-approved alternative to PIV and CAC cards In the matter of just one week, Google reported that it saw more than 18 million daily malware and phishing emails related to COVID-19. That’s an astonishing number, and one that is not likely to slow down any time soon. For organizations across the globe, it is imperative to quickly, securely, and affordably fill existing […] Read more -
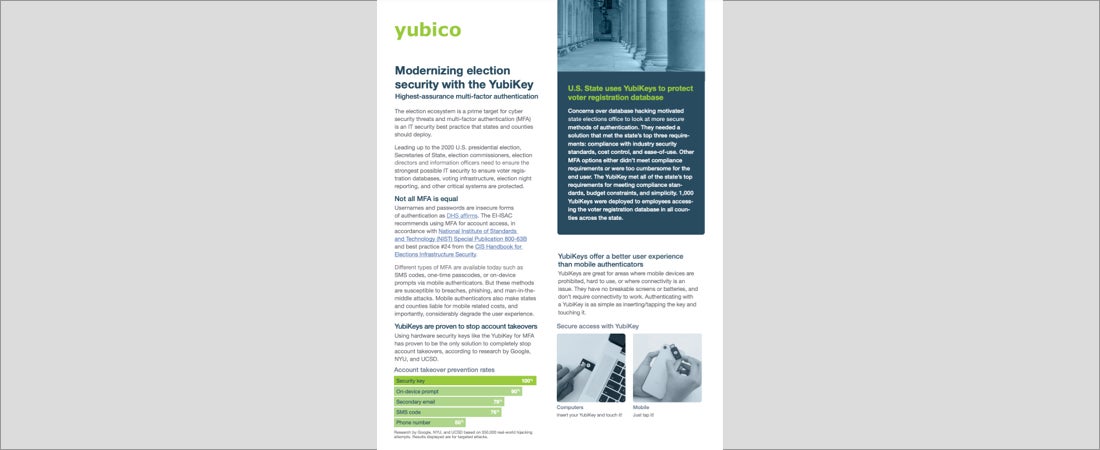
Modernizing election security with the YubiKey The election ecosystem is a prime target for cyber security threats. Read more