Build a phishing-resistant business in the passkey age
80% of breaches start with a stolen password. While legacy MFA is vulnerable, YubiKeys offer unshakeable, hardware-backed protection.
It’s time to go passwordless and stay secure.
Passwords are your biggest liability
Passwords account for 91% of organizational authentication but offer weak security and high costs.

43% of All Cyberattacks in 2023 Targeted SMBs
Modern AI phishing kits can bypass passwords and other legacy MFA in seconds.

95% of Cybersecurity Incidents Can Be Attributed to Human Error
One accidental click on a bad link can expose your entire network.

The Average Cost of a Cyber Attack on a SMB is $254,445
Some incidents cost up to $7 million. 60% of small businesses that suffer a cyberattack shut down within six months.
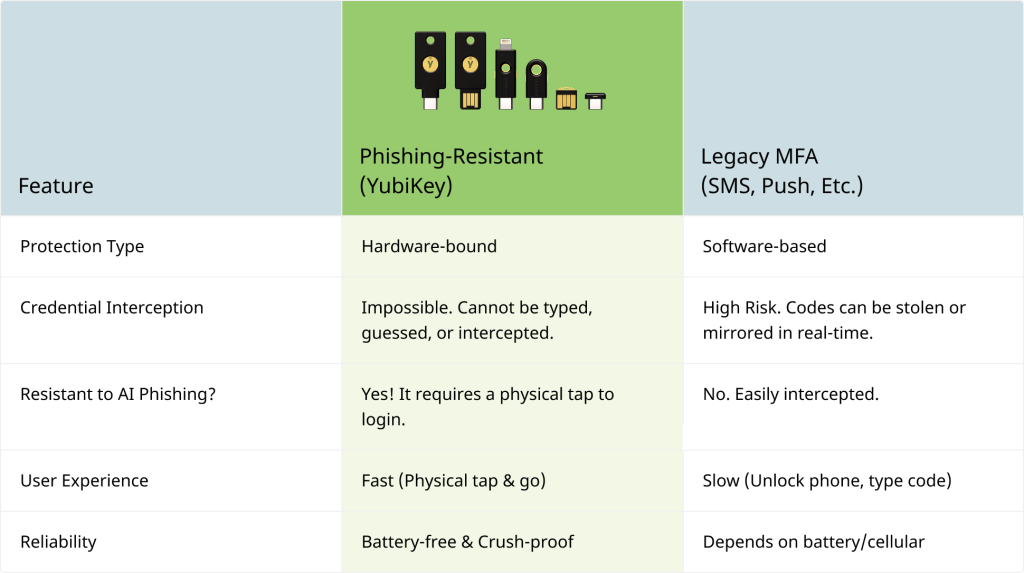
The shift to phishing-resistance: moving beyond legacy MFA
To build a truly resilient business, you must transition from “Legacy MFA” (which relies on interceptable codes) to “Phishing-Resistant MFA.” By using hardware-bound passkeys, you ensure that even if an employee is tricked into clicking a malicious link, your accounts remain uncompromisable.
YubiKey: The essential tool for your security toolbox
Trusted by the world’s largest brands, YubiKeys are the gold standard in phishing-resistant authentication, bridging the gap between legacy systems and a passwordless future.

Phishing-Resistant Security
Requires a physical tap to login, stopping 99.99% of credential-related breaches.
Works with what you use
Microsoft 365, Google Workspace, Okta, and hundreds more.

FIDO2 and WebAuthn Standards
Every key supports the latest in modern authentication, with additional protocols available for specialized security needs.
Better User Experience
Log in four times faster and never click ‘Forgot Password’ again. Just a simple tap and you’re in.
YubiKey protects the world’s leading brands

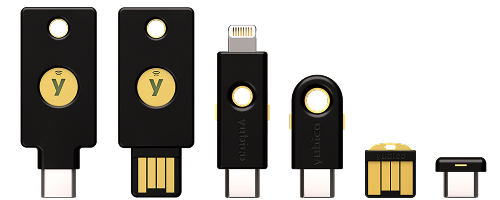
Which key is right for us?
| Feature | Security Key Series | 5 Series | Bio Series |
| Best For | Essential cloud protection | Advanced compatibility | Biometric authentication |
| Key Benefit | Affordable: Essential security at scale | Versatile: Our most diverse, all-in-one lineup. | Frictionless: Replaces PINs with a fingerprint |
| Protocols | FIDO2 (WebAuthn), FIDO U2F | FIDO2, FIDO U2F, Smart Card (PIV), OTP, OpenPGP | FIDO2 (WebAuthn), FIDO U2F |
| Volume Discounts | Yes | Yes | Yes |
| Starting at | $29 | $58 | $98 |
| Shop now | Shop now | Shop now |

Two Key Strategy
We recommend two keys per user: one primary and one backup stored securely. It’s the same way we stay secure at Yubico.
3 Steps to Get Started

Inventory
Identify your team’s port needs (USB-A vs. USB-C).

Pilot
Secure your “Admin” accounts first (Email, Registrar, Financials).

Register
Have employees register their primary and backup keys at the same time.


Sources
IBM, 2022 Cost of Data Breach Report
Forrester, 2026, The Total Economic Impact™ Of Yubico YubiKeys
BD Emerson, Must-Know Small Business Cybersecurity Statistics for 2025
Infosecurity Magazine, How to Understand and Adapt to Modern Cyber Threats
CNBC, Family offices become prime targets for cyber hacks and ransomware