Embracing for the next evolution of PCI DSS
The PCI Security Standards Council (SSC) publishes the PCI Data Security Standard (DSS). The PCI SCC continues to demonstrate investment and expertise as they enhanced the core 4.0 standard with a 4.0.1 update. PCI DSS holds organizations accountable around the world for implementing higher levels of cybersecurity to safeguard sensitive information and the payment ecosystem—impacting all industries.
Organizations collect a treasure trove of payment card data (PCI) as well as employee and customer identifiable information (PII) which necessitates stronger cybersecurity practices, starting with authentication. In fact, 90% of all cyber breaches are due to the theft of login credentials, passwords or other weak authentication methods.1 While any form of multi-factor authentication (MFA) provides significant advantages over traditional username and password, some methods are more effective than others. Legacy mobile-based authentication such as SMS, OTP and push notification apps are not phishing resistant and create costly downtime risk for organizations. Not all MFA is created equal.
How PCI DSS 4.0.1 defines MFA
The language specifically references FIDO Alliance when choosing authentication factors and National Institute of Standards and Technology (NIST) Special Publication (SP) 800-63 on phishing-resistant MFA stating that all MFA processes using shared secrets are vulnerable to phishing attacks—including: passwords, security questions, mobile-based authentication (SMS) and magnetic stripe cards. According to NIST SP 800-63-B4 only two forms of authentication currently meet the mark for phishing-resistant MFA: Smart Card/PIV and FIDO2/WebAuthn.
Specifically within v4.0.1:
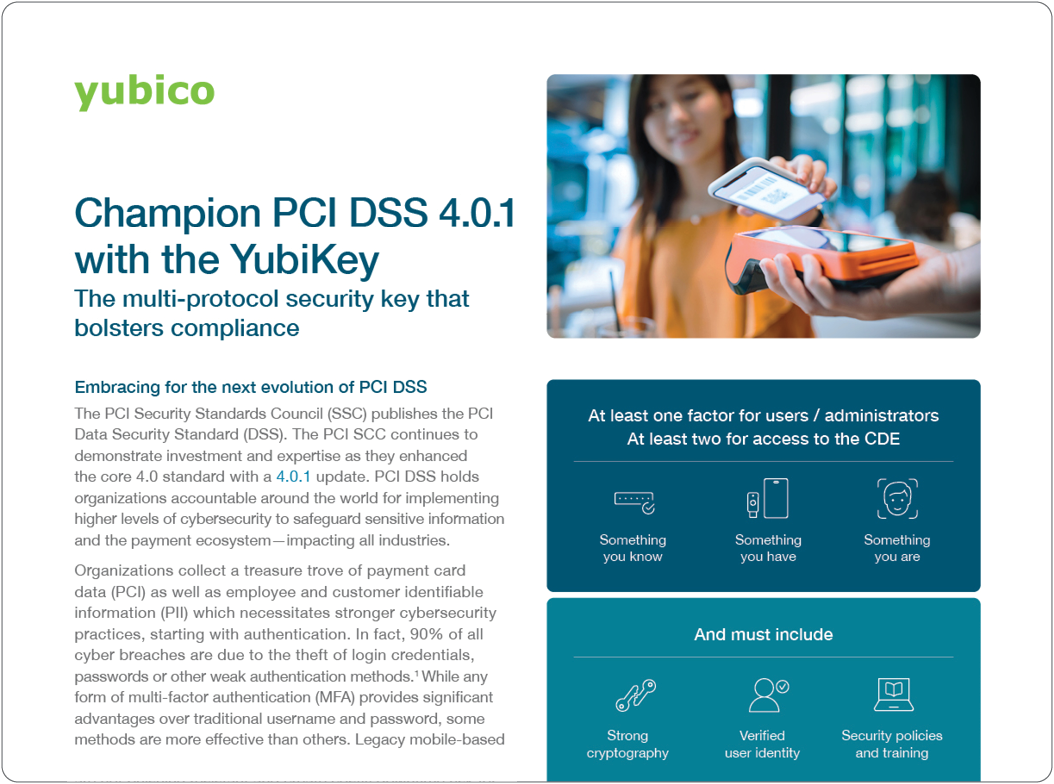
- Requirement 8.X enhances MFA requirements to include at least one factor for users and administrators and at least two factors of MFA for all access into the cardholder data environment (CDE) and related systems.
- Requirement 12.X details the need to focus on user experience that encourages the ease of use of MFA while focusing on user training and education.
At least one factor for users / administrators
At least two for access to the CDE

Something you know

Something you have

Something you are
And must include

Strong cryptography

Verified user identity

Security policies and training
The MFA system must meet minimum requirements

Resistant to attack

Cannot be bypassed
What this means for your authentication strategy
The weaker your MFA posture, the greater your compliance burden: longer policies, more user training, and more controls to manage risk. The solution: apply strong phishingresistant MFA, passwordless to all users. With AI-driven phishing attacks, QR code phishing attacks (Quishing) and other social engineering attacks, it necessitates the need for phishing-resistant authentication to address the evolving sophisticated threat landscape.
Protect your organization with the high-assurance YubiKey to bolster your PCI DSS 4.0.1 strategy
The YubiKey is a modern hardware security key that offers phishing-resistant multi-factor and passwordless authentication providing authentication that moves with users, and is highly suitable to secure payment services within all industries (financial services, retail and hospitality, healthcare, telcos, and more) as well as secure a wide range of scenarios:

Why choose the YubiKey for phishing-resistant authentication?
- With the YubiKey deploy the most secure passkey strategy: device-bound that is purpose-built for security, FIPS 140-2 validated and Authenticator Assurance Level 3 (AAL3) compliant
- Bridge to modern passwordless with multi-protocol support for Smart Card/PIV, FIDO2/WebAuthn, FIDO U2F, and OTP on a single key
- Cultivate phishing-resistant users, all the way from registering new employees on new devices, to daily authentication tasks, and even through account recovery processes
- Login without a password using phishing-resistant FIDO2 authentication to provide the strongest level of protection with the YubiKey-you can’t compromise what you don’t have
- Reduce risk of credential theft by 99.99% and stops account takeovers while delivering 265% ROI2
- Provide secure user access at scale on any device with the best user experience
- Drive business continuity, satisfy cyber insurance and regulatory requirements
- Ensure that any remote cyberattack will be unsuccessful because the YubiKey enforces human presence as a requirement when submitting credentials for authentication
Get started today and seamlessly deploy YubiKeys
With YubiKey as a Service, organizations can benefit from simple and scalable global deployments of YubiKeys for their workforce, supply chain, and end customers. YubiKey as a Service offers customers a choice of form factors, replacement stock, and priority customer support, all for less than the price of a cup of coffee per month.
Enrollment and Delivery services that help IT get users quickly onboarded with YubiKeys to fast track to phishing-resistance and then get YubiKeys to end users across the world, including corporate and residential addresses. Users can even experience self-service ordering of YubiKeys, giving them the freedom to have the keys shipped to their preferred address anytime they need. YubiKey as a Service customers receive continual enhancements to available and new services assuring a smart and future-proofed security investment.
At Yubico we meet you where you are on your cybersecurity journey and bolster your compliance posture to meet the needs of today and into the future.
“Instead of YubiKey being a highly recommended solution for our clients, we’re moving towards making them a required solution. We are building it into our hosting suite, and into our user fees.”