Blog
Stay up to date on company and partner news, product tips, and industry trends.
-

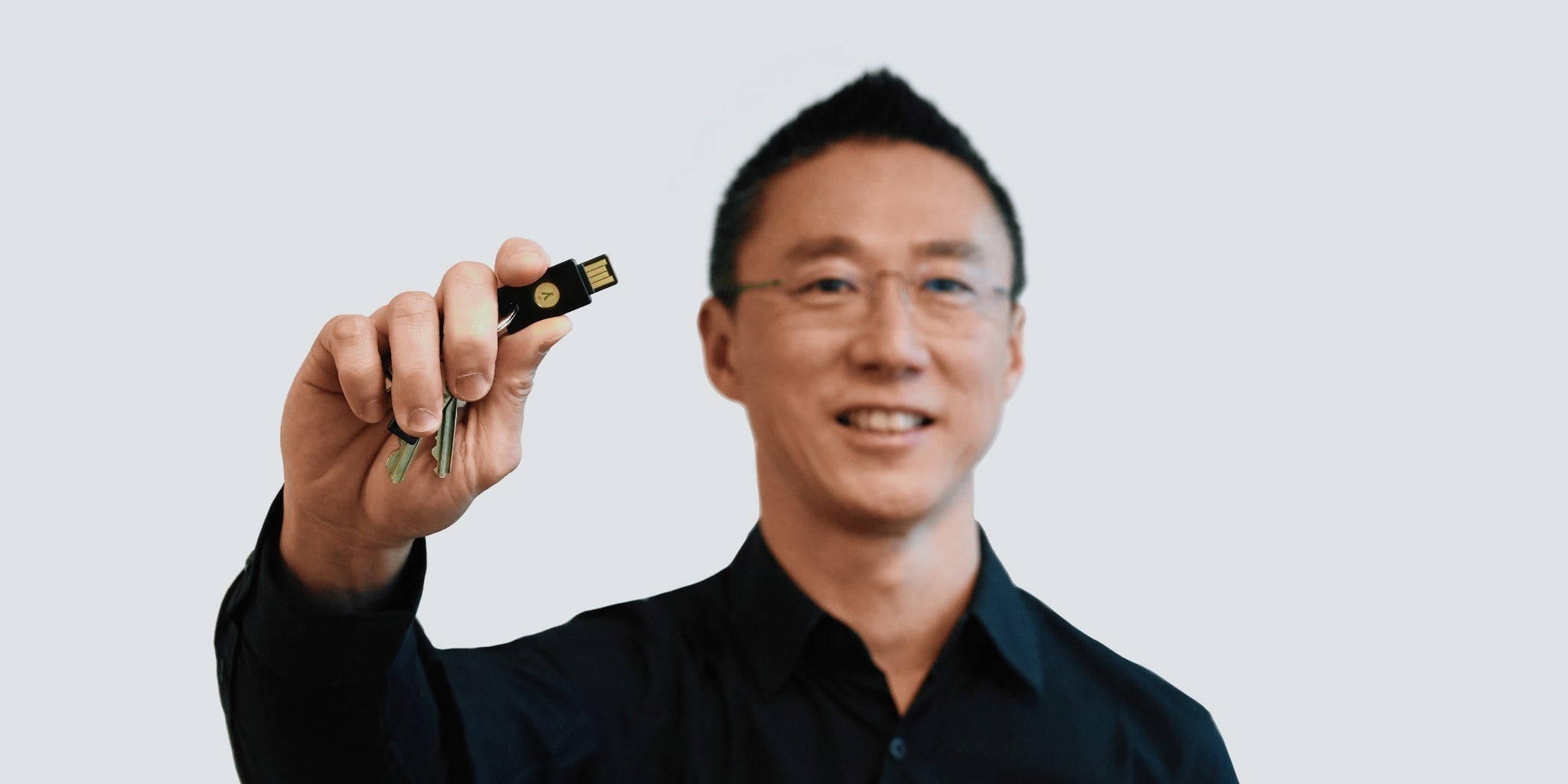
Yubico officially lands in Singapore: Opening our third global headquarters This week, we officially cut the ribbon on Yubico’s new Singapore office, marking a major milestone in our mission to secure digital identities worldwide. Joining Stockholm and Santa Clara, USA, Singapore now serves as our third global headquarters and a dedicated hub for the Asia Pacific region. As AI-driven cyber threats and sophisticated phishing attacks […] Read more -

Welcome to YubiNation Partners: Reimagining the Future of Channel Partnership to Secure Identity at Scale The cybersecurity landscape isn’t just changing; it’s being rewritten by AI. With the average cost of a breach hitting $4.4M, and phishing remains the primary threat, the industry can no longer rely on legacy MFA. Today, we are thrilled to officially unveil YubiNation Partners. This isn’t just a new name for a global Channel program; […] Read more -

Yubico’s Clifton Slater recognized as a CRN 2026 Channel Chief As the industry continues working together to combat evolving cyber threats like AI-driven phishing attacks, Yubico is committed to a channel-first approach and continued focus in growing a robust global partner network. In alignment with these efforts, we are thrilled to announce that Clifton Slater, Yubico’s VP, Channels, Americas, has been recognized on CRN’s prestigious […] Read more -
Leading Yubico into the Future: 2025 Reflections and Our 2026 Roadmap As we close the chapter on an eventful 2025, I find myself both grateful and honored to step into the role of Acting CEO. Having been part of the Yubico journey for over 12 years – most recently as President and COO – I have witnessed firsthand that our success is deeply rooted in a […] Read more -

Fireside chat: Meet Yubico’s new acting CEO, Jerrod Chong After more than 12 years at Yubico – most recently serving as president and COO – Jerrod Chong recently stepped into the role of Yubico’s acting CEO as the company enters its most exciting phase yet. Having worked across every facet of the business and the wider identity ecosystem, Jerrod is passionate in realizing Yubico’s […] Read more -

Yubico will introduce secure and privacy capable passkey enabled digital signatures in upcoming 5.8 firmware We are introducing what we consider to be one of the most significant updates to the modern authentication ecosystem. Yubico co-created the FIDO passkeys standards and we were first to market with a passkey supported Security Key back in 2018. Now, with the signing extension preview, Yubico is leading the way by making passkeys and […] Read more -

The 265% ROI of phishing resistance with Yubico: Why modern enterprises are ditching legacy MFA for YubiKeys For years, we’ve been told that “any MFA is better than no MFA.” While this still holds true, generative AI and sophisticated deepfakes are rapidly evolving the threat landscape, making it even more important than ever for enterprises to modernize their approach to security. Today, legacy multi-factor authentication (MFA) – like one-time password (OTP) SMS […] Read more -
AI overload? A CISO’s perspective At the beginning of every year, I aim to write something forward-looking based on my experiences as a CISO – reflecting on the past year and what I expect to unfold in the year ahead. What I write about is often a reflection of my expectations for the coming year(s) and what I know my […] Read more -

Say hello to seamless YubiKey deployments: Introducing Self-Service YubiKey ordering for workforces, enabled with a new Customer Portal As the cyber threat landscape continues evolving with AI-driven phishing attacks, enterprises need seamless access to identity security that can’t be socially engineered, intercepted or bypassed. Having the ability to get phishing-resistant YubiKeys into employees’ hands quickly and cost effectively – without adding burden to IT departments – is critical, and we’re committed to helping […] Read more